-
Tweets15K
-
Followers10K
-
Following2K
-
Likes18K
"how I hacked Google": dependency confusion observationsinsecurity.com/2024/04/25/how…
In 1984, Ken Thompson had the best take on software supply chain security: "The moral is obvious. You can't trust code that you did not totally create yourself. No amount of source-level verification or scrutiny will protect you from using untrusted code." dl.acm.org/doi/10.1145/35…
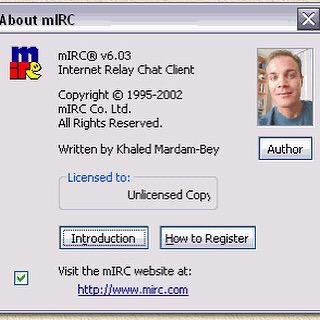
When I was around 12 yo, I was limited to assembly language and QBasic on DOS. Then I found probably a Borland C compiler (Turbo C?) and later Linux! where coding C was natural.
When I was around 12 yo, I was limited to assembly language and QBasic on DOS. Then I found probably a Borland C compiler (Turbo C?) and later Linux! where coding C was natural.
So with all the negative talk about Microsoft security recently it occurred to me it's interesting to remember that MS also achieved one of the most consequential security successes of the last decade. A success that no one--including MS--ever talks about. Hardening Office.
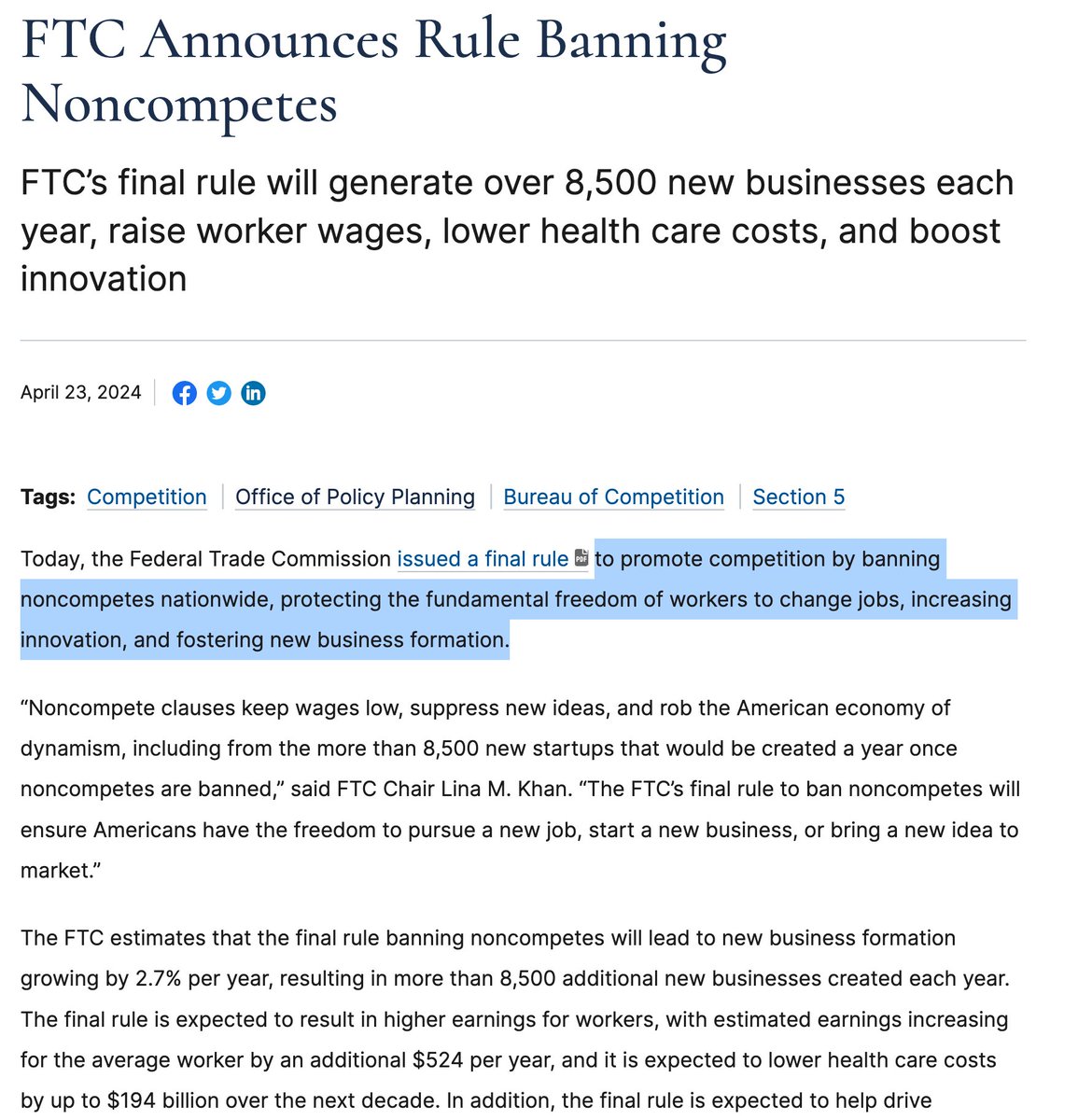
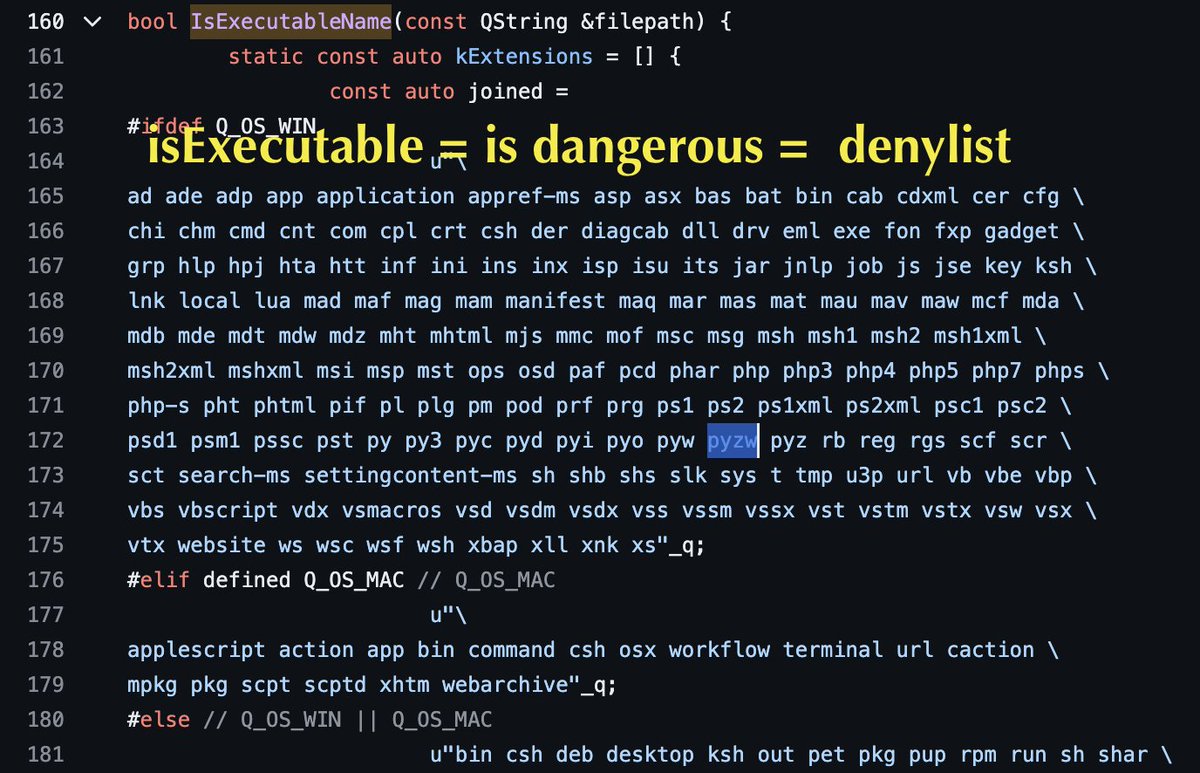
