Virus Bulletin @virusbtn
Security information portal, testing and certification body. Organisers of the annual Virus Bulletin conference. @[email protected] virusbulletin.com Oxfordshire, UK Joined February 2010-
Tweets25K
-
Followers59K
-
Following1K
-
Likes1K
Infoblox researchers look into Muddling Meerkat’s operations. The actor conducts active operations through DNS by creating large volumes of widely distributed queries that are subsequently propagated through the internet using open DNS resolvers. blogs.infoblox.com/threat-intelli…
Zscaler's Santiago Vicente (@smvicente) explores the technical intricacies of Zloader's latest anti-analysis feature, introduced in recent versions. zscaler.com/blogs/security…
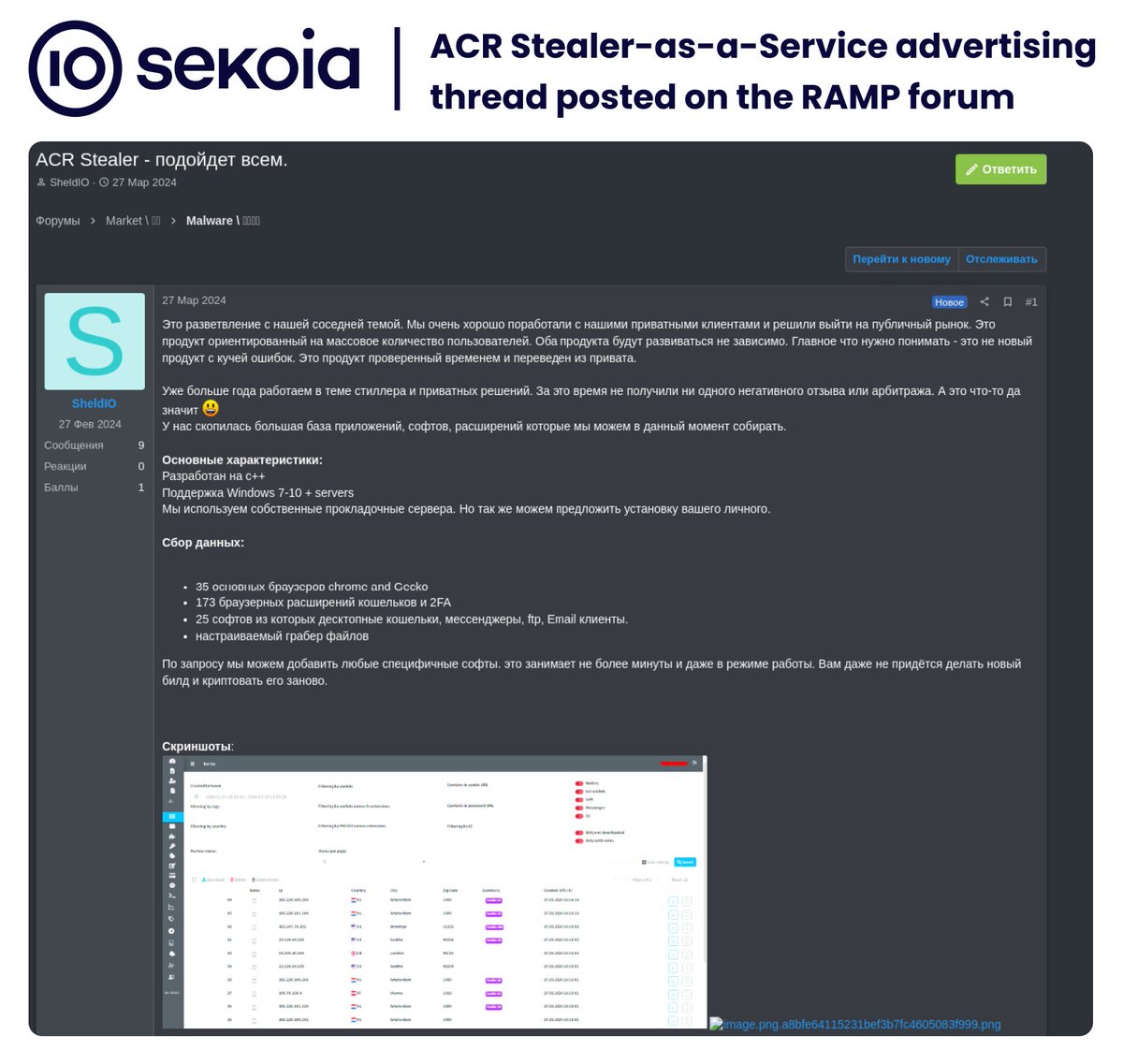
🚨 @sekoia_io analysts investigated the (not so) new infostealer, named #ACR Stealer, advertised on Russian-speaking underground forums by SheldIO. Our technical analysis revealed that ACR Stealer is a new, updated variant of the older #GrMsk Stealer. ⬇️
We had a blast at #botconf last week! During the lightning talks session we gave a brief presentation about malware config extraction using malduck🦆. As an additional treat, we've also open-sourced a few of our internal modules: github.com/CERT-Polska/ma….
