-
Tweets58K
-
Followers40K
-
Following8
-
Likes510
As long as AI systems are trained to reproduce human-generated data (e.g. text) and have no search/planning/reasoning capability, performance will saturate below or around human level. Furthermore, the amount of trials needed to reach that level will be far larger than the…
As long as AI systems are trained to reproduce human-generated data (e.g. text) and have no search/planning/reasoning capability, performance will saturate below or around human level. Furthermore, the amount of trials needed to reach that level will be far larger than the…
How to use AI / LLM in incident response: security.googleblog.com/2024/04/accele… Yes it makes our job really faster. I am glad it can be shared, so folks can take it as inspiration where AI is potentially useful. Kudos to all people involved, the authors of the post and the whole team.
I'm not sure it's fair to blame Microsoft if the national security risks of their monopoly have been known for 20+ years: "CyberInsecurity: The Cost of Monopoly How the Dominance of Microsoft's Products Poses a Risk to Security" (2003) schneier.com/essays/archive…
I'm not sure it's fair to blame Microsoft if the national security risks of their monopoly have been known for 20+ years: "CyberInsecurity: The Cost of Monopoly How the Dominance of Microsoft's Products Poses a Risk to Security" (2003) schneier.com/essays/archive…
There is little evil in the world; rather there is lots of stupidity and selfishness that gets interpreted as evil.
This software supply chain attack vector is worth knowing about:
On the surface, the rise in workplace burnout makes no sense. Despite choosing our hours, working where we want and taking meetings in our underwear, we're suffering burnout more than ever. Are we just whiny & weak, or is there something deeper going on? Let’s investigate👇
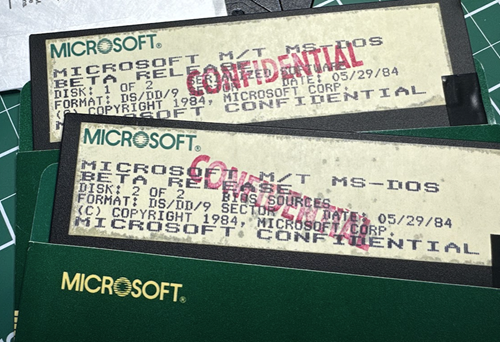
Microsoft just open-sourced DOS 4 hanselman.com/blog/open-sour… (as well a release of beta binaries, disk images, and PDFs from @rozzie's archives!) (but who did the PR?!)
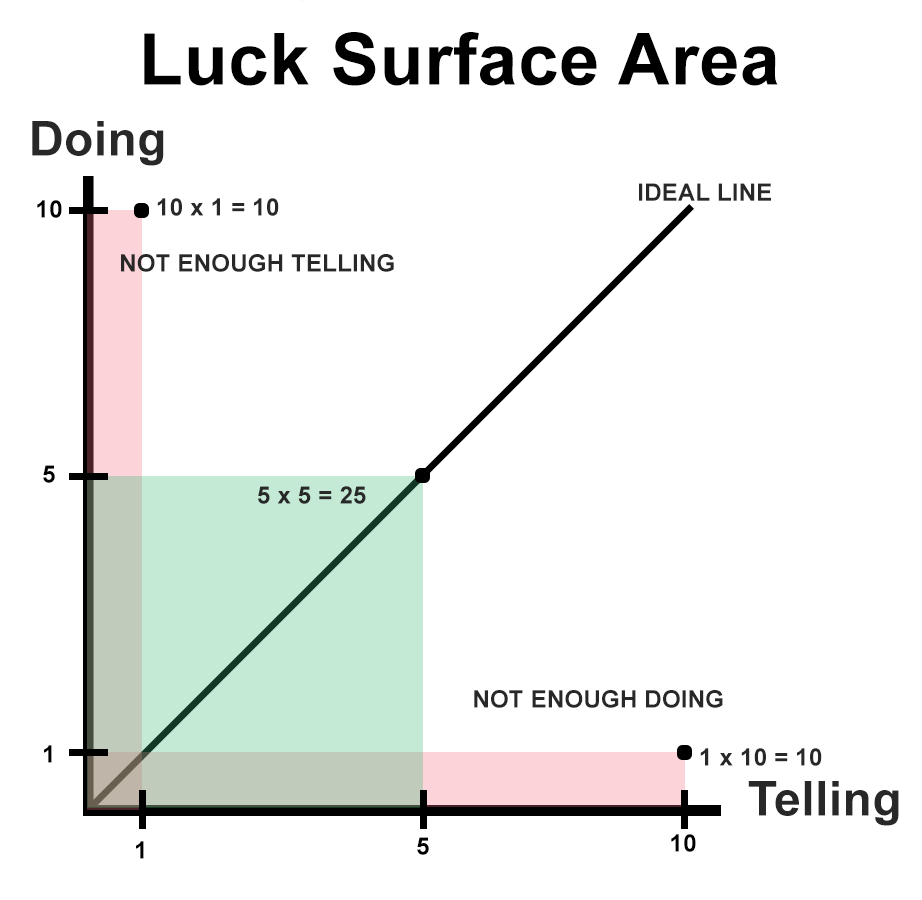
"The amount of serendipity that will occur in your life is directly proportional to the degree to which you do something you're passionate about combined with the total number of people to whom this is effectively communicated."
