Zero Day Initiative @thezdi
Trend Micro’s Zero Day Initiative (ZDI) is a program designed to reward security researchers for responsibly disclosing vulnerabilities. zerodayinitiative.com Austin, Texas Joined November 2009-
Tweets3K
-
Followers76K
-
Following17
-
Likes121
[ZDI-24-400] Microsoft uAMQP for Python azure-iot-sdks-ci Uncontrolled Search Path Element Remote Code Execution Vulnerability (CVSS 9.8; Credit: Nitesh Surana (@_niteshsurana) of Trend Micro Research) zerodayinitiative.com/advisories/ZDI…
[ZDI-24-396] Microsoft Azure ODSP nikisos Uncontrolled Search Path Element Remote Code Execution Vulnerability (CVSS 9.8; Credit: Nitesh Surana (@_niteshsurana) of Trend Micro Research) zerodayinitiative.com/advisories/ZDI…
Congrats to Nitesh Surana (@_niteshsurana) and all the researchers on the MSRC Leaderboard!
Congrats to Nitesh Surana (@_niteshsurana) and all the researchers on the MSRC Leaderboard!
CVE-2024-20697: Windows Libarchive Remote Code Execution Vulnerability -- The Trend Micro Research Team takes a deep dive into this recently patch bug. An attacker could exploit this bug by enticing a user into extracting a crafted RAR archive. zerodayinitiative.com/blog/2024/4/17…
It seems @msftsecresponse has confirmed another CVE is under active attack. CVE-2024-26234 report by my old colleague Christopher Budd at Sophos is publicly known and under attack. I've updated my blog to reflect this information. zerodayinitiative.com/blog/2024/4/9/…
Microsoft patches actively exploited security feature bypass vulnerability (CVE-2024-29988) - helpnetsecurity.com/2024/04/09/apr… - @msftsecresponse @gothburz @thezdi @dustin_childs @TenableSecurity @satnam @SonicWall #PatchTuesday #SecurityUpdate #Windows #SecureBoot #CybersecurityNews
No time to read the patch blog? It is the biggest release in Microsoft's history, so we understand. That's why we summarize for you in the Patch Report - our video summary of this month's Patch Tuesday release. Check it out at youtu.be/kRU33jNKhB0
