Search results for #NetworkSecurity
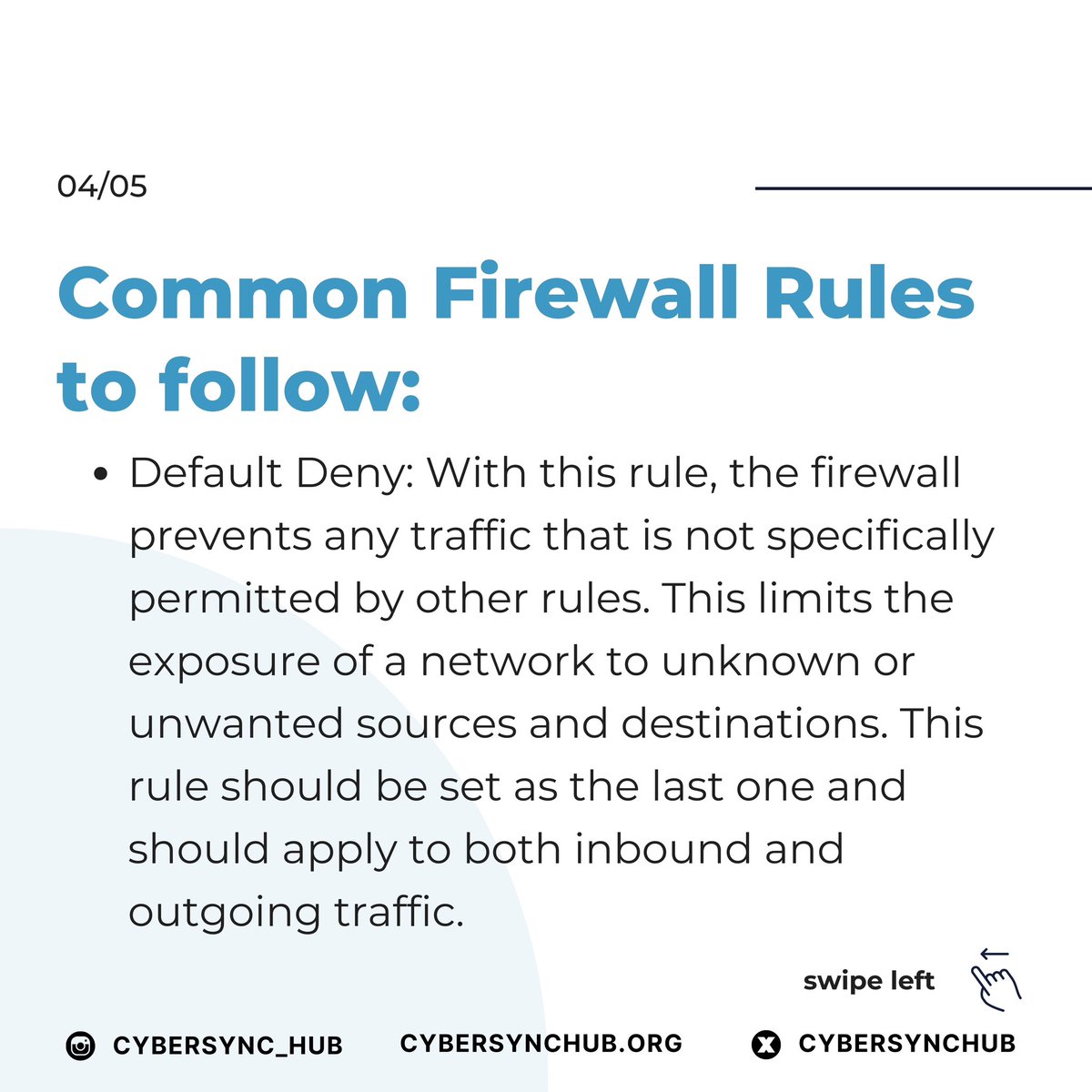
What do you think are the top 3 Firewall rules? Drop your comments below #Techtalk #Firewall101 #NetworkSecurity #CyberSyncHub
What do you think are the top 3 Firewall rules? Drop your comments below #Techtalk #Firewall101 #NetworkSecurity #CyberSyncHub
Cryptography and Network Security: Principles and Practice, 8th Edition, by William Stallings hackedexams.com/item/7489/cryp… #Cryptography #NetworkSecurity #PrinciplesandPractice #hackedexams
Top HTTP Status Codes 🔥🔥📌 #infosec #cybersecurity #pentesting #redteam #informationsecurity #cybersecuritytips #networking #networksecurity #infosecurity #cyberattacks #Security #Linux #cybersecurityawareness #httpstatus #bugbounty #bugbountytips #attacks #cyberattack
"Guest Lecture Delivered At The George Telegraph Training Institute" 📱+91 9934974671 / +91 9830108958 📧 Email us:- [email protected] Visit us:- tpdigitaltechnologies.com #websitedevelopment #websitedesign #itservices #networksecurity #guestlecture
A Network Packet Broker (NPB) is a device that optimizes traffic flow between TAP and SPAN connections and network monitoring, security, and acceleration tools. #NetworkVisibility #NetworkSecurity #TrafficOptimization #NetworkMonitoring visit us:-khushicomms.com
Discover the challenges telcos face in implementing customer security services and the advantages that converged security services give telcos. Read now👉 lp.allot.com/converged-secu… #cybersecurity #networksecurity #telcos
Looking for Linux Path Cheat Sheet? inbox now. #infosec #CyberSecurity #CyberSecuritytips #pentesting #oscp #informationsecurity #cissp #CyberSec #networking #networksecurity #CheatSheet #CloudComputing #vulnerabilities #linux #UNIX #NFTs
What you cannot see, you cannot secure. Leverage continuous discovery to gain asset visibility and avoid the expansion of the attack surface. bit.ly/4dhn3QK #cybersecurity #PAM #Discovery #networksecurity #accesscontrol #accessmanagement
How can security teams be ready for holiday cyberattacks and the seasonal peak in cybercrime? 🔗 tinyurl.com/4e2v47ra #cybersecurity #networksecurity