In 1984, Ken Thompson had the best take on software supply chain security: "The moral is obvious. You can't trust code that you did not totally create yourself. No amount of source-level verification or scrutiny will protect you from using untrusted code." dl.acm.org/doi/10.1145/35…
Ten Laws of Security and their Security Implications. 3.Conway’s Law. Org affects the nature of the products you deliver and also shapes how you do risk governance and embedded security functions. Optimize to avoid dysfunction. philvenables.com/post/security-…
No one buys books "The DOJ’s lawyer collected data on 58,000 titles published in a year and discovered that 90 percent of them sold fewer than 2,000 copies and 50 percent sold less than a dozen copies."
Only half of CISA's 2023 warnings to critical infrastructure organizations that their internet-connected devices had vulnerabilities commonly used in ransomware attacks resulted in fixes or mitigations, per newly published data. cisa.gov/news-events/ne…
This is just a month after the VPN bypass bug I found on the same Cisco ASA/Firewall device (CVE-2024-20337). For everyone asking me why not release a PoC: its bc it's a very dangerous bug. Just on shodan, you can see 178k different organizations use this device. It just requires…
This is just a month after the VPN bypass bug I found on the same Cisco ASA/Firewall device (CVE-2024-20337). For everyone asking me why not release a PoC: its bc it's a very dangerous bug. Just on shodan, you can see 178k different organizations use this device. It just requires…
NEW: An ex-NSA hacker and an ex-Apple researcher are launching a startup with the goal of helping other companies make better security products for iOS and macOS. They’ll make modules, like monitoring network flow, that can be plugged into other tools. techcrunch.com/2024/04/25/ex-…
This is the way, and why Nix is the future. LTS is expensive tech debt you pay for twice.
This is the way, and why Nix is the future. LTS is expensive tech debt you pay for twice.
Nix 2.22.0 is here! Dive into the full announcement and release notes to discover the latest enhancements and features: buff.ly/3UmEhUm
Challenge accepted. We've seen Nix make teams happier and more productive. With the right tooling (see @jetify_com, @Replit, and others) Nix can empower developers without the painful learning curve.
Challenge accepted. We've seen Nix make teams happier and more productive. With the right tooling (see @jetify_com, @Replit, and others) Nix can empower developers without the painful learning curve.
The dataset is everything. Great read: nonint.com/2023/06/10/the…
Just landed back in good old USA from a visit to Dubai. Working on improving Zcash—the completely decentralized, self-sovereign currency. There are a lot of other people improving Zcash too, known and unknown. Because privacy is normal, and is necessary for a healthy society.