It's the largest #PatchTuesday in Microsoft's history, and Adobe has some patches as well. Join @dustin_childs as he tries to make sense of this historic release. zerodayinitiative.com/blog/2024/4/9/…
A year-and-a-half ago Trend Micro's @thezdi warned of an industry-wide problem with vendor patch quality. Sadly, nothing has changed, according to @dustin_childs. I spoke to him and @scarybeasts about what CISOs, and the industry at large, shd be doing: assured.co.uk/2024/patching-…
[ZDI-24-349|CVE-2024-23476] SolarWinds Access Rights Manager OpenFile Directory Traversal Remote Code Execution Vulnerability (CVSS 10.0; Credit: 07842c0e165d4d2d8733dd4eab48b3ed0f7afe38) zerodayinitiative.com/advisories/ZDI…
It might not be Scranton, but Vancouver is a fine place to ask our coworkers why they are the way they are. youtu.be/_JYgNrkHeeE
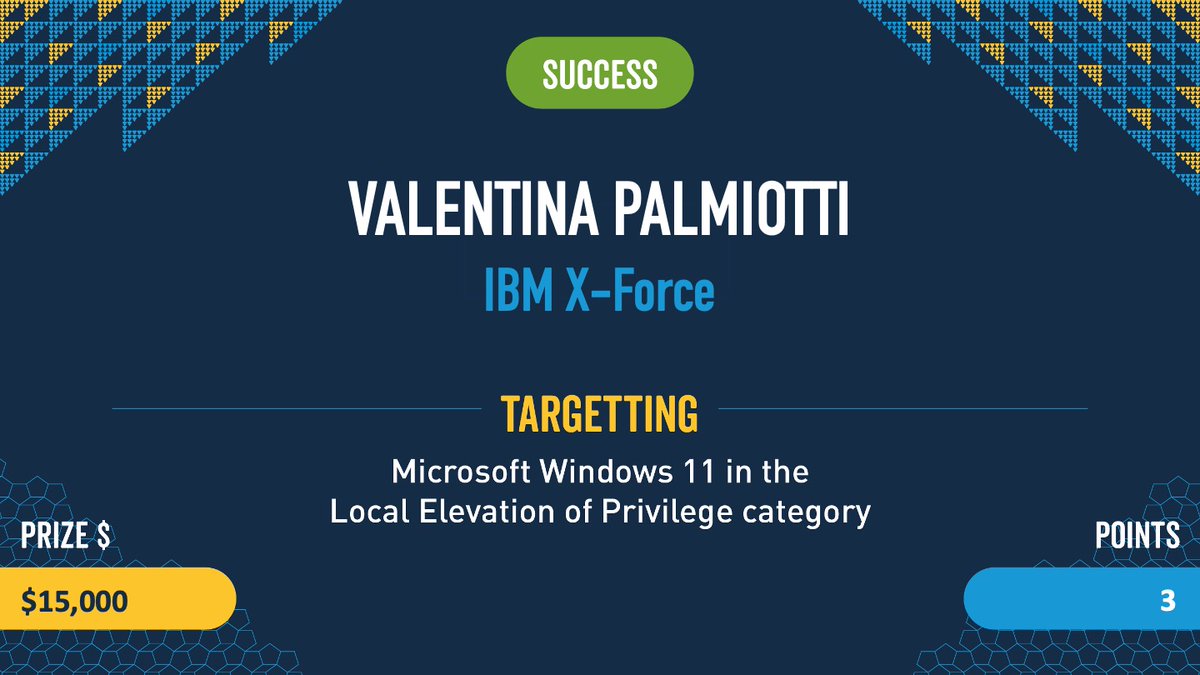
Highlights from Pwn2Own Vancouver Day 2 - Valentina Palmiotti (@chompie1337 ) vs Window... youtube.com/shorts/vN01vr1… via @YouTube
Congrats to #Mozilla for being the first vendor to provide patches for bugs disclosed during #Pwn2Own Vancouver. bleepingcomputer.com/news/security/…
Video highlights of all winning entries from #Pwn2Own Vancouver 2024 have been posted to our YouTube channel. Check out the playlist at youtube.com/playlist?list=…
Looking at the last three #Pwn2Own events (Toronto, Automotive, Vancouver), we have awarded $3,494,750 at this year's Pwn2Own events. Stay tuned for a special announcement regarding or fall event in the coming weeks.
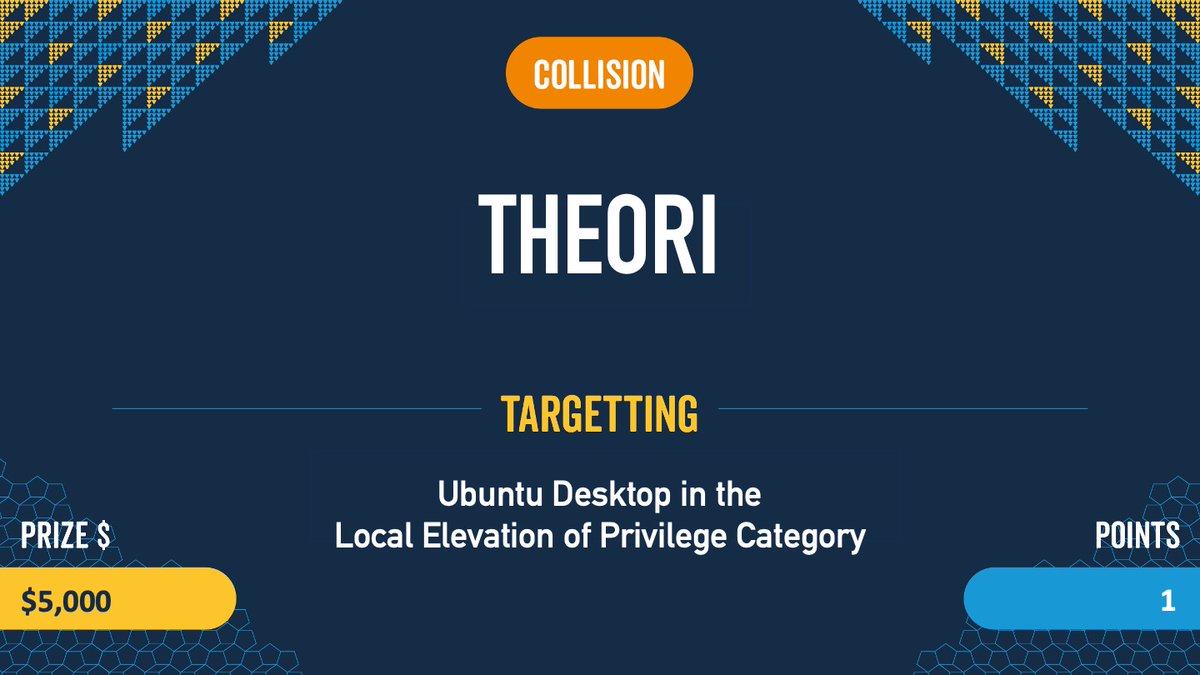
Collision: The final entry of #Pwn2Own Vancouver 2024 ends as a collision as Theori used a bug that was previously know to escalate privileges on Ubuntu desktop. He still wins $5,000 and 1 Master of Pwn point. #P20Vancouver
Confirmed! Valentina Palmiotti (@chompie1337) with IBM X-Force used an Improper Update of Reference Count bug to escalate privileges on Windows 11. She nailed her first #Pwn2Own event and walks away with $15,000 and 3 Master of Pwn points.