⚠️Telegram Desktop for Windows security vulnerability confirmed and fixed 🪲 RCE risk due to a typo in the executable and IP-revealing file extension list: 'pywz' instead of 'pyzw'. ❌ Relying on blacklists/denylists alone is risky. They can be incomplete or miss new extensions.
🎁🪱supply chain attacks: code review alone not enough. 🔧Continuous Integration best practices and auto vuln detection help. After removing the XZ backdoor, Lasse hardens CI: ➕UBSAN, Valgrind, persistent verbose logs, abort build on error Let's move beyond the "many eyes" 🤥
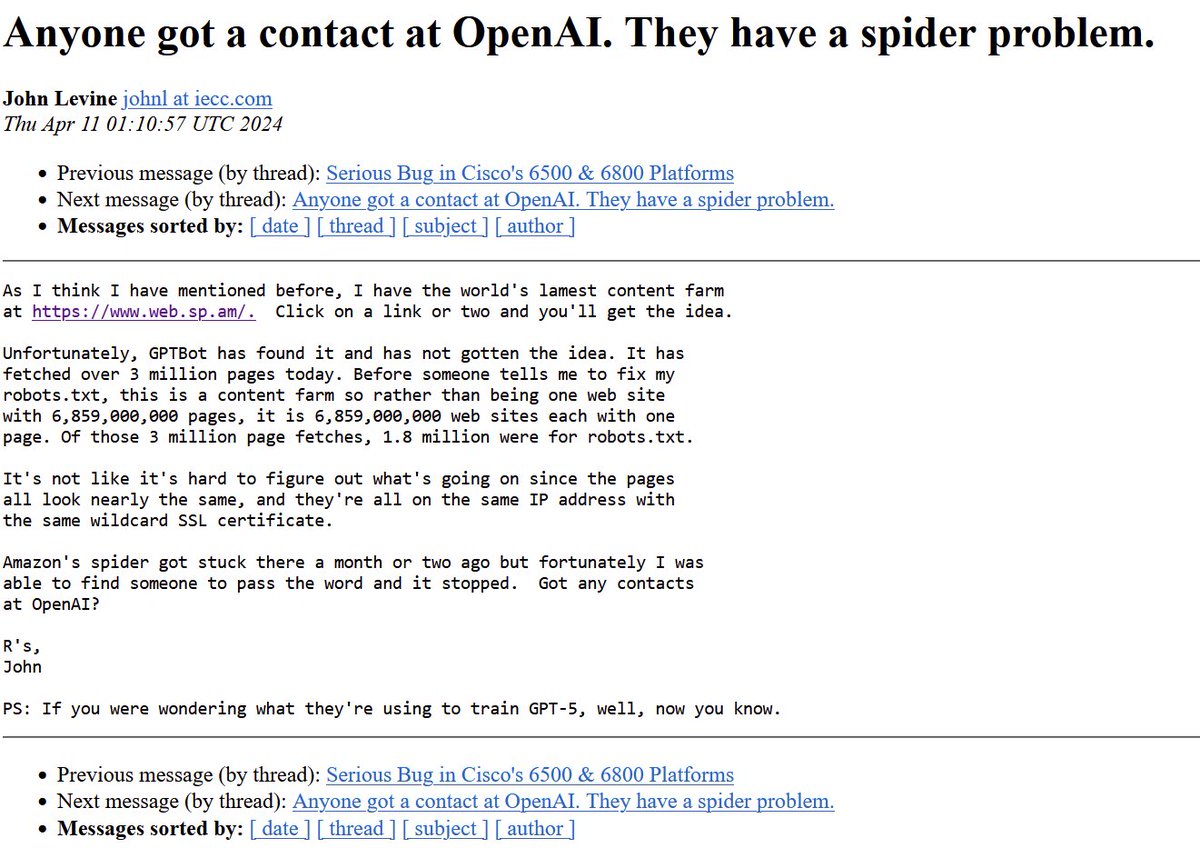
🔎Researchers are working hard but still need to conclude the XZ backdoor analysis and determine whether it has alternative communication channels or triggers. 🎁The xz-min project by @felipec is a way to easily reproduce the XZ backdoor to study it: github.com/felipec/xz-min
Last week, I lost a dear friend and ctf teammate, Quend. Every spring we all gather to comile together the best challenges we can for the @MidnightSunCTF qualifiers. The current HFS crew were all back together again this month getting things ready to launch