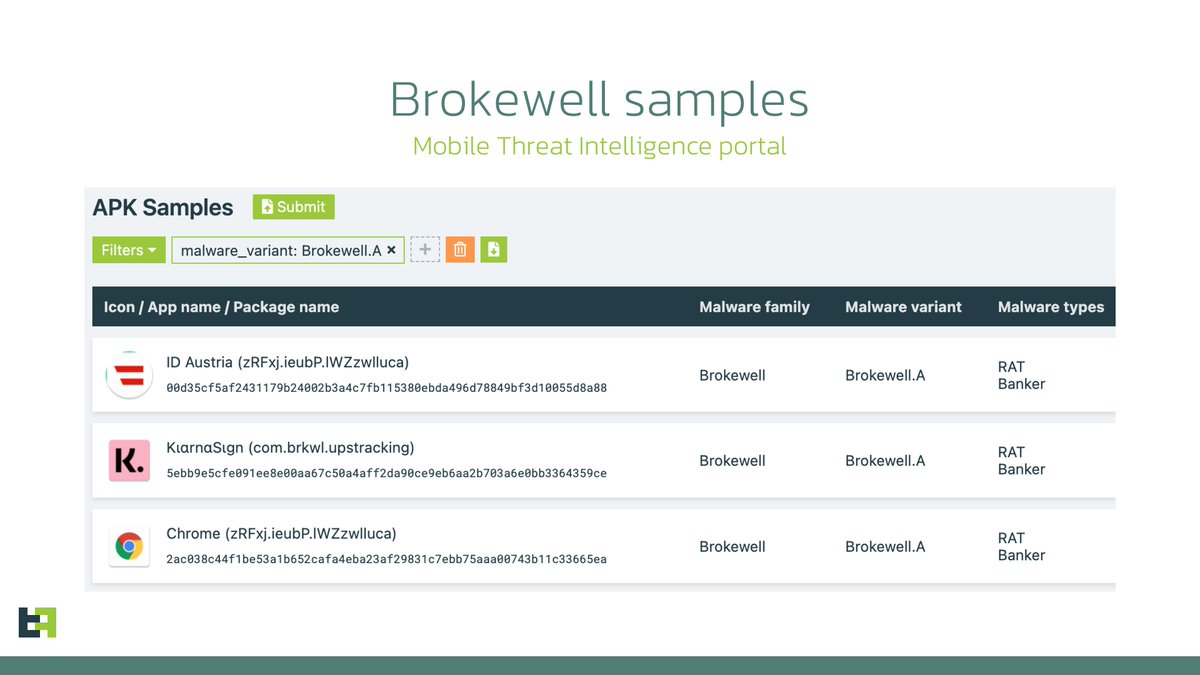
ThreatFabric analysts recently discovered a new mobile malware family in active development. Brokewell poses a significant threat to the banking industry, providing attackers with an extensive set of device takeover capabilities. threatfabric.com/blogs/brokewel…
Cisco Talos researchers analyse ArcaneDoor, an espionage-focused campaign targeting perimeter network devices. Threat actor UAT4356/STORM-1849 deployed the “Line Runner” and “Line Dancer” backdoors as components of this campaign. blog.talosintelligence.com/arcanedoor-new…
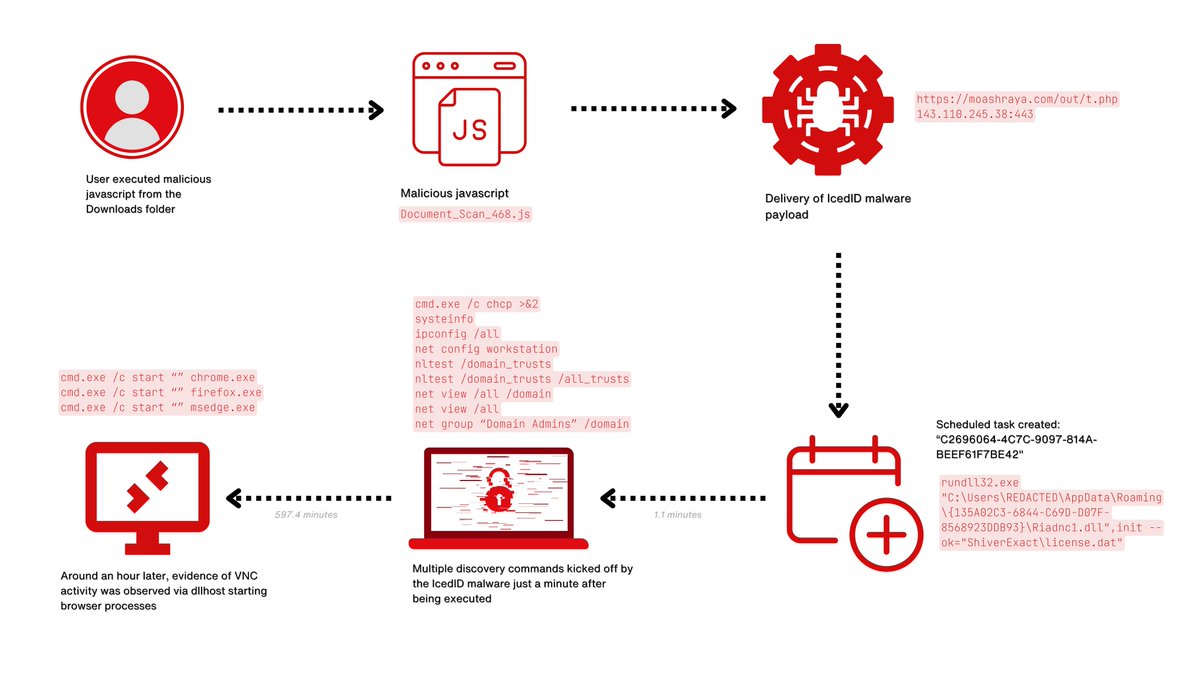
Researchers from The DFIR Report look into an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID, which dropped and executed a Cobalt Strike beacon, leading to the Dagon Locker ransomware. thedfirreport.com/2024/04/29/fro…
Version 10 of CyberChef is cooking with gas! Developed by GCHQ's very own software engineers, explore the latest features of the cyber Swiss Army knife ⬇️ github.com/gchq
Learn more about Coderex at: github.com/intel471/coder…
We are pleased to announce and welcome onboard the first five partners of #VB2024: @malwation, @TalosSecurity, @Fortinet, @CyberAlliance & @QI_ANXIN. Find out how to join them and make your company visible among security peers: virusbulletin.com/conference/vb2…
New #StopRansomware advisory provides recently observed #IOCs and #TTPs on Akira ransomware. With @FBI and international partners, we published actionable information to help all orgs identify and protect against this ransomware activity. go.dhs.gov/J9n
Microsoft has tracked at least 70 Russian actors engaged in Ukraine-focused disinformation campaigns concentrated on undermining support for Ukraine. Meanwhile, China seeks to exploit societal polarization and diminish faith in US democratic systems: msft.it/6013Y8noc
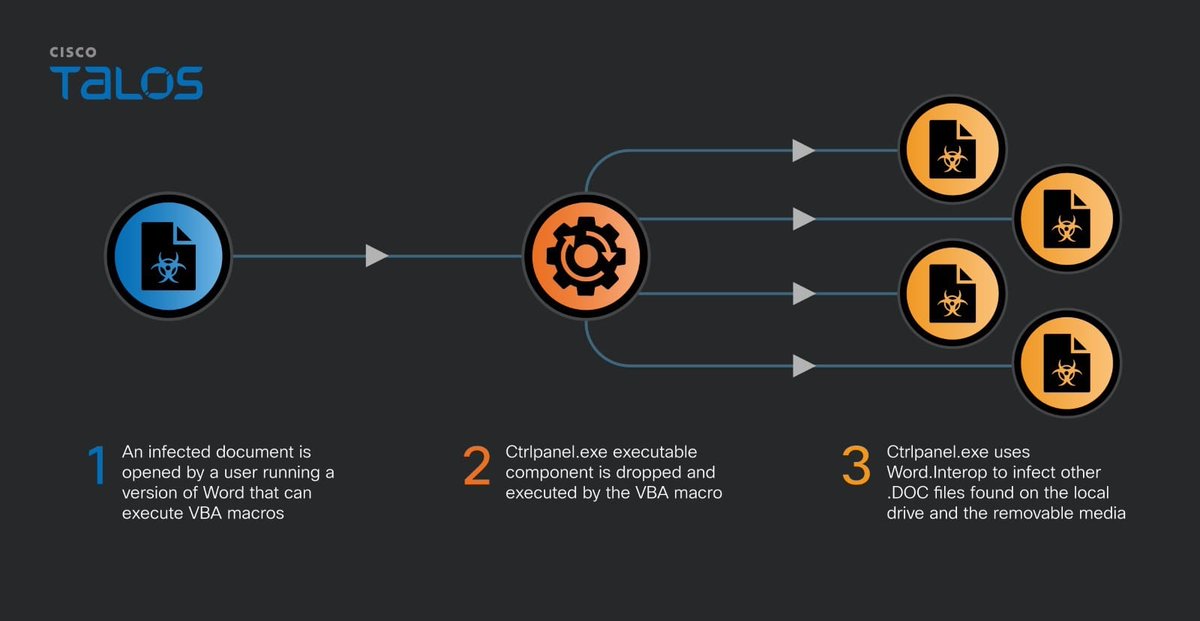
