Malware Patrol @MalwarePatrol
Malware | Ransomware | Phishing | Cryptomining malwarepatrol.net USA and Brazil Joined March 2009-
Tweets32K
-
Followers9K
-
Following2K
-
Likes27K
"Our analysis revealed critical #vulnerabilities in #keyboardapps from eight out of the nine vendors in which we could exploit that vulnerability to completely reveal the contents of users’ #keystrokes in transit." citizenlab.ca/2024/04/vulner…
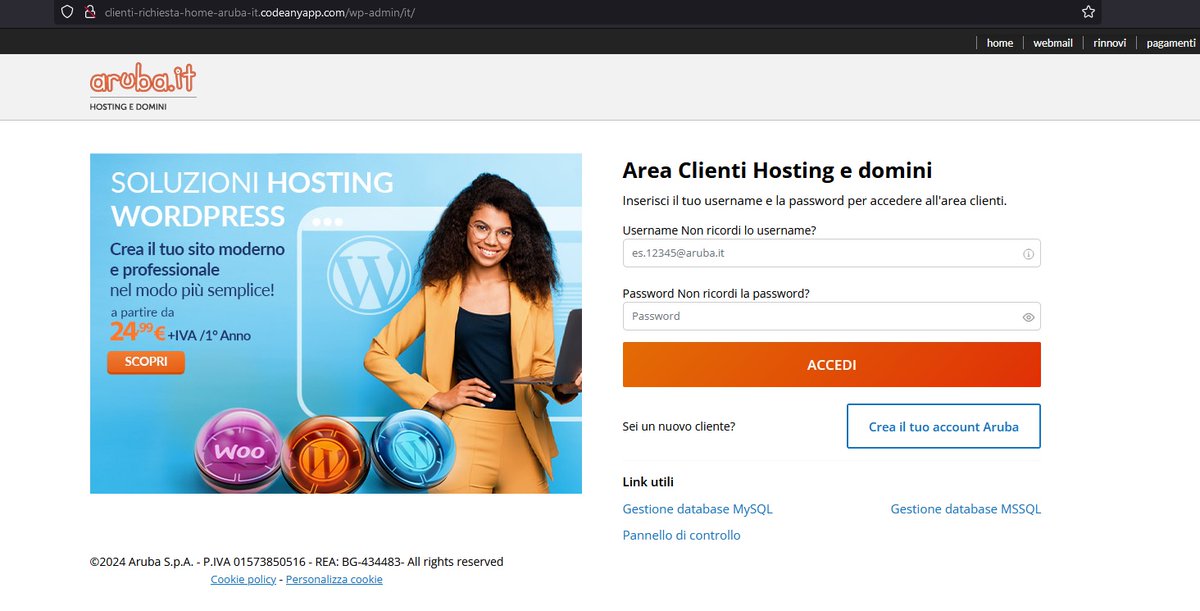
"#ThreatActors utilize fraudulent websites hosted on popular legitimate platforms to spread #malware and #stealdata. To evade detection, #attackers employ obfuscation methods and checks on referral URLs." zscaler.com/blogs/security…
"Starting with a Word document using the #TemplateInjectiontechnique, download and run RTF that uses a #vulnerability in the equation editor (EQNEDT32.EXE)." #RemcosRAT asec.ahnlab.com/ko/64421/
Request a free evaluation of our Enterprise Threat Intelligence Feeds. #malware #ransomware #threatintelligence malwarepatrol.net/enterprise-eva…
"According to a public-facing vendor advisory, the #vulnerability is ostensibly a VFS sandbox escape in #CrushFTP managed file transfer software that allows “#remoteattackers with low privileges to read files from the filesystem outside of VFS Sandbox.”" rapid7.com/blog/post/2024…
The disruption of the LabHost phishing service and the arrest of several key players puts a dent on the phishing operations of its many criminal clients. This should effectively reduce the number of phishing attacks globally for the time being. Read: ⬇️ research.trendmicro.com/LabHostTakedown
"🚨 Multi-Year Cyberattack: Chinese hackers suspected of breaching Volkswagen, unveiling espionage activities and stolen sensitive data. Implications for automotive industry and the need for robust cybersecurity measures. #Cybersecurity #Volkswagen #Chin… ift.tt/Mxo93Rm
⚠️@CISAgov issued 8 NEW public #ICS advisories. These advisories provide info about current security issues, vulnerabilities, & exploits surrounding ICS. More at cisa.gov/news-events/al…
Yesterday @TalosSecurity released a threat intelligence blog detailing the ArcaneDoor espionage-focused campaign. Microsoft Threat Intelligence collaborated with Cisco Talos to provide data and analysis on the threat actor Storm-1849 (UAT4356). msft.it/6015YJdzL
”#SSLoad is designed to stealthily infiltrate systems, gather sensitive information and transmit its findings back to its operators. Once inside the system, SSLoad deploys multiple #backdoors and #payloads to maintain persistence and avoid detection.” securonix.com/blog/securonix…