Securing access to your company’s network is not only important for the safety of your business, but also a requirement for most IT Security standards. Download your free Network Access Control Security Policy template today. hubs.li/Q02vqd2z0 #ControlCase #NetworkSecurity
Don't let complex network security jargon hold you back. #VirtualNetworkAppliances can be your secret weapon for securing your Azure network. Click to know more: lnkd.in/dbhpGNYc #AzureSecurity #CloudSecurity #NetworkSecurity #VNAs #HurixDigital
why a strong Cloud & Network Security strategy is essential for any organization 𝐖𝐞𝐛𝐬𝐢𝐭𝐞: bluechipgulf.ae #CyberSecurity #DataProtection #Compliance #BusinessContinuity #ReputationManagement #TrustworthyOperations #NetworkSecurity
Windows Exploitation: regsvr32 hackingarticles.in/windows-exploi… #infosec #CyberSecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #oscp #CyberSecurityawareness #bugbounty #bugbountytips
Windows Exploitation: msiexec.exe hackingarticles.in/windows-exploi… #infosec #CyberSecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #oscp #CyberSecurityawareness #bugbounty #bugbountytips
Windows Exploitation: msbuild hackingarticles.in/windows-exploi… #infosec #CyberSecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #oscp #CyberSecurityawareness #bugbounty #bugbountytips
Windows Exploitation: mshta hackingarticles.in/windows-exploi… #infosec #CyberSecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #oscp #CyberSecurityawareness #bugbounty #bugbountytips

NetworkSecurity News @NetworksecNews
390 Followers 25 Following News, updates, and opinions about network security.
Networksecurity @Networksecuri17
37 Followers 1 Following
NetworkSecurity @NetworkSafety
58 Followers 12 Following SafeMedia Corp. delivers the most powerful intrusion detection, prevention, mitigation, and monitoring capabilities.
NetworkSecurity @NetSecurity123
62 Followers 6 Following Future Ethical Hacker Bringing You Tips and Advice on Network Security
CyberInbox @cyberinbox
4K Followers 149 Following A single platform for all #CyberSecurity news & events. Stay updated on #EthicalHacking, #Infosec and #NetworkSecurity.