Cisco Talos researcher Vanja Svajcer writes about the OfflRouter VBA macro virus afecting users in Ukraine. blog.talosintelligence.com/offlrouter-vir…
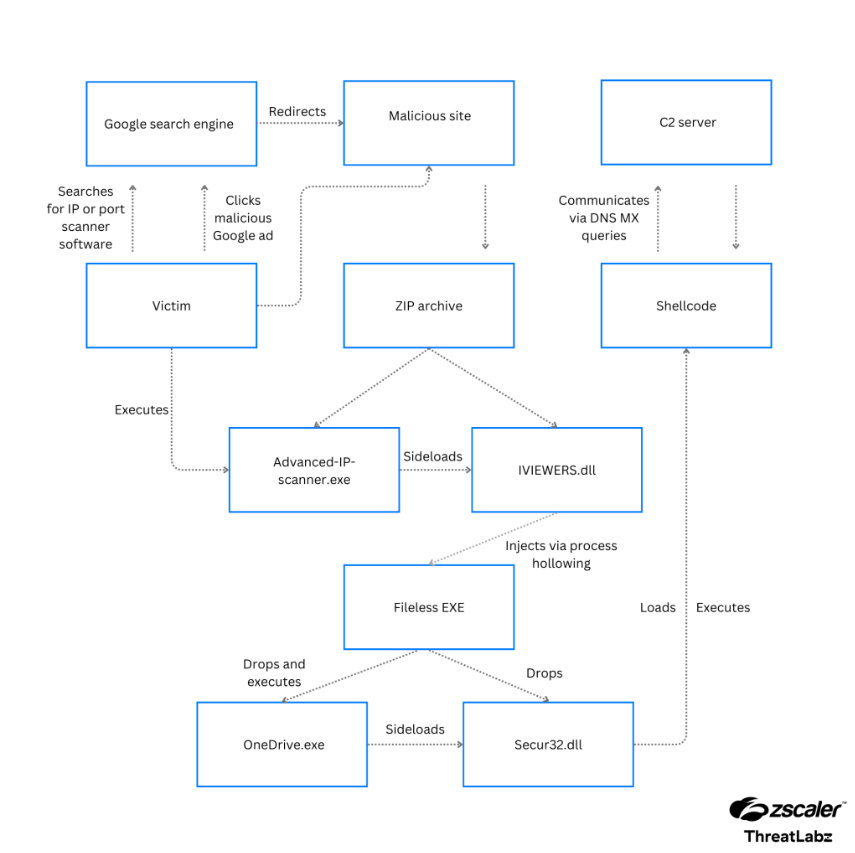
Zscaler's Roy Tay & Sudeep Singh observed a malvertising campaign pushing the MadMxShell backdoor. The threat actor registered multiple domains spoofing legitimate IP scanners and other software typically used by IT security & network administration teams. zscaler.com/blogs/security…
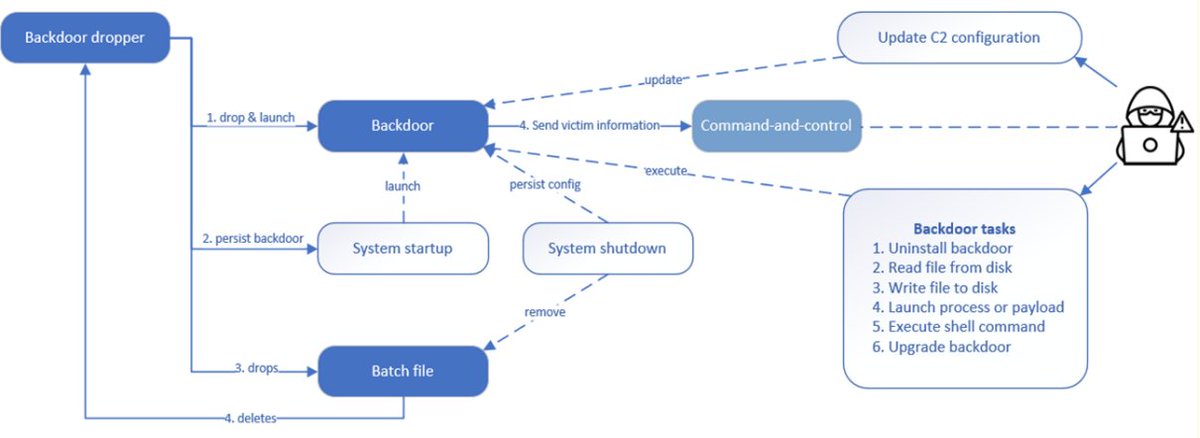
WithSecure researchers look into Kapeka, likely a new addition to Sandworm’s arsenal, used in attacks against victims in Eastern Europe. Kapeka is a flexible backdoor with all the necessary functionalities to serve as an early-stage toolkit. withsecure.com/en/whats-new/p…
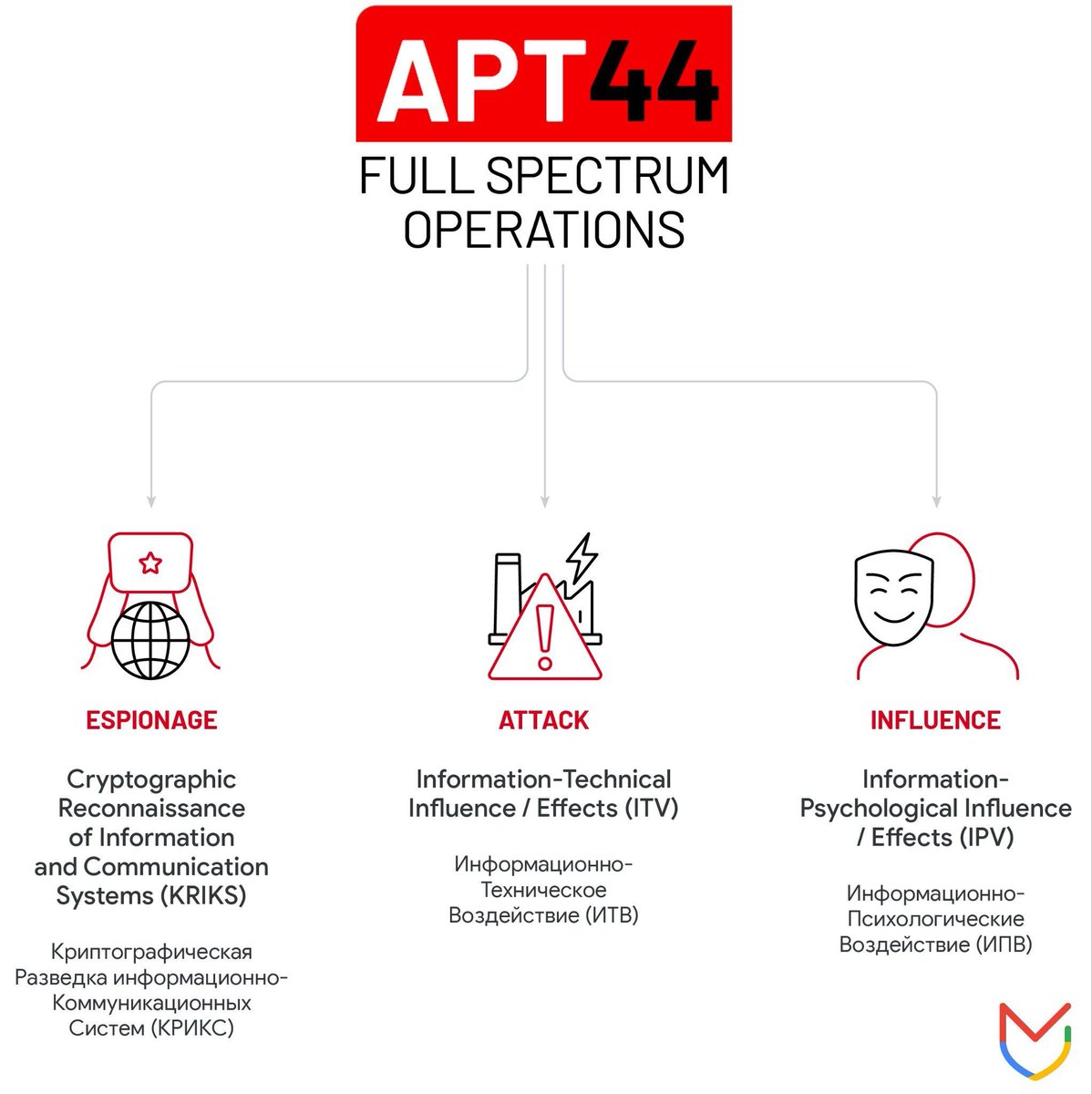
Google Mandiant researchers decided to graduate the Sandworm group into APT44 & release a report that provides additional insights into the group’s new operations, retrospective insights, & context on how the group is adjusting to support Moscow’s war aims cloud.google.com/blog/topics/th…
During a recent investigation into several criminal forums, Sophos X-Ops discovered something interesting: an influx of crude, cheap ransomware, mostly sold as a one-time purchase rather than typical RaaS models. 1/16
Thoughts on how #infosec should view #CTI as more a mindset or practice and less as a specific person or role, and how this can extend the benefits of threat-driven understanding in security: pylos.co/2024/04/17/the…
Proofpoint's Greg Lesnewich & Crista Giering describe the tactics successfully used by TA427 to gather information on topics of strategic importance to the North Korean regime. proofpoint.com/us/blog/threat…

Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
blackorbird @blackorbird