Massive data breach at SiSense - a business intelligence platform. Actors allegedly compromised network, exfiltrated data and could potentially contain customer data. Highly recommend if using SiSense, to look at the following: * Change passwords of any SiSense accounts…
CISA investigates critical infrastructure breach after Sisense hack bleepingcomputer.com/news/security/…
🚀 learn-evm-attacks V1 release is here! 🎉 Coinspect's #LearnEVMAttacks team: 👨🏭reproduced 40+ smart contract exploits with extensive docs, diagrams, and clear explanations. 💪contributed changes to Foundry to make the PoCs work. 🌐 github.com/coinspect/lear… 🙏 Thanks to all…
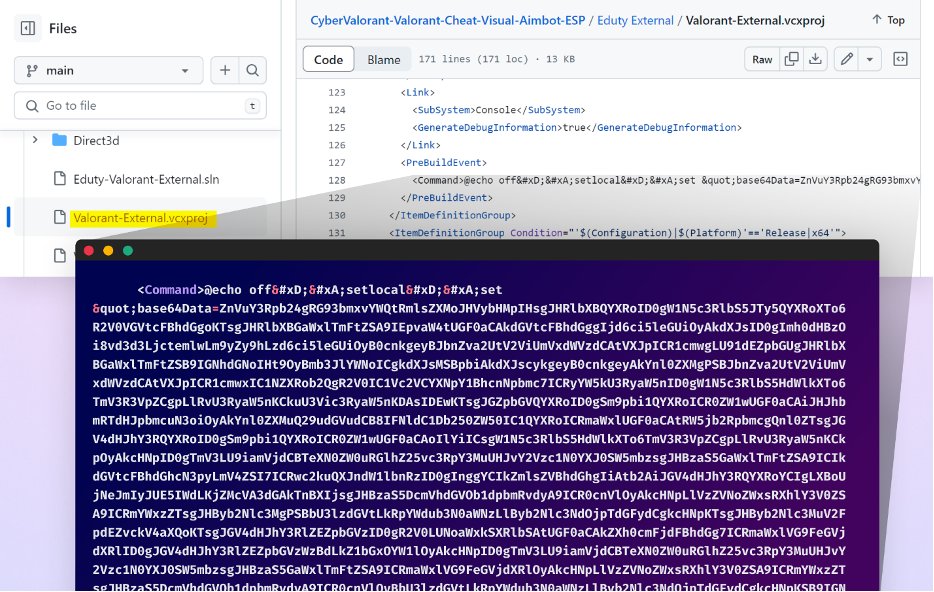
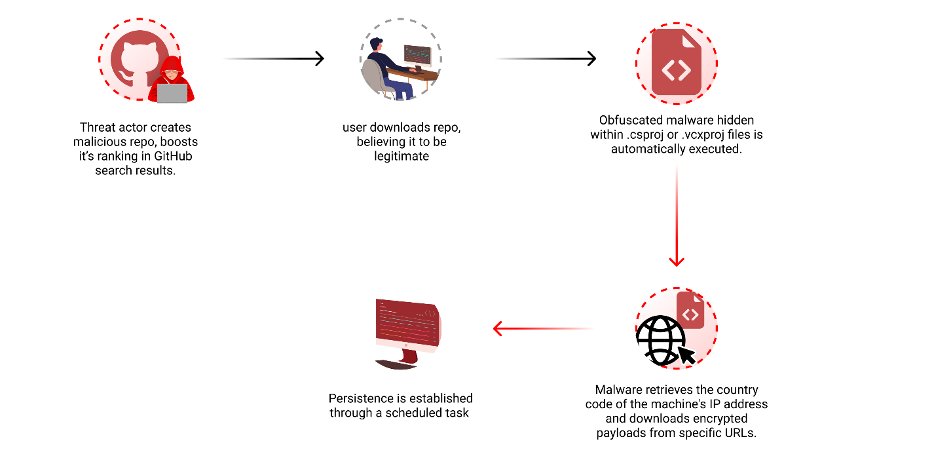
GitHub Search Sabotaged - Malware Hidden in Popular Repositories : checkmarx.com/blog/new-techn… The GitHub Black Market : Gaming the Star Ranking Game : medium.com/checkmarx-secu… How Attackers Manipulate Their GitHub Profiles to Deceive You — Part 1 : medium.com/checkmarx-secu… Part 2…
VW programmed cars to optimize for the wrong objective: reduced emissions only under test conditions. Are we creating AI with genuine integrity or just test-optimized behavior?