”Cyble Research & Intelligence Labs (CRIL) identified a #DragonForce #ransomware binary based on #LOCKBIT #Blackransomware, suggesting the threat actors behind DragonForce used a leaked builder of LOCKBIT Black ransomware to generate their binary.” cyble.com/blog/lockbit-b…
”Cisco Talos discovered a new ongoing campaign since at least February 2024, operated by a #threatactor distributing three famous #infostealer malware, including #Cryptbot, #LummaC2 and #Rhadamanthys.” blog.talosintelligence.com/suspected-cora…
Offering a cloak of anonymity and encrypted pathways, these services have emerged as an option that allows attackers to obfuscate their activities and bypass conventional security measures. #Tunneling #IngressAsAService #MaliciousTunneling #ThreatIntel malwarepatrol.net/tunnel-vision-…
We offer free Basic Defense blocklist accounts for EDUs. Request yours here. malwarepatrol.net/free-subscript…
”In today’s publication, they resorted to simply executing a single obfuscated JavaScript file calleddeference.js, a #trojanized version of a file from the legitimate package node-config.” blog.phylum.io/north-korean-s…
"The main objective of #GuptiMiner is to distribute #backdoors within big corporate networks. We’ve encountered two different variants of these backdoors" decoded.avast.io/janrubin/gupti…
"This campaign targets users through an #openredirect #vulnerability within a domain owned by #Nespresso, a well-known coffee manufacturer." hackread.com/nespresso-doma…
"The researcher claims that the #vulnerabilities he found in PMP components can be exploited to gain access to plaintext content keys guarded by #PlayReady. These keys may then allow a logged-in user to decrypt content from popular streaming services." securityweek.com/microsoft-drm-…

mRr3b00t @UK_Daniel_Card
92K Followers 7K Following 真理的揭露者 Quis custodiet ipsos custodes fella in cyberspace #nafo undercover #FVEY Lovely Horse #fella #meme #farm #appreciator #cyber #specialist
OccupytheWeb @three_cube
219K Followers 4K Following Pentester, Forensic investigator, and former college professor. Trained hackers at every branch of US military and intelligence. Visit me at https://t.co/G478wufszw
Karsten Hahn @struppigel
22K Followers 702 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Will @BushidoToken
29K Followers 3K Following Threat Intel & Hunting @Equinix | Co-founder @CuratedIntel | Co-author @SANSForensics FOR589 | @darknetdiaries #126: REvil
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon) https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
SentinelOne @SentinelOne
52K Followers 1K Following ONE autonomous platform to prevent, detect, respond, and hunt. Do more, save time, secure your enterprise: https://t.co/N75g1HAnCs 🐱💻
☣ KitPloit - Hacker.. @KitPloit
118K Followers 3K Following Hacking and PenTest Tools for your Security Arsenal!