28K Followers 600 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
SentinelOne @SentinelOne
52K Followers 1K Following ONE autonomous platform to prevent, detect, respond, and hunt. Do more, save time, secure your enterprise: https://t.co/N75g1HAnCs 🐱💻
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 568 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger | Stronger Together |
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Karsten Hahn @struppigel
22K Followers 702 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
21K Followers 235 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
Grzegorz Tworek @0gtweet
30K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
Kostas @Kostastsale
16K Followers 364 Following @TheDFIRReport member | Tweeting and following mostly #ThreatIntel,#malware,#IR & #Threat_Hunting. Opinions are mine only! 🇬🇷🇨🇦
Katie Nickels @likethecoins
54K Followers 3K Following Director of Intel at @redcanary. SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft. She/her. Mastodon: @[email protected]
Jiří Vinopal @vinopaljiri
8K Followers 429 Following Threat Researcher at Check Point @_CPResearch_ #DFIR #Reversing - All opinions expressed here are mine only. https://t.co/iWvwWF1AnN
Max_Malyutin @Max_Mal_
11K Followers 302 Following Threat Researcher, Blue Team, DFIR, Malware Analysis, and Reverse Engineering. “⚔️What do we say to God of malware, Not today⚔️”
Clandestine @akaclandestine
36K Followers 5K Following | Security | Osint | Threat Research | Opsec | Threat Intelligence | Infosec | Threat Hunting |
x0rz @x0rz
98K Followers 422 Following Cybersecurity & Threat Intelligence. Knowledge is power, France is bacon 🥓
Łukasz @maldr0id
13K Followers 999 Following Military-grade @Android malware reverse engineer @Google || "Tom Brady of malware strings analysis" - @MalwareTech || Tweets are my own opinions || he/him ✨🌈🦄
krishah @GregdatKrishah