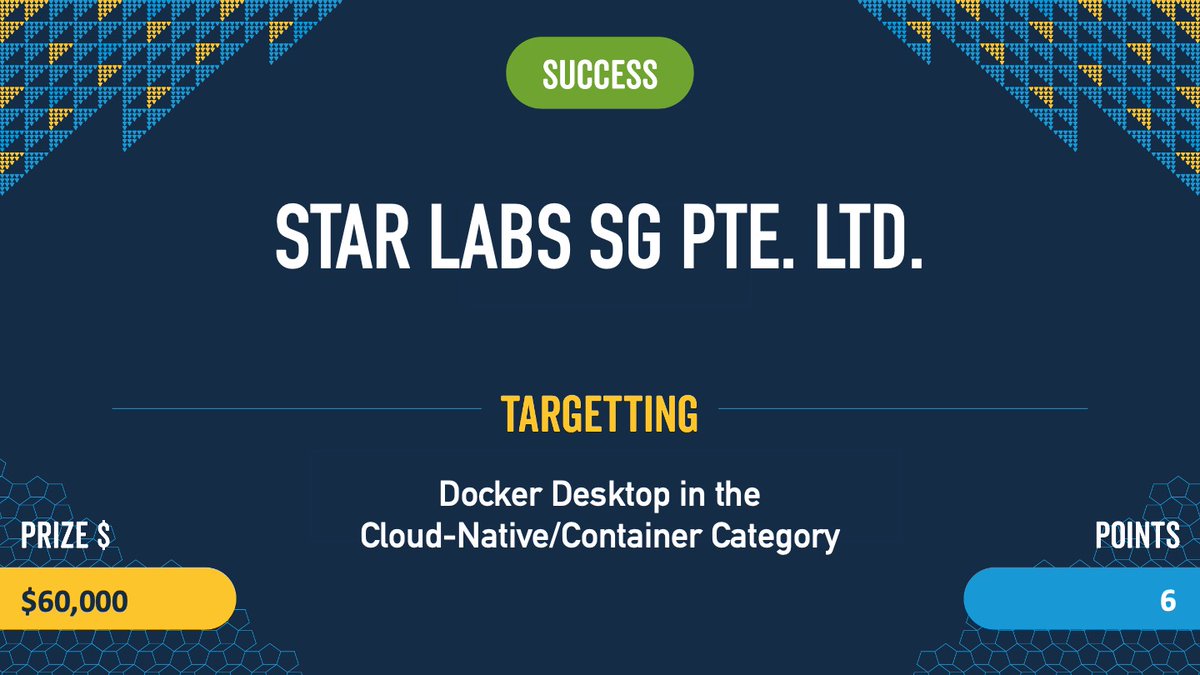
Verified! The first #Docker escape at #Pwn2Own involved two bugs, including a UAF. The team from STAR Labs SG did great work in the demonstration and earned $60,000 and 6 Master of Pwn points. #P2OVancouver

0xor0ne @0xor0ne
55K Followers 525 Following | CyberSecurity | Reverse Engineering | C and Rust | Exploit | Linux kernel | PhD | My Tweets, My Opinions :) |
Ptrace Security GmbH @ptracesecurity
53K Followers 883 Following Empowering IT Security Professionals through Hands-On Online Courses.