Clandestine @akaclandestine
35K Followers 5K Following | Security | Osint | Threat Research | Opsec | Threat Intelligence | Infosec | Threat Hunting |
Lisa Forte @LisaForteUK
54K Followers 5K Following Cyber Security - Partner @redgoatcyber - Climber / Caver. she/her
Gi7w0rm @Gi7w0rm
14K Followers 677 Following Threat Intelligence and #URINT Analyst | See my Linktree for other socials | In case I post false intel, contact me! Support me: https://t.co/5WgDqr0K8p
James @James_inthe_box
21K Followers 438 Following
Katie Nickels @likethecoins
54K Followers 3K Following Director of Intel at @redcanary. SANS Certified Instructor for FOR578: CTI. Senior Fellow at @CyberStatecraft. She/her. Mastodon: @[email protected]
Michael Frederick Mar.. @MFMarcotte
1K Followers 2K Following Tech executive & board member | VC partner | philanthropist
Ouanilo MEDEGAN 🇧�.. @ouanilo
6K Followers 841 Following #IT, #InfoSec (https://t.co/Ytlo6lZcGW), #MMA 🥋 (https://t.co/ZYBAmtO76e), #Africa
Gus Swens @GGGGGGVIC
34 Followers 400 Following
2amtech @2amtech
314 Followers 823 Following From startups to growth bound businesses, we go beyond software to ensure that your vision becomes an innovative and practical application.
Veki @vekivac
41 Followers 261 Following
LinK @LinK22659215
2 Followers 71 Following
El-Viajero @El_Viajeo
0 Followers 33 Following
Jean-Jacques Borie @jjborie
66 Followers 367 Following Leadership in Software Engineering, Data, AI, Cybersecurity & Technology Solutions PH.D. Student in CYBERSECURITY MANAGEMENT
オスカー @oscarrage
25 Followers 52 Following
MoeSec @MoeSecCom
6 Followers 226 Following Website Hack Repair, Malware & Blacklist removal services. Website Firewall Protection Digital Forensics Vulnerability Assessment & Penetration Testing
ً @VBrfTp7LS280861
0 Followers 391 Following
xeria coli @XeriaColi
62 Followers 230 Following
Robin @Robin1954978
0 Followers 118 Following
halitay $BUBBLE 🫧�.. @halitayair13706
67 Followers 669 Following
David Krivobokov @_6461766964
12 Followers 30 Following
sobot @sobot
65 Followers 446 Following
jtc1sc7 @jtc1sc7
62 Followers 38 Following ISO/IEC JTC 1/SC 7 Software and systems engineering is a standardization subcommittee of the Joint Technical Committee ISO/IEC JTC 1 of ISO & IEC
ShadowFalcon @ShadowFalc2734
31 Followers 129 Following
Cyber Security Topics @Mawg0ud
4K Followers 4K Following Daily posts for cybersecurity analysts about: ➟ RedTeam ➟ Incident Response ➟ Digital Forensics ➟ Threat Intelligence .
𝓙𝓪𝓬𝓴2 @2RunJack2
1K Followers 2K Following #ThreatIntel Researcher @S2W_Official @TALON_INTEL Main Author of Threat Intel Report 'Campaign DOKKAEBI : Documents of Korean and Evil Binary' / Formerly FSI
Yotaibi @Yotaibi9
31 Followers 175 Following
C.T. @yFdn3kCdajMhxc_
1 Followers 49 Following
wpy1dlv0pdx3 @grq3d8km5
4 Followers 324 Following If you want to make friends, you can contact me anytime TG:https://t.co/FRK1aC86bP WS:https://t.co/yzS8veQBM2
Kartik @kartikhosamani
8 Followers 58 Following
عمران حیدر �.. @IftikharHa71994
1K Followers 3K Following •اِیَّاکَ نَعۡبُدُ وَ اِیَّاکَ نَسۡتَعِیۡنُ •
Yeti @Yeti_Sec
698 Followers 664 Following Sr. Malware Reverse Engineer & Threat Researcher, Unit 42 Threat Intelligence @unit42_intel | Ex-Incident Response. Opinions are my own.