Allot Communications @allot_ltd
6K Followers 855 Following Provider of innovative #NetworkIntelligence, #NetworkSecurity, #CyberSecurity and converged security solutions for #telcos and enterprises worldwide.
Tufin @TufinTech
8K Followers 1K Following Tufin simplifies and automates the #security policy management of some of the largest, most complex networks in the world. #networksecurity
DCSO Deutsche Cyber-S.. @DCSO_de
799 Followers 31 Following Cyber Security Service Provider - https://t.co/e0SfdHb1kL #managedservices #cybersecurity #itsecurity #threatintelligence #networksecurity #threatdetection
NetworkSecurity @NetSec_UH
17 Followers 3 Following
networksecurity @ITK_Security
42 Followers 17 Following
128 Technology @128technology
1K Followers 370 Following We Help Companies Radically Reinvent Their Digital Future By Setting Their Network Free. #MultiCloud #Cloud #NetworkSecurity #SDWAN
networksecurity @secure_gateway
30 Followers 28 Following
networksecurity @netsecandmore
25 Followers 47 Following Todo lo que necesites para tu seguridad te la brindamos incluyendo tus datas.
Visual Edge IT @visualedgeit
820 Followers 151 Following Follow us for #managedITservices and #networksecurity news and information to guide your critical #databackup and #disasterrecovery decisions.
NetworkSecurity @NetworkSecur1ty
11 Followers 0 Following
Michael E Lemm @FreedomFireCom
2K Followers 1K Following Owner Of FreedomFire Communications & Retired Navy Vet...FREE Help With #NetworkDesign & Sourcing Of #Fiber, #5G, #SDWAN #NetworkSecurity, #Cloud, #IoT, #UCaaS
NetworkSecurity @meetsec
14 Followers 1 Following
Infowebica @infowebica
2K Followers 2K Following #CyberSecurity news website - How to secure yourself from #CyberThreats on #Internet & #SocialMedia. We write about #DataSecurity, #IoT, #NetworkSecurity. 🛡️
Great Bay Software @GreatBay_Beacon
2K Followers 2K Following We help #ITpros take back control of corporate networks to protect against #databreaches. #NetworkSecurity #IoT Blog at: https://t.co/KKUJCbMcnk
lnardo @lnardo
813 Followers 729 Following Product Manager #DB #Performance, #APM, #ITOps, #DevOps. #Automation #Security #NetworkAutomation #Compliance #CyberSecurity #NetworkSecurity father & #Sailing
NetworkSecurity News @mysecuritynews
19 Followers 57 Following Poster of #networksecurity news and reviews. Special focus on #sonicwall #cisco #juniper #watchguard and the latest threats.
DAP Report @DAPReport
1K Followers 2K Following Helps #analysts create #PenetrationTest and #securityReports for #Security #Assessment of their #NetworkSecurity
O2HS NETWORKSECURITY @O2HSco
19 Followers 112 Following Especializado a la atención y soporte técnico informático, instalación y programación de sistemas de seguridad electrónica, diseño de páginas y sistemas web.
Omega ATC @OmegaATC
1K Followers 1K Following Stay resilient against threats to your information and critical systems | #cybersecurity #infosec #networksecurity | [email protected] | 636-557-7777
IpowerAfrica @IpowerAfrica
1K Followers 1K Following Solving Business Problems w/ Tech Solutions IT Services, & Consulting #ICTSecurity #NetworkSecurity #PowerAfrica #Solar #remittance #InfoSec #DataFirst
Integra Networks @IntegraCanada
1K Followers 2K Following Canada’s leading source of #IT Business Solutions. #Virtualization #PrivateCloud #NetworkSecurity #HCI #DevOps #BusinessContinuity #DataCenter #HybridCloud
Tirtha Acharya @BardiyaKoBagh
1K Followers 867 Following An IT Entrepreneur. Co-Founder @cloudtechnepal #ManagedWiFi #NetworkSecurity #SystemIntegration. RT's ARE endorsement.
Scuba Matt @ScubaMatt01
862 Followers 2K Following Expert on #CrohnsDisease | #IoT & #ITtraining #NetworkSecurity | #Geek | Life is about The Little Things #tweet4taiji | Business Owner