Julien | MrTuxracer �.. @MrTuxracer
30K Followers 417 Following Freelancer | Full-time #BugBounty | @Hacker0x01 H1-Elite & $1,500,000 Hacker | ❤️ IDA Pro
shubs @infosec_au
50K Followers 2K Following Co-founder, security researcher. Building an attack surface management platform, @assetnote
[email protected].. @0xdea
12K Followers 19 Following When cryptography is outlawed, bayl bhgynjf jvyy unir cevinpl.
Oliver Lyak @ly4k_
8K Followers 267 Following Yet another security researcher 🔦 Github: https://t.co/7WFOFz17KI
Alisa Esage Шевч�.. @alisaesage
35K Followers 142 Following Hacker & Founder @zerodaytraining • First Female Winner Pwn2Own • Solo Entrepreneur • Student of Physics
ϻг_ϻε @steventseeley
21K Followers 519 Following Hermetic Initiate. Exploring conscience and the nature of reality. I also hack things. @[email protected]
Tuan Anh Nguyen 🇻�.. @haxor31337
13K Followers 2K Following 28 y/o Bug Bounty Hunter and Red Teamer at Viettel Cyber Security. Brand Ambassador @Hacker0x01 - Researcher Spotlight @Bugcrowd
Synacktiv @Synacktiv
17K Followers 277 Following Offensive security company. Dojo of many ninjas. Red teaming, reverse engineering, vuln research, dev of security tools and incident response.
hasherezade @hasherezade
84K Followers 844 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Alex Plaskett @alexjplaskett
9K Followers 589 Following Security Researcher | Pwn2Own 2018, 2021, 2022, 2024 | Tweets about 0day, OS, mobile and embedded security.
Saar Amar @AmarSaar
18K Followers 362 Following Reversing, exploits, {Windows, Hyper-V, *OS} internals, mitigations. Apple SEAR. Opinions are my own. @[email protected]
an0n @an0n_r0
11K Followers 716 Following CRT(E|O|L) | OSCP | @RingZer0_CTF 1st (for 2yrs) | HackTheBox Top10 | RPISEC MBE | Flare-On completer | GoogleCTF writeup winner | SSD research | Math MSc |🇭🇺
Unit 42 @Unit42_Intel
51K Followers 88 Following The latest research and news from Unit 42, the Palo Alto Networks (@paloaltontwks) Threat Intelligence and Security Consulting Team covering incident response.
kmkz @kmkz_security
18K Followers 1K Following Offensive Security fanatic, Offsec Team lead... pom-pom girl? Who fuckin' cares ??
Ichigo @Ichigo4661272
11 Followers 167 Following
sskdas @ss1sadasasda
0 Followers 2 Following
shantanu sawantbhosal.. @shantan93308960
0 Followers 27 Following
Qirui @Qirui28124
14 Followers 1K Following
Rafi Rafi @rafisorker90
129 Followers 599 Following I am B2B and B2C Led Generation Expert E-mail; [email protected] What's app number: 01767536884 Work at : Fiverr / Upwork / Freelancer/Peoplehour
fd @Fareed3131
38 Followers 2K Following
Deen @itxDeeni
3K Followers 3K Following Backend/ API Engineer | Technical Writer 👨💻 ⚡️Typescript 🐍Python ☕️Java 🐙Git 🐧Linux ⚓️Scrum ☁️AWS 🐳Docker 🌟GitHub 🏆Agile 📊SEO 🤖AI
#BTC.Eth# @LionofCrypto2
156 Followers 1K Following Crypto Promoter |DM for promotions,Marketing & Business. Be Honest to everyone,everywhere & Always.Always take stand for right things.
Thanks Always @iTimonPumbaa
1 Followers 368 Following
mmeies @mries43255
0 Followers 6 Following
Anubian @0xanubian
2 Followers 57 Following
filipe Rally @Live122118
0 Followers 32 Following
javeed @javeed_8
3 Followers 28 Following
yagyuu @topyagyuu
0 Followers 21 Following
Your Therapist @YerShrink
408 Followers 3K Following
Jorge Mazzonelli aka .. @jmazzonelli
131 Followers 1K Following
daniele pesolo @DPesolo
5 Followers 273 Following
Osama Elmansori @ElmansoriOsama
3 Followers 164 Following
Book Reading @BookR97356
0 Followers 17 Following
Pablo San @PabloSa93603903
33 Followers 225 Following
Skhalla @OuzenMirai
0 Followers 39 Following
Noah @pwnProphet
23 Followers 72 Following
sibernetikawan @TelaahTerarah
227 Followers 2K Following Transhumanism, Conceptual Reverse Engineering, Metacognition & Compression. Understanding underlying mechanism how any system understanding itself. lang: id-id.