VW programmed cars to optimize for the wrong objective: reduced emissions only under test conditions. Are we creating AI with genuine integrity or just test-optimized behavior?
A new year, a new challenge: medium.com/@maor_s/a-new-…
Login with Google + Google Advanced Protection Program still better than password managers and phisheable 2FA. Passkey in the near future ...
Login with Google + Google Advanced Protection Program still better than password managers and phisheable 2FA. Passkey in the near future ...
Interesting info from UN Security Council +600 pages report on DPRK attacks: 👀How to identify North Korea "IT Workers" attack: 📸Unwillingness to appear on video calls 🤖Cheating on coding tests, incorrect but plausible answers 🎭Online profiles don't match resume, multiple…
Interesting info from UN Security Council +600 pages report on DPRK attacks: 👀How to identify North Korea "IT Workers" attack: 📸Unwillingness to appear on video calls 🤖Cheating on coding tests, incorrect but plausible answers 🎭Online profiles don't match resume, multiple…
I'm exploring Analytic Hierarchy Process (AHP) to improve security checklists. Have you tried it? linkedin.com/feed/update/ur…

Matthew Green @matthew_d_green
143K Followers 1K Following I teach cryptography at Johns Hopkins. Mastodon at [email protected] and BlueSky at https://t.co/GI4QlxYTdk.
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
thaddeus e. grugq the.. @thegrugq
129K Followers 423 Following Hacker :: https://t.co/km8BR8E1Ga :: [email protected] :: PGP https://t.co/dYipV8y3bo :: @warstudies :: https://t.co/H3dWknFCfk :: https://t.co/Z2lWqEVVua
Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
Daniel Cuthbert @dcuthbert
30K Followers 1K Following Documentary photographer, old creaky hacker. Co-author of @OWASP ASVS standard. Blackhat/Brucon Review Board & UK Government Cyber Security Advisory Board
Brendan Dolan-Gavitt @moyix
25K Followers 6K Following Associate Professor @ NYU Tandon. Security, RE, ML. PGP https://t.co/3WXr0RfRkv Founder of the MESS Lab: https://t.co/zGycrX3Gmn "an orc smiling into the camera" — CLIP
AIfredo Ortega @ortegaalfredo
8K Followers 950 Following Software Developer - Security researcher - Shape rotator - Cybergaucho - @[email protected] AI-related: https://t.co/hhQltrgzKS https://t.co/ibyCcAp6zv
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
Gareth Heyes \u2028 @garethheyes
32K Followers 1K Following JavaScript for hackers: Learn to think like a hacker. https://t.co/e0aNEbEDk5
Immunefi @immunefi
44K Followers 640 Following The leading bug bounty platform for blockchain with the world's largest bug bounties. More than $95m paid out to whitehats and $156m in rewards available.
runixo @runixo
8K Followers 4K Following computadoras, plantas y comida 💻🖥️🌲🌳🌴🦐🍍🥑🌶️🍇🍄🥗 en mastodon https://t.co/z9fRobNqtR
Sysarmy @sysarmy
27K Followers 2K Following El soporte de quienes dan soporte. // IT Community. Support for those who give support.
Nicolás Wolovick ⭐.. @nwolovick
4K Followers 1K Following HPC, CSEd, RC, FM. Votar en papel para defenderse de las computadoras.
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Filippo Valsorda @fil.. @FiloSottile
49K Followers 507 Following Cryptogopher / Go crypto maintainer / @kateconger-knower / RC F'13, F2'17 / #BlackLivesMatter / he+him https://t.co/ZE4RtJ1xqD / https://t.co/qfth7zr00W / https://t.co/j1grpEm8uR
DragonJAR - Seguridad.. @DragonJAR
289K Followers 3K Following Al 👉 seguirnos, te compartiremos información de calidad sobre #Hacking, Somos una empresa 🐲 👇 Colombiana de servicios en #SeguridadInformática
Santiago Palladino @smpalladino
11K Followers 955 Following 🇦🇷 Engineer at @aztecnetwork. Councilmember at @graphprotocol. Formerly @OpenZeppelin @manastech.