Pascar Namusha @PascarN8302
21 Followers 28 Following
🄲🅈🄱🄴🅁 .. @Cyber_Asia_
3K Followers 349 Following Follow us for the latest #cybersecurity news in Asia Pacific.
Suryaan Dave @DaveSuryaan
64 Followers 344 Following
TheAnonNetwork @TheAnonNetwork
2K Followers 721 Following A witty character with a cloak of invisibility. #FreeAssange #MorpheuS #RedHack 👊👊
Atlas-Research @atlasresearch1
166 Followers 576 Following
Malware 505 @0xfff0x
21 Followers 66 Following
sockecito @sockecitoUy
48 Followers 101 Following
Irimsa Doorayd @idoorayd
45 Followers 173 Following
Piyush @piyushadge
3 Followers 49 Following
ouesleti oussema @ouesletious
14 Followers 114 Following
m.in_d @nacht0xff
31 Followers 487 Following …Computer ENG / #Cybersecurity geek / DFIR / SOC / blue as the sky above… { وَقُلْ رَبِّ زِدْنِي عِلْمًا }
Deepak Deepu @Deepak25R
109 Followers 615 Following eJPT | Cybersecurity | Crypto |CTF Player | CCNA |Networking
AM @Addy1504
28 Followers 314 Following CyberSec Analyst trying to figure it out Above&Beyond 🎧 No estoy en Twitter para pelear, solo estoy viendo muchas gracias 😝
vx-underground @vxunderground
291K Followers 210 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
Hacking Articles @hackinarticles
224K Followers 402 Following House of Pentesters Follow us: https://t.co/Y6XOlSOA92
MalwareHunterTeam @malwrhunterteam
219K Followers 36 Following Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.
mRr3b00t @UK_Daniel_Card
92K Followers 7K Following 真理的揭露者 Quis custodiet ipsos custodes fella in cyberspace #nafo undercover #FVEY Lovely Horse #fella #meme #farm #appreciator #cyber #specialist
Nicolas Krassas @Dinosn
122K Followers 735 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
OccupytheWeb @three_cube
219K Followers 4K Following Pentester, Forensic investigator, and former college professor. Trained hackers at every branch of US military and intelligence. Visit me at https://t.co/G478wufszw
The Hacker News @TheHackersNews
913K Followers 2K Following #1 Most trusted publication for breaking cybersecurity and hacking news, insights, and analysis for information security professionals.
BleepingComputer @BleepinComputer
212K Followers 175 Following Breaking cybersecurity and technology news, guides, and tutorials that help you get the most from your computer. DMs are open, so send us those tips!
Unit 42 @Unit42_Intel
51K Followers 88 Following The latest research and news from Unit 42, the Palo Alto Networks (@paloaltontwks) Threat Intelligence and Security Consulting Team covering incident response.
Jake Williams @MalwareJake
130K Followers 2K Following Breaker of software | GSE #150 | CTI/DFIR | @ians_security faculty | Bookings: jake at malwarejake dot com | He/him
Florian Hansemann @CyberWarship
75K Followers 47 Following Father, Founder @HanseSecure, Pentesting, Student, ExploitDev, Redteaming, InfoSec & CyberCyber; -- Mastodon: https://t.co/KFSKYUN98M
John Hammond @_JohnHammond
239K Followers 2K Following Hacker. Cybersecurity Researcher @HuntressLabs || https://t.co/qUeDM3lSCl
Karsten Hahn @struppigel
22K Followers 702 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
Binni Shah @binitamshah
131K Followers 175 Following Linux Evangelist, Malwares , Security Enthusiast, Philanthropist , Reformist , Jain. binitamshah at protonmail dot com
Alexandre Borges @ale_sp_brazil
23K Followers 111 Following Vulnerability Researcher and Exploit Developer
Germán Fernández @1ZRR4H
29K Followers 576 Following 🏴☠️ OFFENSIVE-INTEL 🏴☠️ Cyber Threat Intelligence by Hackers | Security Researcher en https://t.co/rDrSxZASB3 | @CuratedIntel Member | 🥷🧠🇨🇱
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
21K Followers 235 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
blackorbird @blackorbird
28K Followers 600 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Ptrace Security GmbH @ptracesecurity
53K Followers 883 Following Empowering IT Security Professionals through Hands-On Online Courses.