BlackPanther86 @panther86_black
35 Followers 866 Following SysAdmin|Security|i hack mostly on @Microsoft|BugBounty Hunter
나영욱(이태수/�.. @4fI2l6Kr7kOo3fQ
649 Followers 5K Following 우리 하나로 마트 점장 문공 입니다.서울중앙지법 민사합의12부 부장판사입니다.대통령 명예훈장입니다.대법관 상달 입니다.정신과 특작부대 사령관 입니다.하버드 의대 명예박사입니다.방송공사 명예회장입니다.대법원 초대 상임원장입니다.목민관 총판사입니다.세계 성결교회 상임 부목사입니다.
Benjamin @Benjamin15469
88 Followers 490 Following Cybersecurity Enthusiast | Industrial Automation Engineer | Software Developer | Lifelong Learner (Math & Physics) | Public Speaker | Gamer | Friend.
sav @savi0
170 Followers 2K Following
Aniruddha kale @kaleaniruddha
5 Followers 22 Following
sayed essam @sayedessam76860
3 Followers 289 Following
Anthony Jamous @AnthonyJamous11
15 Followers 171 Following
Juan José Torres @Juanjo_Torres11
173 Followers 592 Following Cloud Engineer: SecOps @Platzi | Ingeniero @DISCuniandes | Amante de los videojuegos, cómics, la historia y la música
Hades @Hades6366852440
17 Followers 131 Following
Vasq @Vinigan
212 Followers 1K Following Muchos nos preguntamos si somos buenos queriendo ser malos o somos malos queriendo ser buenos
crow @MrCccrow
1 Followers 30 Following
Num @ii6934
0 Followers 358 Following
jackey77 @hzjtyh
11 Followers 385 Following
Nithin S @NithinS1548654
43 Followers 412 Following
BSides Barcelona @BarcelonaBsides
848 Followers 800 Following Official Security BSides Barcelona account.
Alo @Hal90910
0 Followers 2K Following
Fighter001 @Fighter00192814
21 Followers 256 Following
Pieeck @_pieeck
0 Followers 55 Following
Chaolinbombin @Calc3t1n
7 Followers 86 Following
Carlos Zepeda @ZorD_13
198 Followers 681 Following
Phil Emery @fidodido666699
38 Followers 75 Following
Carlos A. Lozano Arro.. @clozarr
421 Followers 1K Following Software Developer 👨🏻💻 | Traveler ✈️🌴| Fútbol ⚽️
Peter Girnus @gothburz
317 Followers 108 Following Threat Hunter 🥷🏻 Securing the Web Landscape, One Byte at a Time 🛡️Learning something new 🚀👨🏼💻 Sr. Threat Researcher with @theZDI
TheZDIBugs @TheZDIBugs
3K Followers 2 Following Checks for high severity, 0day, or Pwn2Own related advisories published by @thezdi
Jimmy Calderon @vectors2final
139 Followers 957 Following
Piotr Bazydło @chudyPB
3K Followers 257 Following Vulnerability Researcher at the Zero Day Initiative | Pwn2Own Miami 2022 | Microsoft MVR
renorobert @renorobertr
2K Followers 843 Following
Hossein Lotfi @hosselot
6K Followers 56 Following Vulnerability researcher at Zero Day Initiative... check #hosselot_tips for vulnerability research tips. 'A machine never faults. It reflects human's faults.'
Michael DePlante @izobashi
3K Followers 658 Following Security Researcher at the Zero Day Initiative. DMs open.
Mat Powell @mrpowell
565 Followers 151 Following According to Wired, “a gruff-looking bald man with a goatee”
T. @trendytofu
820 Followers 596 Following something something Cyber, something something security something.
Trend Micro @TrendMicro
115K Followers 4K Following We're a global leader in cybersecurity that helps make the world safe for exchanging digital information.
Fritz Sands @FritzSands
550 Followers 945 Following Coder, biker, brewer, shooter, political animal, tango dancer.
Brian Gorenc @MaliciousInput
3K Followers 428 Following Leader of the Zero Day Initiative. Pwn2Own organizer and adjudicator. Trafficker of export-controlled intrusion software. Bug Hunter.