XLaBete.eth @XLaBete
5K Followers 6K Following Les #Algorithmes #X contrôlent ce compte & ce que vous voyez. La libre expression est en vente 🗽💵 #AdoptDontShop #Animals #Animaux
SherryHousman @qX6Agp8OSE910
64 Followers 1K Following
F70 @s0m3n4m30
28 Followers 158 Following
Kevin Mendoza @12F5C8D
5 Followers 64 Following
darkwebnews @darkwebint
49 Followers 139 Following
mrragava @mrragava
151 Followers 3K Following
Tzada 🐘 @marionlml
460 Followers 1K Following 🇬🇧🇫🇷 #InfoSec || #Audit || #RiskAssessment || #SupplierRelationship
white.liszt @WhiteLiszt
80 Followers 261 Following
qvinhprolol @qvinhprolol
18 Followers 270 Following
Ali Abdullah @A208_
75 Followers 393 Following
Jonatan Rodriguez @jotaerregv
6 Followers 192 Following
dtn9fgi9pi @hcj4oyhwoe
12 Followers 1K Following We first transfer USDT to you TRC20, you return 90% to BEP20, you get 10% , 2K per day Our co hv a large amt of USDT need to from TRC20 convert to BEP20 network
Jan Jakub Rychlicki @Co_Liber
75 Followers 1K Following Rock hard, ride free .... 💙 https://t.co/iKfB5blp9y Army
JiaTan @reenz0h
333 Followers 3K Following Hacktivist The chief enemy of good decision is the lack of sufficient perspective on a problem.
aliyu usman abdullahi @aleemaxxiss
67 Followers 403 Following
parsa @_Parsa_kv_
9 Followers 2K Following
Siavash @siavash_di
213 Followers 683 Following یه کلاه قرمز لینوکس باز در آمستردام 🇳🇱🚨 Co-founder | DevOps | Redhat engineer (RHCE) 🛡
Robert Lerelou @RLerelou
292 Followers 1K Following Big picture. #crypto #longterminvesting #hodl. Watching #AI #automation #robotics #futureofwork #privacy & #singularity
noe @nopucopc
45 Followers 890 Following
AJ King @ajkingio
185 Followers 699 Following Director of Threat Research @SnapAttackhq / Detection Engineering / Dad
christian cch @chris_cch_
189 Followers 3K Following
Nghi Vi @NghiVi1
22 Followers 104 Following
ferritox @ferritox
105 Followers 340 Following
Muhammad Hendro @hendro_jun
348 Followers 2K Following
𐁉 @01O101O0
30 Followers 68 Following
Yasin @0x56ee
6 Followers 168 Following
Nicolas Chatelain @Nicocha30
298 Followers 267 Following Senior security researcher | Ligolo/Ligolo-ng/Chashell author
Kevin E. Greene @iamkevtorious
1K Followers 3K Following Public Sector CTO - @opentext | One of my passions is cyber | my imagination is running wild!! | writer @Darkreading | podcast - https://t.co/wyezs68sCS
Dan Clemente @DaniloNC
476 Followers 731 Following Infosec Eng, CTF with TheGoonies. Tweets are my own and should never be taken seriously.
WilltheLaw@hachyderm... @willthelaw
339 Followers 2K Following
Felipe Contreras @felipec
656 Followers 753 Following Freedom of speech maximalist, anti-censorship, anti-woke, anti-globalism, anti-centralization, anti-orthodoxy.
Marcos Irisarri @marcos_irisarri
16 Followers 34 Following
Matías E. Kühn @matias_kuhn23
278 Followers 2K Following Cs. de la Computación FAMAFyC/UNC || Landeta, Santa Fe ~ Córdoba. || 21 años || Radical, Reformista y Socialdemócrata. || Hincha de Boca.
thomas @LimThomas168
4K Followers 345 Following
vtyagli24 @vtyagli24
33 Followers 844 Following
CodeAsm.. @CodeAsm_
2K Followers 5K Following HTML decoder,Software/Hardware,(-reverse)-engineer,-ⓗ𝖆𝕔🄺乇я, student,G🅐mer.opinions are my own. Autism. he/him. I'm Something of a 🐧inux user Myself
Amirodin Kamid @AmirodinK
60 Followers 254 Following
Martin Di Paola @zeratlx
5 Followers 24 Following
Matthew Green @matthew_d_green
143K Followers 1K Following I teach cryptography at Johns Hopkins. Mastodon at [email protected] and BlueSky at https://t.co/GI4QlxYTdk.
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
lcamtuf (@lcamtuf@inf.. @lcamtuf
35K Followers 494 Following Homepage: https://t.co/iFAXZxCO5H Substack: https://t.co/yFvmNisGW3
thaddeus e. grugq the.. @thegrugq
129K Followers 423 Following Hacker :: https://t.co/km8BR8E1Ga :: [email protected] :: PGP https://t.co/dYipV8y3bo :: @warstudies :: https://t.co/H3dWknFCfk :: https://t.co/Z2lWqEVVua
Halvar Flake @halvarflake
44K Followers 3K Following I do math. And was once asked by R. Morris Sr. : "For whom?" @[email protected] At the moment, for noone.