21 Followers 315 Following
VirarK @THKRmusic
67 Followers 150 Following
Rashid Noor @rnbhatti
199 Followers 295 Following پہلے بھٹو ذوالفقار تھا.. نشان ہمارا تلوار تھا🗡️ اب پسر بینظیر ہے... نشان ہمارا تیر ہے🏹
NeutronConsole @NeutronConsole
118 Followers 2K Following
IGXSAM @igxsam2493
3 Followers 57 Following
Valerie Smith @Valerie03217854
215 Followers 4K Following
Lord_Tuga ⚛️♑�.. @Lord_Tuga
57 Followers 1K Following
RAMBO’S little brot.. @23Nosrednac
382 Followers 5K Following I'm not a computer scientist or The Company, I am the RESISTANCE.
Necr0Byte @necr0byt3
4 Followers 69 Following
0x59901R @0x59901R
38 Followers 499 Following
Emma jack @emmajack005
205 Followers 3 Following
Rabbit @Red_Rabbit4440
21 Followers 820 Following
r1n9w0rm @r1n9w0rm
84 Followers 76 Following
𝗠𝗶𝗰𝗵𝗶�.. @rowaido
3K Followers 2K Following Kotlin | Linux | Ktor | Compose (for Android) | 🇯🇵基本情報技術者 | ⚠️ Sometimes, I may share information that isn’t entirely accurate, as I’m not perfect.
Alex M @alexmade86
6 Followers 70 Following
researcher Gpt LLM @researchGptllm
230 Followers 4K Following
Larry P @LarryP449220
7 Followers 58 Following
Jordi Lengua @jordilengua
207 Followers 899 Following Programador #swift 👨🏽💻 seguridad informática #hacking polifacético 👷🏽♂️🧑🏽🚀🦸🏽♂️
filipe Rally @Live122118
3 Followers 48 Following
cmurphyg @cmurfyg
1 Followers 37 Following
ししゃも @moplp9rj
218 Followers 1K Following 🇮🇳🇪🇸🇺🇸🇬🇧 Enterprise Senior Architect / Azure、AWS、AI、Security関連 ジュガードマスター 投資、クレカ、コンサル界隈をよく眺めています
Java @JavaGenbu_
605 Followers 64 Following
Rodrigo Rios 🇧🇷 @Rodrigofrj
32 Followers 621 Following O sábio nunca diz tudo o que pensa, mas pensa sempre tudo o que diz. Aristóteles.
Mohammad Shakir @Moshakir5858
3 Followers 39 Following LMNO Partnered with CrowdStrike Falcon to deliver cutting-edge solutions. Passionate about protecting digital landscapes and empowering organizations.