Trending GitHub Repos.. @trending_repos
18K Followers 0 Following Tweeting the most starred GitHub repository of the: 📈 day - every day 🏅 week - every Monday 🏆 month - every 1st of the month
Cyber Security Topics @Mawg0ud
4K Followers 4K Following Daily posts for cybersecurity analysts about: ➟ RedTeam ➟ Incident Response ➟ Digital Forensics ➟ Threat Intelligence .
Vangelis tix Stykas @evstykas
2K Followers 418 Following Father of two sons and ARIS fan. Named NOT A UNICORN!🦄 IDOR as a service. @_ifigeneia husband @atroposai jack of all trades Never ethical , mostly legal...
The Cyber Express @TheCyberExpress
2K Followers 389 Following The Cyber Express is a publication that provides latest news and analysis about the information security industry. #cybersecurity #cyberexpress #news
Robert Macfarlane @RobGMacfarlane
205K Followers 4K Following Books: Is A River Alive? (WIP) Underland, The Lost Words, The Old Ways, etc. | Films: River, Mountain, Upstream | Nature, climate, people | Prof @Cambridge_uni
Spectrum Bay News 9 @BN9
389K Followers 455 Following Breaking news first in Tampa Bay. Continuous updates and in-depth coverage only @BN9, @BN9weather and @BN9Traffic can provide | News. Weather. Now.
Pinellas County @PinellasGov
33K Followers 282 Following Pinellas County government's latest news, events, photos, video and general information. We're on the #GulfOfMexico and #TampaBay on the west coast of #Florida.
St. Petersburg, FL @StPeteFL
101K Followers 388 Following Official City of St. Petersburg account | #WeAreStPete
F5 DevCentral @devcentral
5K Followers 4K Following DevCentral is @F5 Online Community of Technical Peers dedicated to learning, exchanging ideas, and solving problems – Together https://t.co/LjhWST42Fz
F5 Labs @F5Labs
10K Followers 6K Following We process application threat data from @F5 and our partners into actionable intelligence. We analyze and share information to benefit the security community.
Spamhaus Technology @SpamhausTech
4K Followers 76 Following Spamhaus is the trusted authority on IP and domain reputation. This data not only protects but also provides insight across networks and email worldwide.
Threat Insight @threatinsight
10K Followers 228 Following @Proofpoint's insights on targeted attacks & the security landscape. Follow us on Mastodon: https://t.co/DT0pYpwuxy.
MalDev Academy @MalDevAcademy
11K Followers 5 Following A comprehensive module-based malware development course providing fundamental to advanced level knowledge
Lumu @lumutech
661 Followers 465 Following Lumu Technologies is a cybersecurity company that helps companies control the impact of cybercrime.
chum1ng0 @chum1ng0
4K Followers 4K Following #Chile-🇨🇱, Investigador Independiente cubro hacktivismo y filtraciones de datos en #LATAM y puedes encontrar mis noticias en:@_newschu y https://t.co/2nxsX7K3cE
N4hual @N4hualH
3K Followers 609 Following Independent Security Researcher. Cybercrime research with mexican flavor. La Libertad es lo único que importa. Data Junkie
ScamAdviser @scamadviser
17K Followers 27 Following https://t.co/Hik9HvATzt helps 2,5 million consumers every month to check if a website is legit and safe or a scam or fraud.