thaddeus e. grugq the.. @thegrugq
129K Followers 423 Following Hacker :: https://t.co/km8BR8E1Ga :: [email protected] :: PGP https://t.co/dYipV8y3bo :: @warstudies :: https://t.co/H3dWknFCfk :: https://t.co/Z2lWqEVVua
Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Brendan Dolan-Gavitt @moyix
25K Followers 6K Following Associate Professor @ NYU Tandon. Security, RE, ML. PGP https://t.co/3WXr0RfRkv Founder of the MESS Lab: https://t.co/zGycrX3Gmn "an orc smiling into the camera" — CLIP
Daniel Cuthbert @dcuthbert
30K Followers 1K Following Documentary photographer, old creaky hacker. Co-author of @OWASP ASVS standard. Blackhat/Brucon Review Board & UK Government Cyber Security Advisory Board
Greg Linares (Laughin.. @Laughing_Mantis
29K Followers 2K Following 20+ yrs in Infosec. Cybergoth. Musician. Autistic. Art @MalwareArt. 4x Pwnie Nominee. Red Teamer. 𝕍𝕏. Chronic Illness Fighter. I love Smite, Gamedev & Synths
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
Kim Zetter @KimZetter
95K Followers 3K Following Journalist - cyber/national security. Author - COUNTDOWN TO ZERO DAY: Stuxnet and the Launch of the World's First Digital Weapon. https://t.co/334DzfSL1f
mdowd @mdowd
32K Followers 744 Following Internet Hacker. Founder of @vigilant_labs. Previously, co-founder of Azimuth Security (now L3Harris Trenchant)
cje @caseyjohnellis
29K Followers 4K Following founder/chief strategy officer @bugcrowd && co-founder @disclose_io || pioneer of crowdsourced security as-a-service
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
haroon meer @haroonmeer
17K Followers 3K Following Security Geek at Thinkst. We build https://t.co/Sv6Gp3sG6b
Clint Gibler @clintgibler
19K Followers 575 Following 🗡️ Head of Security Research @semgrep 📚 Creator of https://t.co/xwtIAI0CuJ newsletter
Weld Pond | Chris Wys.. @WeldPond
57K Followers 1K Following Hacker. Co-founder/CTO Veracode. Former L0pht security researcher. GenAI Auto-repair of vulns is the future @[email protected]
Mudge @dotMudge
67K Followers 343 Following Make a dent in the universe. Find something that needs improvement: go there and fix things. If not you, then who? {he/they}
Filippo Valsorda @fil.. @FiloSottile
49K Followers 508 Following Cryptogopher / Go crypto maintainer / @kateconger-knower / RC F'13, F2'17 / #BlackLivesMatter / he+him https://t.co/ZE4RtJ1xqD / https://t.co/qfth7zr00W / https://t.co/j1grpEm8uR
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Jack Daniel is over t.. @jack_daniel
62K Followers 3K Following Storyteller, wanderer, comic, historian, world’s oldest millennial. I used to do stuff, now I do other stuff. @[email protected]
Holber @HolberMallowe
118 Followers 5K Following
Thanks Always @iTimonPumbaa
2 Followers 368 Following
Peter Clark @al_saeroth
132 Followers 476 Following R&D Cybersecurity @SandiaLabs, PhD @IowaStateU. CTI + deterrence, interested in RE. KD0LMF. Tweets my own; likes+RT neq endorsements.
Noncomodegenic_quartz.. @NQuartzite16385
0 Followers 4K Following High follow:follower ratio screws up your reach
Fighter001 @Fighter00192814
21 Followers 256 Following
₿itcoin Roth₿ard @BitcoinRothbard
19K Followers 10K Following Libertarian / ancap Bitcoiner working to spread the message of liberty, free markets, and sound money. Bitcoin Realist. Austrian economics. #Bitcoin
Pietro Peterlongo @pietroppeter
509 Followers 1K Following Recursing at https://t.co/0kuxrKz5Lj, previously Data Scientist & Software Engineer @ToolsGroup. #python #nim #... @[email protected] 🐘 he/him
freakyclown @_Freakyclown_
16K Followers 3K Following Co-Founder of @CygentaHQ former head of cyber research @Raytheon - Keynote Speaker, ethical hacker and physical security specialist. Author of How I Rob Banks.
Youssef @YoussefO526
20 Followers 36 Following
Brian in Pittsburgh @arekfurt
6K Followers 772 Following Former attorney, current IT & infosec consultant in the 'Burgh. Happy to talk about password spraying one minute and constitutional law the next. Son of #wvu.