Etc @Etseterra
2 Followers 517 Following
Batuhan Işıldak @batuhan_isildak
466 Followers 862 Following Development Team Lead @malwation Part Time Undergrad @sabanciu Building @threat_zone
maison millemont @maison1000mont
138 Followers 2K Following
Robert Betaica C @RobertBetaicaC
19 Followers 333 Following hidup saya yang tersesat atau hidup anda yang hanya cari aman?
りん @sakaii0529
1 Followers 59 Following
Dana Mahmood @deordered
22 Followers 731 Following Fine-tuning AI models oftentimes & practicing philosopher at other times.
diarrhea_goat @diarrhea_goat
2 Followers 272 Following Systems eng by day, pentester by night. Sharing what I learn along the way and randomly bitching about IBD.
Cyber Sales VP @CyberSalesVP
7 Followers 91 Following Revenue acceleration for Cybersecurity companies - Fractional CRO, VP of Sales, CMO, BDR/SDR Teams, GTM Advisory
Thanks Always @iTimonPumbaa
8 Followers 368 Following
codinglightsoff @codinglightson
2 Followers 124 Following THIS IS A PERSONAL JOURNAL 📓 PENTESTING/CODING
Justin Kahler @jkahler_dev
45 Followers 132 Following
노경래 @nogyeongla65193
38 Followers 304 Following
Leon Basin @BasinLeon25499
114 Followers 745 Following Passionate about pioneering secure, user-friendly cyber solutions. Building bridges in #BusinessDevelopment for @FudoSecurity. Driven by innovation.
Darryl @darryl_ty
205 Followers 659 Following ya.. I’m a photographer XULA ‘24 | Learning about malware analysis one sample at a time
María @mariamartso
371 Followers 1K Following Docente de #tecnología #TIC #STEAM. Ing. Técnica Telecomunicaciones SI, MBA. Colaboro con @RedAnd_Robotica y @coitta_aagit @ingenierasenred
whatever douchebag @notsureigetthis
62 Followers 895 Following
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
MalwareHunterTeam @malwrhunterteam
219K Followers 36 Following Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.
BleepingComputer @BleepinComputer
212K Followers 175 Following Breaking cybersecurity and technology news, guides, and tutorials that help you get the most from your computer. DMs are open, so send us those tips!
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
ESET Research @ESETresearch
32K Followers 30 Following Security research and breaking news straight from ESET Research Labs.
Karsten Hahn @struppigel
22K Followers 702 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Kaspersky @kaspersky
321K Followers 123 Following Kaspersky is the world’s largest privately held vendor of Internet security solutions for businesses and consumers. For support, visit https://t.co/enRPRUIwcm
Katie Nickels @likethecoins
54K Followers 3K Following Director of Intel at @redcanary. SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft. She/her. Mastodon: @[email protected]
Ivan Kwiatkowski @JusticeRage
9K Followers 73 Following Lead cyber threat researcher @HarfangLab. Maintainer of Manalyze, Gepetto, and writer. Trolling on a purely personal capacity.
Catalin Cimpanu @campuscodi
112K Followers 1K Following Parked account. I don't post here anymore. Follow me on Mastodon: @[email protected]
x0rz @x0rz
98K Followers 422 Following Cybersecurity & Threat Intelligence. Knowledge is power, France is bacon 🥓
Łukasz @maldr0id
13K Followers 999 Following Military-grade @Android malware reverse engineer @Google || "Tom Brady of malware strings analysis" - @MalwareTech || Tweets are my own opinions || he/him ✨🌈🦄
Will Dormann @wdormann
26K Followers 1K Following I play with vulnerabilities and exploits. @[email protected]
SANS.edu Internet Sto.. @sans_isc
116K Followers 86 Following @[email protected] - https://t.co/8IgCGtJnZd - Global Network Security Information Sharing Community -
Dark Reading @DarkReading
326K Followers 47 Following One of the most widely read and trusted cybersecurity news sites, providing IT security professionals informed insights into the latest news and trends.
Trend Micro Research @TrendMicroRSRCH
52K Followers 385 Following Security research, news, and information direct from @TrendMicro experts.
Kimberly @StopMalvertisin
16K Followers 631 Following Security Researcher | Cyber Threat / Malware Analyst | Ex Sr. Threat Analyst @ Proofpoint | Founder of Stop Malvertising
jagchandra @jag_chandra
608 Followers 351 Following Malware Research, Mobile malware, Reverse Engineering, DM me to report malware apps/URL. (On [email protected] )
Niv @Nivy92
14 Followers 150 Following
8thGreyOwl @8th_grey_owl
604 Followers 130 Following Reverse Engineering Enthusiast, A Malware Analyst. Mainly focusing on APAC. All views my own. EN | JP
Camilo Gutiérrez A. @hcamiloga
1K Followers 260 Following currently based in BsAs • born and raised in Medellín • travelholic, scubaholic and security researcher • learning and sharing #DataScience #MalwareAnalysis
Geri Revay @geri_revay
911 Followers 414 Following Ex-ethical hacker and malware analyst, currently a principal security researcher. I spent the last 15 years learning how hackers work.
Silent Push Labs @silentpush_labs
221 Followers 38 Following The latest IOCs uncovered by @SilentPush's cyber threat intelligence research team
Silent Push @silentpush
601 Followers 347 Following Enterprise threat intelligence & threat hunting. We Know First.
Giovanni Vigna @giovanni_vigna
1K Followers 98 Following Professor at @ucsbcs, researcher at VMware, and founder of @Shellphish Mastodon: @[email protected]
Lior Rochberger @Lior_Rochberger
97 Followers 146 Following Security researcher Linkedin: https://t.co/Y1NtSEZMUo…
Daniel Plohmann @push_pnx
4K Followers 196 Following Reverse Engineering & Malware Research @Fraunhofer_FKIE. Projects: @Malpedia, DGArchive, MCRIT, SMDA, ApiScout, IDAscope.