Transparency Internat.. @anticorruption
277K Followers 2K Following We are a global movement that wants to end the injustice of corruption worldwide 💙 #UnitedAgainstCorruption Imprint: https://t.co/x6HEZZoOBF
News about Hacks and .. @blue_leaks
3K Followers 195 Following Links to news & opinion on hacks, leaks & other interesting data from #DDoSecrets: #GreenhouseProject #Roskomnadzor #SEDENALeaks Tweets by @bbhorne & staff
ICIJ @ICIJorg
298K Followers 1K Following Stories that rock the world. We expose wrongdoing so the world can make it right. #CyprusConfidential #UberFiles #PandoraPapers #FinCENFiles #PanamaPapers
Organized Crime and C.. @OCCRP
173K Followers 2K Following It takes a network to fight a network. Exposing crime and corruption so the public can hold power to account. Support: https://t.co/osICI4Lcox RT ≠ endorsement
FloCon @FloCon_News
557 Followers 670 Following FloCon focuses on applying any and all collected data to defend enterprise networks. January 9-11, 2024
Ingrid Söllner @ISollner
404 Followers 372 Following CMO @Tehtris - Cybersecurity company offering the TEHTRIS XDR Platform (Omnichannel / Automated / Real Time #cyberdefense solution) #SecNum #InfoSec #FrenchTech
ShadowStackRe @ShadowStackRE
97 Followers 158 Following Developer, malware reverse engineer & exploit researcher.
Daily CTI @DailyCTI
3K Followers 14 Following Daily, get information about Cyber Threat Intelligence (CTI) like a pill 💊
Security Trybe @SecurityTrybe
161K Followers 106 Following A Platform For Cyber Security| Networking | Tech| Education|IG-https://t.co/iWeuXqOxRk
Jamie Williams @jamieantisocial
6K Followers 5K Following 🤘@mitreattack for Enterprise Lead, former ATT&CK Evals water distribution engineer (the artists known as #UNC1799), @DistrictHeather ♥️🍷, he/him.
Awesome @awesome__re
6K Followers 2 Following Community of curated awesome lists on GitHub. By @sindresorhus.
Sindre Sorhus @sindresorhus
62K Followers 528 Following Full-time open-sourcerer and maker of apps. Swift & Node.js. Made @awesome__re. Also: @sindre_gh_repos @[email protected]
FalconFeeds.io @FalconFeedsio
29K Followers 518 Following Democratizing Cyber Security. Threat intelligence platform for Cyber Security professionals and Small/medium business. Insights from Darkweb and Threat Actors.
VenariX @_venarix_
15K Followers 26 Following Beyond the Code: Universal cyber insights for everyone. Get the latest updates at https://t.co/xjBuuE25xr
Dutch Osint Guy Nico @dutch_osintguy
34K Followers 2K Following Dutch guy with Open Source Intelligence & Analysis skills • OSINT • #osintcurious • Certified Instructor & Author @SANSInstitute • Director @shadowdragonio
Malcolm @malkoegler
334 Followers 485 Following
CERT/CC @certcc
4K Followers 0 Following CERT Coordination Center at the Carnegie Mellon University Software Engineering Institute.
INCIBE-CERT @incibe_cert
40K Followers 88 Following Centro de Respuesta a Incidentes de Seguridad de referencia para los ciudadanos y entidades de derecho privado en #España operado por @INCIBE
CERT-FR @CERT_FR
55K Followers 40 Following Centre gouvernemental de veille, d'alerte et de réponse aux attaques informatiques. Pour toute question : [email protected] ou par téléphone au 3218 @ANSSI_FR
INTERPOL_Cyber @INTERPOL_Cyber
112K Followers 545 Following INTERPOL Global Cybercrime Programme aims to reduce the global impact of cybercrime and protect communities for a safer world. #YouMayBeNext
CERT-EU @CERTEU
15K Followers 450 Following Official account of the CERT for the EU institutions, bodies and agencies. Please use [email protected] for interaction.
CyberSec_EU 🇪🇺 @Cybersec_EU
23K Followers 1K Following Official EU account. We mainly focus on #cybersecurity/#infosec & #ePrivacy. Tweets by @EU_Commission-@DigitalEU cybersecurity & digital privacy team.