Emilio Mantt @EmilioMant99600
11 Followers 51 Following
end1an @end1an
69 Followers 1K Following
...logogriph @logogriph
57 Followers 1K Following
parsa @_Parsa_kv_
9 Followers 2K Following
JASIK MJ @JASIK_MJ
52 Followers 521 Following New to Bug Hunting | When time becomes treasure, and determination serves as currency. Consistency is the key
Johnny Evans @johnnyevans811
193 Followers 3K Following 𝙶𝚢𝚖 + 𝙲𝚛𝚢𝚙𝚝𝚘 Just a Day Trader helping thousands of traders around the world achieve their goals 🥶📊
Weight Loss | Nutriti.. @FITNESS3M_
4K Followers 3K Following Weight Loss | Nutrition | Workout - Follow for tips to achieve your dream body Quickly - DM For shredding Pounds Faster Now.
Ricky-SwingMan-Jr @RickySwingMan
158 Followers 466 Following Waterman • Road-Cycling• Cloud Systems/Security Engineer• Investing • Dad
CryptoTicky @TickyCrypto
176 Followers 703 Following Whitehat @Immunefi | Smart Contract Engineer & Auditor| Lending & Borrowing, AMM, Yield aggregator, NFT Guardians of @GMX_IO and eBTC (@BadgerDAO)
Corey Anderson @anderson_c19198
205 Followers 3K Following Always protecting people's rights and freedoms for the corrupt people who serve us.
Bentley Hall @BentleyhallLtd
46 Followers 283 Following Turnaround Pluralist in Cyber security, App development, and fraud prevention.
Fəqan Əkbərli @fekan_ekberli
15 Followers 176 Following
Rijabul Islam @RijabulIsl48386
0 Followers 17 Following
JP Aumasson @vt_0_
288 Followers 205 Following aka @veorq cofounder & CSO @taurus_hq author of https://t.co/8Bbd6vuHic Signal: jpa.01
production @product9755299
12 Followers 55 Following Amazon公式アカウント 皆様への感謝を胸に、これからも笑顔をお届けしてまいります。新サービスや新製品、日々の生活を便利で豊かにする情報そしてAmazonの取り組みなどをご紹介していきます ニュースアカウント → @AmazonNewsJP お問い合わせやサポート → @AmazonHelp が24時間行っております
Patto @patto75
79 Followers 220 Following
borski 🇺🇦 ✡�.. @borski
742 Followers 564 Following hacker | founder | cybersecurity expert | angel investor | singer/musician | UX enthusiast
Arthur Wiedmer @awiedmer
591 Followers 4K Following Data, Privacy, Python, Airflow, free software. My opinions are my own.
fethallah ghellaimi @FGhellaimi
2 Followers 93 Following Ingénieur en informatique bien tôt. 💻 Les mathématiques. π Volley ball 🏐
Mm @Mm05646882
80 Followers 2K Following
stevesnewday @stevesnewday
5 Followers 51 Following
Joe35290384134 @joe352903879563
15 Followers 64 Following
ThirdpartyMichelle @ThirdpartyM
0 Followers 84 Following
Farzam Noori @FarzamNoori1
9 Followers 200 Following Before you act, listen. Before you react, think. Before you criticize, wait. Before you quit, try.
roundjam-tech @RoundjamT
62 Followers 537 Following A creative coder and system engineer. Born in Nagaoka of Niigata pref. Finally now in Sapporo Japan. Network Infrastructure . More general topic @roundjam
Marshall Jaquish @marshallposts
143 Followers 427 Following CISO, tech and security strategy for startups and mid-stage.
Anna Lise 👩💻 @ann3dev
15K Followers 6K Following Front-End Developer at @amazon | Crafting websites with HTML, CSS, React.js and JavaScript
Yuvaraj | uvvirus(.le.. @UV_virus
234 Followers 2K Following Hacker | ETHIndia2022🥇 polygon track winner🏆 | Learning Web3Security @TheSecureum | Passed @SpearbitDAO Exam | Web3 security | Digital forensics | #cybersec
lucky @lucky5502118041
0 Followers 166 Following
NixOS @nixos_org
10K Followers 89 Following
Bitkey @Bitkeyofficial
5K Followers 2 Following Bitkey is the self-custody bitcoin wallet with an app, hardware, and recovery tools. Built by the Proto team at Block, Inc.