The Dustin Childs @dustin_childs
2K Followers 340 Following Just a simple information security gnome trying to make his way through the universe. Part-time patch wrangler. Tweets are just my opinion and such.Pwn2Own @Pwn2Own_Contest
6K Followers 1 Following All Pwn2Own tweets now go out of the @thezdi. #pwn2ownHad the best time in Vancouver for #Pwn2Own! Was great to finally participate in-person and meet other researchers, vendors and more. Thanks again @thezdi for the great event and congratulations to all other participants!
Pwn2Own Vancouver 2024 is complete! Over the 2 day event, we awarded $1,132,500 for 29 0-days. Join @dustin_childs and @MaliciousInput as they cover some of the highlights, including Master of Pwn winner @_manfp exploiting all 4 web browsers in the event. youtu.be/3sSVsCQcd9c
I did it again! It was fun to work on exploit one night before the event and one shot it at the demonstration! And thank you @thezdi and @ubuntu for making the report process painless!
Validated! Kyle Zeng from ASU SEFCOM brought a race condition to #Pwn2Own and successfully used it to escalate privileges on #Ubuntu desktop. He earns $20,000 and 2 Master of Pwn points. #P2OVancouver
My CRLF injection vulnerability in .NET FTP client has been described by our VRS team. Simple, yet fun vulnerability, which can sometimes lead to a nice impact.
In our latest guest blog, the Trend Micro Research team details CVE-2023-36049 - a .NET LPE bug originally found by ZDI's own @chudyPB. An attacker could write/delete arbitrary files in the context of the FTP server. Read all the details at zerodayinitiative.com/blog/2024/3/6/…
Thank you @thezdi @TrendMicro for supporting #OffensiveCon24 as gold sponsors! zerodayinitiative.com
I'm shocked - my research was ranked as 2nd best web research of 2023. Thanks for the votes and congratulations to the rest of researchers!
The results are in! We're proud to announce the Top 10 Web Hacking Techniques of 2023! portswigger.net/research/top-1…
The results are in! We're proud to announce the Top 10 Web Hacking Techniques of 2023! portswigger.net/research/top-1…
CVE-2024-21412 is an active zero-day vulnerability that was disclosed by Trend Micro's @thezdi to Microsoft & published today. Trend customers are protected; organizations should take immediate action. Video below & more info: bit.ly/3P5rhkb bit.ly/3HYNqfR
It's been a blast for @steffensanwald and me at #Pwn2Own Automotive. Thanks for having us @thezdi @VicOneAuto and congrats to all contestants!
It was awesome to catchup with friends, so much work went into making this competition. huge thank you to the folks at @thezdi , they put countless hours in order to make this happen, respect 🔥
Trend Micro's Peter Girnus, Aliakbar Zahravi & Simon Zuckerbraun delve into the Phemedrone Stealer campaign's exploitation of CVE-2023-36025, the Windows Defender SmartScreen Bypass vulnerability, for its defense evasion & investigate the malware's payload trendmicro.com/en_us/research…
Recording of my Hexacon talk "Exploiting Hardened .NET Deserialization: New Exploitation Ideas and Abuse of Insecure Serialization" is available! Talk: youtu.be/_CJmUh0_uOM?si… White paper: github.com/thezdi/present… I hope you will find it useful 🙂
Really proud of the @InterruptLabs team. We had some bad luck with the draw order and vendors being vendors but still an impressive result. 🥳 And thanks to @thezdi for running such an awesome event. See you next time.
I've approved a new version of YSoSerial.Net. Thanks to all contributors especially @chudyPB for so many new gadgets! 📃See @chudyPB🤯"130 page" research: github.com/thezdi/present… 📽️Video here: youtube.com/watch?v=5UyX7H… at @hexacon_fr #AppSec #DotNet #Deserialization
(0day) [ZDI-23-1044] Microsoft GitHub Dev-Containers Improper Privilege Management Privilege Escalation Vulnerability (CVSS 9.9; Credit: Nitesh Surana (@_niteshsurana) of Trend Micro Research) zerodayinitiative.com/advisories/ZDI…
💎🔨 Exploiting Hardened .NET Deserialization: New Exploitation Ideas and Abuse of Insecure Serialization, by Piotr Bazydło (@chudyPB)