NSA/CSS @NSAGov
1.1M Followers 166 Following National Security Agency/Central Security Service official account, home to America's codemakers and codebreakers. Likes, retweets, and follows ≠ endorsement.
USCYBERCOM Cybersecur.. @CNMF_CyberAlert
69K Followers 93 Following This is Cyber National Mission Force’s alert mechanism to contribute to our shared global cybersecurity (Following, retweets and links do not equal endorsement)
OH SHINT! @ohshint_
10K Followers 649 Following Private Investigator in Meatspace. | #OSINT Specialist & #OPSEC Wizard. | #Surveillance & #TSCM Guru. | Cyber Security Enthusiast. | Certified #Cyberpunk. |
Cyber Hunter Academy @CyberHunterSec
9K Followers 202 Following No importa la edad o la experiencia previa, en Cyber Hunter Academy nos adaptamos a tus necesidades y tenemos cursos de todos los niveles. #OSINT #SOCMINT
Dreg @therealdreg
3K Followers 405 Following Senior Malware Researcher, OS Internals, C/C++, assembler, reversing, forensics, hardware hacking, x86_64, AVR, ARM & PIC
BSides SaoPaulo @bsidessp
2K Followers 162 Following Security BSides Conference in São Paulo, Brazil
NEC Brasil @necbrasil
850 Followers 403 Following Fornecedora de soluções de segurança e TIC para operadoras, empresas e governo. Subsidiária da NEC Corporation, com mais de 50 anos de experiência no Brasil.@MalwarePatrol Unfortunately, this type of attack contribute to the rise of medical identity theft, where criminals use stolen patient information to obtain medical services, and prescription drugs, or file fraudulent insurance claims.
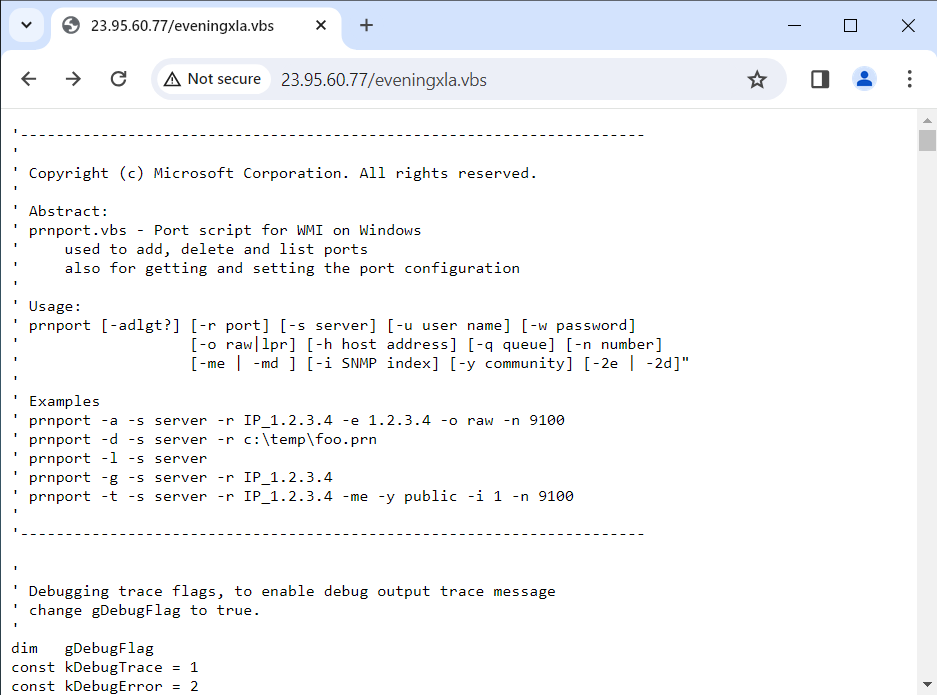
🚨 Malicious Excel File Evaded Most of the AV Solutions #AgentTesla🚨 📌 VT Detection: 4 / 62 🔐 MD5: fbe269e9e59772f738456bf0a165f0fd 🕵️♂️ IOCs: - http[:]//23.95.60.77 - http[:]//bun.is/08c72u DOCGuard Report: app.docguard.io/cc962c0a4622ba…
The disruption of the LabHost phishing service and the arrest of several key players puts a dent on the phishing operations of its many criminal clients. This should effectively reduce the number of phishing attacks globally for the time being. Read: ⬇️ research.trendmicro.com/LabHostTakedown
"🚨 Multi-Year Cyberattack: Chinese hackers suspected of breaching Volkswagen, unveiling espionage activities and stolen sensitive data. Implications for automotive industry and the need for robust cybersecurity measures. #Cybersecurity #Volkswagen #Chin… ift.tt/Mxo93Rm
⚠️@CISAgov issued 8 NEW public #ICS advisories. These advisories provide info about current security issues, vulnerabilities, & exploits surrounding ICS. More at cisa.gov/news-events/al…
Yesterday @TalosSecurity released a threat intelligence blog detailing the ArcaneDoor espionage-focused campaign. Microsoft Threat Intelligence collaborated with Cisco Talos to provide data and analysis on the threat actor Storm-1849 (UAT4356). msft.it/6015YJdzL