Daniel Cuthbert @dcuthbert
30K Followers 1K Following Documentary photographer, old creaky hacker. Co-author of @OWASP ASVS standard. Blackhat/Brucon Review Board & UK Government Cyber Security Advisory Board
Brendan Dolan-Gavitt @moyix
25K Followers 6K Following Associate Professor @ NYU Tandon. Security, RE, ML. PGP https://t.co/3WXr0RfRkv Founder of the MESS Lab: https://t.co/zGycrX3Gmn "an orc smiling into the camera" — CLIP
AIfredo Ortega @ortegaalfredo
8K Followers 950 Following Software Developer - Security researcher - Shape rotator - Cybergaucho - @[email protected] AI-related: https://t.co/hhQltrgzKS https://t.co/ibyCcAp6zv
Greg Linares (Laughin.. @Laughing_Mantis
29K Followers 2K Following 20+ yrs in Infosec. Cybergoth. Musician. Autistic. Art @MalwareArt. 4x Pwnie Nominee. Red Teamer. 𝕍𝕏. Chronic Illness Fighter. I love Smite, Gamedev & Synths
[email protected].. @0xdea
12K Followers 19 Following When cryptography is outlawed, bayl bhgynjf jvyy unir cevinpl.
mdowd @mdowd
32K Followers 744 Following Internet Hacker. Founder of @vigilant_labs. Previously, co-founder of Azimuth Security (now L3Harris Trenchant)
Richard Johnson @richinseattle
16K Followers 3K Following Computer Security, Reverse Engineering, and Fuzzing; Training & Publications @ https://t.co/mloVP6rPB7; hacking the planet since 1995; Undercurrents BOFH
Gareth Heyes \u2028 @garethheyes
32K Followers 1K Following JavaScript for hackers: Learn to think like a hacker. https://t.co/e0aNEbEDk5
Immunefi @immunefi
44K Followers 640 Following The leading bug bounty platform for blockchain with the world's largest bug bounties. More than $95m paid out to whitehats and $156m in rewards available.
Nicolás Wolovick ⭐.. @nwolovick
4K Followers 1K Following HPC, CSEd, RC, FM. Votar en papel para defenderse de las computadoras.
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
Deirdre Connolly¹ @durumcrustulum
6K Followers 3K Following • 🜗 🝒 🝲 crypto as in 'cryptography' 🝳 🝡 🜖 • ¹ isogenist, co-host @SCWpod, @durumcrustulum.bsky.social
toly 🇺🇸| bip-42.. @aeyakovenko
372K Followers 5K Following Co-Founder of Solana Labs. Award winning phone creator. NFA, don’t trust me, mostly technical gibberish. https://t.co/zyJoDMQdyO
LightLink ⛓️ @LightLinkChain
138K Followers 1K Following LightLink is an Ethereum L2 blockchain that lets dApps and enterprises offer users instant, gasless transactions. Top 10 in transaction volume among rollups.
Felipe Contreras @felipec
656 Followers 753 Following Freedom of speech maximalist, anti-censorship, anti-woke, anti-globalism, anti-centralization, anti-orthodoxy.
Gadi Evron @gadievron
6K Followers 2K Following CEO & Founder, Knostic. Frmr. CISO-in-Residence, Team8. Founder @Cymmetria (acquired). Threat hunter, scifi geek, dance teacher. Opinions my own.
Matías E. Kühn @matias_kuhn23
278 Followers 2K Following Cs. de la Computación FAMAFyC/UNC || Landeta, Santa Fe ~ Córdoba. || 21 años || Radical, Reformista y Socialdemócrata. || Hincha de Boca.
Andrej Karpathy @karpathy
981K Followers 905 Following 🧑🍳. Previously Director of AI @ Tesla, founding team @ OpenAI, CS231n/PhD @ Stanford. I like to train large deep neural nets 🧠🤖💥
Tobias Lins @linstobias
5K Followers 633 Following Product Engineer · Building @Vercel Analytics · Splitbee Founder (acquired by Vercel) · Built https://t.co/ntvIQbfUkG (acquired) · Co-Creator of https://t.co/jzbfV4f1EY
Anthony Weems @amlweems
3K Followers 244 Following Cloud Vulnerability Research • The opinions stated here are my own, not those of my company.
GordonGekko_$CVP (Pow.. @GordonGekko_CVP
1K Followers 4K Following #PowerPool #PowerAgent #CVP #LSTETH
duckie @vx__notduck1e
254 Followers 1K Following likes malware | does blue+red team things | OSCP check out my rarely updated blog 👇🏻👇🏻👇🏻
mak @maciekkotowicz
3K Followers 99 Following
h4x @c0ner0ne
167 Followers 303 Following Guy from the late 70’s - former software cracker at CORE - nowadays fighting malware and still interested in breaking things
minhoryang.{eth,bsky... @__minhoryang__
146 Followers 800 Following your metaverse plumber and firefighter | DISCLAIMER - 소속한 집단의 의견을 대표하지 않고, 생각은 언제나 바뀔 수 있음
stelthintitan @jacintawothaya
103 Followers 363 Following It is with passion, courage of conviction, and a strong sense of self that we take our next steps into the world.
Fubuki Hoshino @bukiMXGA
2K Followers 3K Following Do you want to allow meoware.exe from an unknown publisher to make changes to this computer? @[email protected]
Prince Samuel @prince7007
100 Followers 683 Following 💙 Blue Teamer | Threat Researcher | Cyber Defense
Bruno Jiménez @Noxbru
738 Followers 661 Following I'm a cripplingly depressed (astro)physicist (PhD), teacher, a little geek/freak, a heisenbug hunter, Chaotic Good, me. Neurodivergent (ASD) warning.