Berk Albayrak @brkalbyrk7
987 Followers 1K Following Threat Research Team Lead @malwation | TI | OSINT | TA2AQX 📡
Daniel Stepanic @DanielStepanic
1K Followers 609 Following Malwarez at @elasticseclabs | Macrodata Refinement
Institute for Securit.. @IST_org
5K Followers 2K Following We design and advance solutions to the world’s toughest emerging security threats. #SecurityandTechnology #RansomwareTaskForce
RH-ISAC @RH_ISAC
2K Followers 1K Following As a member of the National Council of ISACs, the RH-ISAC is the information sharing and analysis center for these important sectors – retail and hospitality.
AVAR Asia @avar_asia
271 Followers 262 Following We are an industry led, not-for-profit community platform for #cybersecurity researchers and practitioners.
Andrei Ciubotaru (@ci.. @ciubotaruoa
3K Followers 179 Following Director of Endpoint Security @ ESET
Aleksandar Milenkoski @milenkowski
2K Followers 471 Following Sr. Threat Researcher @LabsSentinel | https://t.co/lNC3T5OShC | PhD | Personal profile | 🇩🇪
Nils Kuhnert @0x3c7
1K Followers 469 Following Threat Intelligence. Infrastructure Analysis. APT Tracking. Stoked to learn and grow. MMA, Grappling and Brazilian Jiu-Jitsu. I'm also @[email protected].
David Álvarez @wormable
549 Followers 573 Following Malware Analyst at Gen™ | Author of the book Ghidra Software Reverse Engineering for Beginners
Sylke Gruhnwald @SylkeGruhnwald
5K Followers 6K Following Reporter & Columnist. To reach me in confidence, write to [email protected] or Signal, other platforms available. Please get in touch!
Trellix Advanced Rese.. @TrellixARC
47K Followers 2K Following The Future of XDR. We Bring Security to Life.
hakan @hatr
17K Followers 2K Following writing about hackers and their tradecraft @paper_trail_m – @derspiegel – @zdf
Cyentia Institute @cyentiainst
1K Followers 293 Following Our data-driven #cybersecurity research inspires action, promotes industry progress & builds your brand's mindshare Your data has a story-let's tell it together
Sekoia.io @sekoia_io
3K Followers 147 Following A #SOCplatform driven by #threatintelligence and combining #SIEM, #SIRP, #TIP, #logmanagement in a single solution. Used by End-users, MSSP and APIs
Matthew Olney🌻 @kpyke
8K Followers 907 Following I'm Director of Threat Intelligence and Interdiction at Cisco. A host of the Beers With Talos podcast My opinions. He/Him #NAFO @[email protected]
Stefano Ortolani @ostefano
366 Followers 654 Following Threat Research Lead @ VMware, Views are my own.
Kathi Whitbey 🇺�.. @kjo364
257 Followers 377 Following Cybersecurity professional. EMS. Lucky wife. Runner. Traveler. Awesome Aunt. Marine Brat. Beer Girl.
Blackhoodie @Blackhoodie_RE
3K Followers 7 Following Blackhoodie is a free, women-only reverse engineering workshop. Check our website for infos! #BHRE
markus neis @markus_neis
3K Followers 1K Following Principal Threat Intelligence Researcher at Arctic Wolf Labs | Opinions are my own
Cyber Threat Alliance @CyberAlliance
6K Followers 546 Following The CTA is a group of cybersecurity practitioners who work together to improve the overall security of the global digital ecosystem. We are stronger together.
Andy Syrewicze @asyrewicze
2K Followers 2K Following #CyberSecurity Evangelist for @Hornetsecurity | Microsoft MVP | Neutral Good | #Azure #M365 #Microsoft365 #MVPBuzz - Opinions are my own
Adam @malworms
294 Followers 64 Following IDA pro enthusiast, malware reverser, addicted to Rocket League. @PwC_uk Threat Intelligence. All views my own.
The Banshee Queen👑 @cyberoverdrive
2K Followers 792 Following #threatintel @PwC_uk but views are mine only. Malware & infrastructure analysis with a side of cyberpunk. 🌃🌌 She/her, support 🏳️🌈🏳️⚧️✨
Gil Mansharov @mansgil
57 Followers 88 Following Security Researcher at @Mimecast | Former @_CPResearch_
CyberGeeksTech @GeeksCyber
1K Followers 9 Following Malware analysis, Incident Response, Penetration Testing
Qihoo 360 @QIHU_Official
802 Followers 12 Following Qihoo 360 is a leading Internet security company in China with over 600 million monthly active PC users and nearly 800 million mobile users.
S2W @S2W_Official
1K Followers 6 Following Intelligence and news from S2W | https://t.co/igZ1zrbXLx | https://t.co/hbonjVE5A3
hypen @hypen1117
265 Followers 242 Following Lead of Threat Analysis Team at S2W | Cyber Threat Intelligence, Malware Analysis, Incident Response, DDW Intelligence @S2W_Official | Formerly KISA, KrCERT/CC
RespectInSecurity @RespectinSec
2K Followers 31 Following Respect in Security is an initiative set up to take a stand against all forms of harassment and support victims of harassment both online and in the workplace.