Kaiser Permanente: Data breach may impact 13.4 million patients - @billtoulas bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…
🚨 Attention #WordPress users! A critical SQL injection #vulnerability (CVE-2024-27956) in the WP-Automatic plugin is being actively exploited. With a max severity of 9.9/10, this bug enables site takeovers and malicious activities. Details: thehackernews.com/2024/04/hacker… #hacking
Our latest research provides a deep-dive analysis of Earth Hundun's Waterbear and Deuterbear malware families, offering valuable insights for cybersecurity professionals dealing with these threats. Click this link for the full story:⬇️ research.trendmicro.com/3PZzdnc
Beware of phishing attacks impersonating Korean portal websites, logistics brands, and webmail login pages. Threat actors are using actual source code to create nearly identical fake pages, making it crucial to avoid logging in through email attachments … ift.tt/6PCvy5j
United Nations Agency Investigating Ransomware Attack Involving Data Theft securityweek.com/united-nations…
#Oracle released its Critical Patch Update Advisory for April 2024. Users & admins are encouraged to review & apply the necessary updates. cisa.gov/news-events/al… #Cybersecurity #InfoSec
1/8: We provide interesting highlights from #OperationCronos’ disruption of #LockBit, the biggest financial #RaaS group of 2023. Follow this thread to discover key LockBit disruption takeaways. 🔻
Microsoft has tracked at least 70 Russian actors engaged in Ukraine-focused disinformation campaigns concentrated on undermining support for Ukraine. Meanwhile, China seeks to exploit societal polarization and diminish faith in US democratic systems: msft.it/6013Y8noc
Global law enforcement cracked down on LabHost phishing service! "Operation Nebulae" arrested 32 individuals, including UK masterminds. LabHost ran 40,000 domains, victimizing over 94,000 in Australia. Details here: thehackernews.com/2024/04/global… #hacking #cybersecurity
Avast discovered a new Lazarus campaign targeting individuals in the Asian region with fabricated job offers decoded.avast.io/luiginocamastr…
Frontier Communications shuts down systems after cyberattack - @serghei bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…
🚨 A new stealthy backdoor #malware called Kapeka, likely created by Russia's APT group Sandworm, has been targeting Eastern Europe, including Estonia and Ukraine. Learn more about this cyber threat: thehackernews.com/2024/04/russia… #cybersecurity #hacking
LabHost, a notorious phishing-as-a-service provider that has generated over a million pounds in revenue, has been taken down by law enforcement, with Trend Micro assisting in the investigation. Learn more about this operation in our latest blog: ⬇️ research.trendmicro.com/LabHostTakedown