Andres Freund (Tech) @AndresFreundTec
9K Followers 105 Following FWD: @[email protected] Postgres developer, working at Microsoft. For politics: @AndresFreundPol
Christopher Stanley @cstanley
74K Followers 598 Following {title: "Security Engineering", company: "@SpaceX,@X", education: "M.S Computer Science // Cyber Security", opinions: "my own"}
CryptoQuant 🌱 @CryptoQuant
5K Followers 5K Following 🐧 1998 Linux hacker ⛏️ 2011 #Bitcoin miner 🤖 2016 @numerai modeller 👨🌾 2020 @chia_project farmer
Gynvael Coldwind @gynvael
38K Followers 1K Following security researcher/programmer/director @ HexArcana Cybersecurity GmbH ⁂ @pagedout_zine ⁂ @DragonSectorCTF ⁂ https://t.co/ShG2c5As1K ⁂ ex-Google ⁂ he/him
Adhityaa @adtac_
167 Followers 187 Following building https://t.co/e7qzViUh8w to make tracing and monitoring easy; prev: google
👁️👃👁️ @caylesharrock
654 Followers 93 Following tippity tap all day. sometimes something good comes out the other end.
Tanya Janca @shehackspurple
51K Followers 3K Following Best-selling author of Alice and Bob Learn Application Security. Education and community at @Semgrep #AppSec #devsecops she/her Secure Code Training
Marek Benny Strihavka @StrihavkaMarek
903 Followers 104 Following Cyber-security & low-level programming
Laura Catena @LauraCatena
19K Followers 681 Following 4th generation Argentine vintner. Doctor & Biologist. Author of Malbec mon amour, Vino Argentino & Gold in the Vineyards @CatenaMalbec & Luca Wines
Supernetworks.org @spr_networks
126 Followers 30 Following 📡 Open Source, secure, user friendly and fast wifi routers @ home - One wifi password per device - Easy policy based network access - DNS Blocking & Rules
Viet Sang Nguyen @nvietsang
71 Followers 269 Following PhD Candidate in Cryptography @UniversiteLyon
🐝 Bryan James @WengersToyBus
8K Followers 639 Following Interactive creative director, designer and animator. 🎥 https://t.co/prIxXcVjxI | 👀 https://t.co/gvZGDY4uIa. Creator of https://t.co/DQljxzMdBT 🐬
Aman Dhesi @amansplaining
1K Followers 641 Following Building https://t.co/n88d4Lz40N past: co-founder @stelolabs backed by @a16z ML @square @doordash @facebook research @princetoncs
Ben Scharfstein @benscharfstein
2K Followers 2K Following Building https://t.co/vPm9TF804A @villagecompute. (Past) co-founder of @stelolabs, @rumevideo (YC S20). built recommendations @google, applied math @harvard
Michael Gogel @mgogel
9K Followers 1K Following dark patterns. generative art stuff. NLP Hacker. early adopter. crypto
Raoul @RaoulSaffron
662 Followers 895 Following Formal Verification @rv_inc Building Simbolik: The Solidity Debugger with built-in Symbolic Execution. EVM | Solidity | Debugging | Formal Methods
jfrankfurt.eth @jordanfrankfurt
2K Followers 660 Following long time @uniswap pr fabricator https://t.co/8GZBS1NCM9
Chaofan Shou @shoucccc
8K Followers 2K Following phd student @ucberkeley working on security (#fuzzing #plse #llm) / intern @hackthedefi
ebrandwine @ebrandwine
2K Followers 117 Following Amateur father and husband. Breaker of end mills. Securifier of clouds @AWS. I’m full of opinions, but they’re just mine. BLM
ljmanini @ljmanini
790 Followers 315 Following wearer of a white hat book an audit ➡️ https://t.co/199gwmgOcu
Ed @edwardmulraney
728 Followers 3K Following Software engineer | Previously @LiquityProtocol @NatwestGroup
Zac Williamson @Zac_Aztec
10K Followers 576 Following CEO @aztecnetwork. Building a privacy-first L2 on Ethereum. Cryptographer, software engineer, ex-particle physicist. Plonk co-author. Huff inventor.
Gravita Protocol @gravitaprotocol
33K Followers 175 Following An $ETH-centric Borrowing Protocol for LSTs. Fueling decentralization. https://t.co/nKynbBL93kF'n gnarly!
This is huge news, GitHub Actions is providing build provenance for artifacts! 🤩 github.blog/changelog/2024…
This is huge news, GitHub Actions is providing build provenance for artifacts! 🤩 github.blog/changelog/2024…
This software supply chain attack vector is worth knowing about:
"how I hacked Google": dependency confusion observationsinsecurity.com/2024/04/25/how…
In 1984, Ken Thompson had the best take on software supply chain security: "The moral is obvious. You can't trust code that you did not totally create yourself. No amount of source-level verification or scrutiny will protect you from using untrusted code." dl.acm.org/doi/10.1145/35…
Just to spice things up a bit, I'm pretty sure the amazing feat below would not have been possible without memory *unsafety* :)
Amazing that a chip bricked in 46-yr-old Voyager I, preventing it from sending data, and NASA figured out how to split up and reallocate its functions to other hardware, sending code 15 billion miles away (45 hours round trip!)--and Voyager's back online. blogs.nasa.gov/voyager/2024/0…
Voyager 1 transmitting data again after Nasa remotely fixes 46-year-old probe theguardian.com/science/2024/a…
Huge news for anyone working in tech in the US. Noncompetes are now banned: not just in California (like before), but nationwide. Very, very relevant for anyone at Amazon (which is the Big Tech that has enforced noncompetes even for low-level engineering positions).