TeamT5 @TeamT5_Official
2K Followers 18 Following Top Malware Researcher & #Cybersecurity Solution Provider in Asia & Pacific Intelligence Portal: #ThreatVision EDR Solution: #ThreatSonar_Anti_Ransomware
Wojciech Reguła @_r3ggi
5K Followers 853 Following iOS/macOS app security researcher & blogger. All opinions are my own 🤐.@CyberAlliance is sponsoring 2024 @virusbtn Threat Intelligence Practitioners' Summit (TIPS) Track again. CFP is now open. The TIPS theme is 'Resilience Through Collaboration' Submit abstract here: [email protected] virusbulletin.com/conference/vb2… #cybersecurity #VB2024
@lauriewired Google’s working on the cookie-theft problem. (Stealing 🍪 seems silly, until you realize that sites leave you logged in using session cookies. Currently, a stolen 🍪 can often be reused on any attacker’s system. I spoke about this at @virusbtn Conf 2023.) x.com/bleepincompute…
New Chrome feature aims to stop hackers from using stolen cookies - @serghei bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…
Thank you for featuring my work @virusbtn! 😊
On the ANY.RUN blog, security researcher @LambdaMamba reverse engineers the Snake keylogger. The sample has 4 stages, dynamic code execution, code reassembly, obfuscation, steganography, junk code, & various other anti-analysis techniques. any.run/cybersecurity-…
Big thanks to @virusbtn for featuring our #DCRat analysis! Delving into the capabilities of this #malware sheds light on evolving threats in cyberspace.
ANY.RUN researchers present an analysis of DCRat, an inexpensive, yet capable malware that gives threat actors complete surveillance over their victims. Its potential to access & control social network accounts adds another layer of risk. any.run/cybersecurity-…
I've some sad news to share I'm afraid. Alan Solomon passed away last night, after a brave struggle against cancer. He was, of course, one of the pioneers of the anti-virus industry - a larger-than-life character with a brilliant mind and a great sense of fun. I remember my…
Thanks to @virusbtn for featuring our company and to #ANYRUN's talented ambassador @LambdaMamba for writing the article on the #CrackedCantil malware. We're honored to have this blog post shared with your audience! Thank you for the opportunity to showcase our work. 🙏📰
Security researcher @LambdaMamba writes on the ANY.RUN blog about the CrackedCantil "malware symphony", examining how PrivateLoader, Smoke, Lumma, RedLine, RisePro, Amadey, Stealc, Socks5Systemz & STOP can work together in a coordinated way any.run/cybersecurity-…
@virusbtn @jfslowik Looks like that link is broken. You might have meant this one? virusbulletin.com/conference/vb2…
This is an awesome conference and I look forward to it coming to my island this year
The call for papers for VB2024 Dublin is now open. Submit your proposals for papers before 5 April for a chance to be part of one of the longest running security conferences in the world. virusbulletin.com/conference/vb2…
My appreciation for both the Cyber Threat Alliance and Virus Bulletin goes without saying! Join us in 2024 and become part of the solution! We’re stronger together!
.@CyberAlliance founding member @PaloAltoNtwks @Unit42_Intel @kjo364: "The CTA is an organization that really walks the walk. It is a real testament to the impact that CTA has had on the industry that @virusbtn continues to partner with them each year." cyberthreatalliance.org/cta-and-virus-…
My appreciation for both the Cyber Threat Alliance and Virus Bulletin goes without saying! Join us in 2024 and become part of the solution! We’re stronger together!
Unit 42 Business Operations Manager @kjo364 spoke not once but three times at #VB2023 in London. In this retrospective covering the event, she includes the importance of industry partnerships — such as that between @virusbtn and the @CyberAlliance. Read: bit.ly/46TMhjW
.@CyberAlliance founding member @PaloAltoNtwks @Unit42_Intel @kjo364: "The CTA is an organization that really walks the walk. It is a real testament to the impact that CTA has had on the industry that @virusbtn continues to partner with them each year." cyberthreatalliance.org/cta-and-virus-…
Unit 42 Business Operations Manager @kjo364 spoke not once but three times at #VB2023 in London. In this retrospective covering the event, she includes the importance of industry partnerships — such as that between @virusbtn and the @CyberAlliance. Read: bit.ly/46TMhjW
It was an honor to be invited to give the closing keynote at #VB2023. I tried something that felt new and very out there, tussling with some of the foundational metaphors that (mis|)shape cybersecurity as a practice. Video is finally up :) sentinelone.com/blog/the-physi…
Awesome project by malpedia creator @push_pnx presented at VB2023 Applied one-to-many code similarity analysis using MCRIT Talk: youtube.com/watch?v=CMu1r5…
Superb talks from Virus Bulletin 2023 are still being uploaded to YouTube, making it valuable content for those who couldn't attend in person like me. 📝 youtube.com/playlist?list=…
My talk at #VB2023 on the Ransomware-as-a-Service environment was uploaded to Youtube! I can't recommend enough using the @PwC ransomware protection framework to help prepare and harden your business against ransomware attacks: pwc.co.uk/cyber-security… youtube.com/watch?v=5nx60n…
One of my most favorite talks at #VB2023 🤗💙 Just by coincidence from my colleague, close friend and very often a mentor @megabeets_ 🙏 Content🔝 Speaker 🔝 Design 🔝
My Virus Bulletin presentation is live on YouTube! 😊 I spoke about the TP-Link Router Implant we found used by a Chinese state-sponsored threat actor. Enjoy!
My Virus Bulletin presentation is live on YouTube! 😊 I spoke about the TP-Link Router Implant we found used by a Chinese state-sponsored threat actor. Enjoy!
Newly released: recording of Itay Cohen's #VB2023 presentation "The Dragon who sold his Camaro reversing a custom router implant", in which he presents details of the reverse engineering process for the “Horse Shell” router implant. youtube.com/watch?v=7fzR7e…
rounding off a decade of research with my final talk for @Malwarebytes at this year's @virusbtn conference youtube.com/watch?v=rLDcKH… the full paper about visa and immigration scams can be found here: virusbulletin.com/uploads/pdf/co…