Spiral @spiralbtc
104K Followers 1 Following Making bitcoin more than an investment. Nostr: npub1spralxq6jlw5rdy0249vqr5sh43rfrlx2wzv3rhjjqedw559w9psrs8s72
Block @blocks
89K Followers 8 Following Building blocks @Square @CashApp @spiralbtc @TIDAL @TBD54566975
Square @Square
314K Followers 1K Following Powering all the ways you do business. #PoweredBySquare ⚡️
TBD @TBD54566975
71K Followers 0 Following Making a decentralized world accessible to all | Join @TBDevs, build open source tech to return ownership & control over our finances, data, identity #BTC #Web5
Cash App @CashApp
2.1M Followers 0 Following $ send $ spend $ bank $ invest $ Debit cards issued by Sutton Bank. Disclosures: https://t.co/GtBoXGO6df, https://t.co/tGNe0ur4YyGet the best of both worlds in Common Lisp? Interactive & incremental development always. Dynamic types when you want to prototype. Static types when you want performance and reliability.
A lot of people would get along great if they used a scripting language for design and a compiled language for their core, tbh.
As long as AI systems are trained to reproduce human-generated data (e.g. text) and have no search/planning/reasoning capability, performance will saturate below or around human level. Furthermore, the amount of trials needed to reach that level will be far larger than the…
Interesting how in all these domains AI is asymptoting at roughly human performance - where's the AI zooming past us to superintelligence that Kurzweil etc. predicted/feared?
Today is my birthday and I was reflecting on my 26 years career in infosec. One of the things that I am most proud in my life, not only in my career, is that I collaborated with people for years, decades even. Cross company, cross social statuses, cross any other fake barrier. I…
I'd rather do what's right and lose followers than remain silent about (AKA, complicit in) atrocities. I've collected plenty of blood on my hands "staying in my lane." I won't be silent now. Your discomfort with my posts says more about you than me.
Every field being optional in Protobufs is actually the only scalable solution for schema migrations
On community in Nix, from our cofounder Eelco Dolstra: buff.ly/3wcFN3c
There is little evil in the world; rather there is lots of stupidity and selfishness that gets interpreted as evil.
On the surface, the rise in workplace burnout makes no sense. Despite choosing our hours, working where we want and taking meetings in our underwear, we're suffering burnout more than ever. Are we just whiny & weak, or is there something deeper going on? Let’s investigate👇
"The amount of serendipity that will occur in your life is directly proportional to the degree to which you do something you're passionate about combined with the total number of people to whom this is effectively communicated."
Thought experiment: In a microservice, allocating memory that survives past the end of you servicing the request should be *exceedingly* rare. This means that you should neither do explicit malloc/free *nor* traditional garbage collection. You should just have a bump allocator…
In 1984, Ken Thompson had the best take on software supply chain security: "The moral is obvious. You can't trust code that you did not totally create yourself. No amount of source-level verification or scrutiny will protect you from using untrusted code." dl.acm.org/doi/10.1145/35…
Ten Laws of Security and their Security Implications. 3.Conway’s Law. Org affects the nature of the products you deliver and also shapes how you do risk governance and embedded security functions. Optimize to avoid dysfunction. philvenables.com/post/security-…
NEW: An ex-NSA hacker and an ex-Apple researcher are launching a startup with the goal of helping other companies make better security products for iOS and macOS. They’ll make modules, like monitoring network flow, that can be plugged into other tools. techcrunch.com/2024/04/25/ex-…
@dinodaizovi I am still in awe of the design brilliance of those 70s NASA engineers. What they did in deep space with a bunch of discrete, decidely low-tech by modern standards, components was nothing short of miraculous.
Challenge accepted. We've seen Nix make teams happier and more productive. With the right tooling (see @jetify_com, @Replit, and others) Nix can empower developers without the painful learning curve.
I want nix to prove me wrong but there's like 99% chance all the nix based startup will fail. Nix is such an incredibly difficult sell. You either have people touch nix and have to 3x level up their skills or your abstract away nix so much that you could probably do without it
The dataset is everything. Great read: nonint.com/2023/06/10/the…
Just landed back in good old USA from a visit to Dubai. Working on improving Zcash—the completely decentralized, self-sovereign currency. There are a lot of other people improving Zcash too, known and unknown. Because privacy is normal, and is necessary for a healthy society.
Mercury retrograde is finally over. Now you need a better excuse for your over spending.