The opposite of a wall of text (or worse, a wall of math or wall of code) is what I call “visual structure.” If people can tell how your thoughts are organized by zooming out and squinting a bit… …then they will have a much easier time following your thoughts. Visual…
So with all the negative talk about Microsoft security recently it occurred to me it's interesting to remember that MS also achieved one of the most consequential security successes of the last decade. A success that no one--including MS--ever talks about. Hardening Office.
There are too many separate developments to quickly mention, but overall MS began better defending abused code execution vectors. It generally did this by turning on defenses + turning off features by default, while leaving non-default options for orgs who absolutely needed them.
1/2: ⚠️ Alert for iOS users: We have credible intel regarding a high-risk zero-day exploit targeting iMessage on the Dark Web. This can infiltrate your iPhone without clicking any link. High-value targets are likely. Each use raises detection risk. #CyberSecurity
Want to do cross-language profiling? The profiler that our team at optimyze and later Elastic has worked on for the past few years has been open-sourced today! We also released a first preview of the local dev UI for it along with that (it's free)! elastic.co/blog/elastic-u…
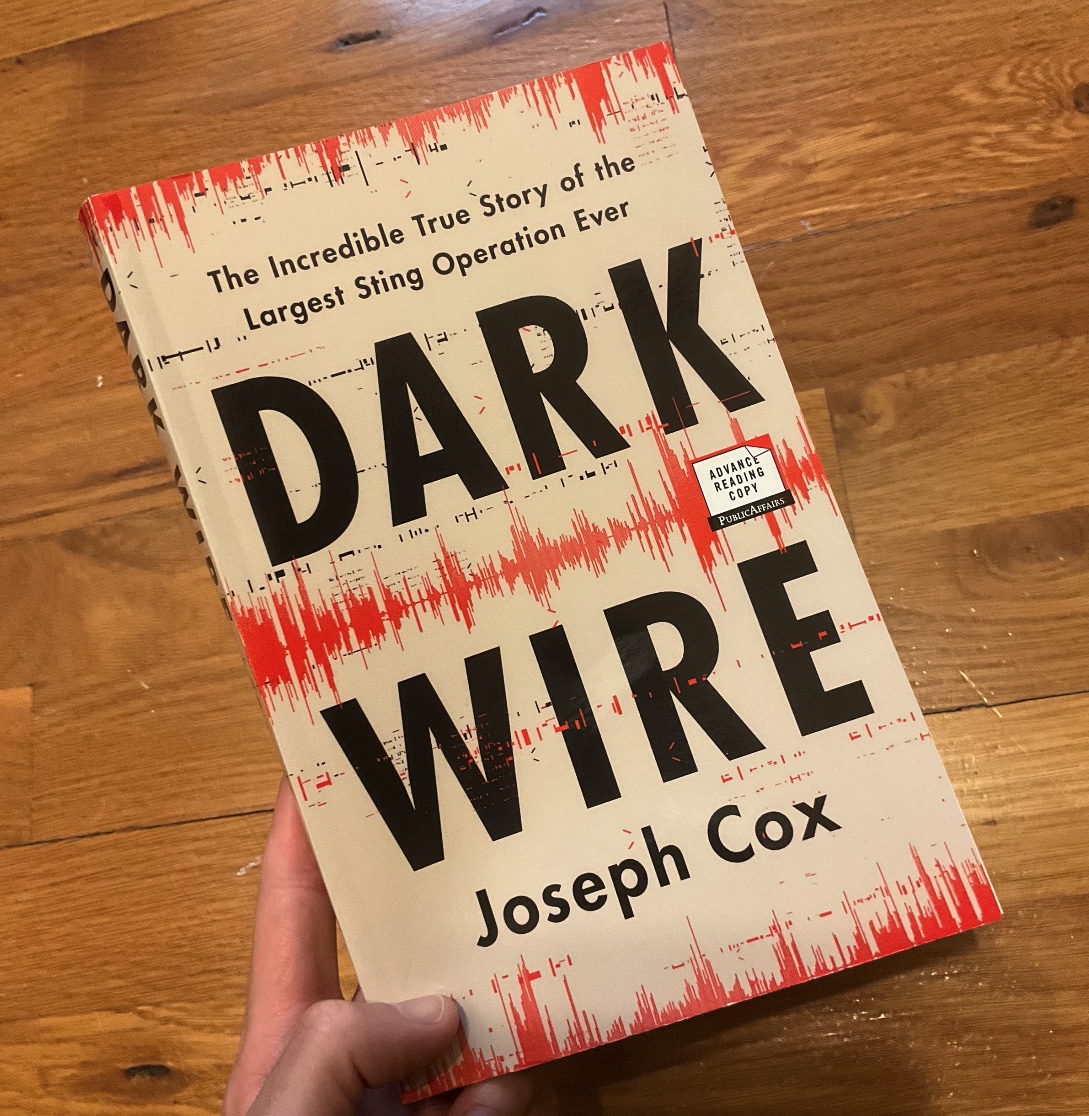
It's finally here—my book on how the FBI secretly ran its own tech startup to wiretap the world. DARK WIRE reveals its true scale & stakes for the first time Preorder now for bonus content on how I pulled back the curtain on this insane story. More below hachettebookgroup.com/titles/joseph-…
We need to STOP running DOOM on new things and START putting new things into DOOM. For example, today I added micro-transactions to the original game. Any time you pick up an item, the game freezes until you make a payment.
@julianor I think only winning strategy could be by reducing the human factor involvement and developing more robust automation for unbiased review process for both code and binary levels.