Marius A @bigalbulescu
Interests: CyberSecurity; Cryptography; TI/AFS/AML/IoT/ AI/BTC; Technology/Gadgets...Red Wine&BlackBerry, Photographer/Tennis player...Never Give Up!!!...🍷💰🍀 Bucharest/ London Joined June 2009-
Tweets24K
-
Followers889
-
Following4K
-
Likes10K
👨🏫 Ce pași trebuie să urmați atunci când realizați că ați căzut victimă unei fraude online, iar datele dvs. de card au intrat în posesia atacatorilor? 🔗 dnsc.ro/vezi/document/… #DNSC #cyber #awareness #SigurantaOnline
Check Point's Alexey Bukhteyev & Arie Olshtein provide insights into GuLoader's evolution. GuLoader is a prominent shellcode-based downloader, active for more than 3 years, that has been used in a large number of attacks to deliver a wide range of malware. research.checkpoint.com/2023/cloud-bas…
State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage (Not fully accurate, Cisco doesn't know what is the initial point of entry) thehackernews.com/2024/04/state-…
New stealthy #malware campaign exploits 2 ZERO-DAY flaws in Cisco devices, enabling covert data collection & reconnaissance by a state-sponsored actor. Details: thehackernews.com/2024/04/state-… "Line Runner" and "Line Dancer" implants allow config changes and traffic capture.
Indian bank’s IT is so shabby it’s been banned from opening new accounts go.theregister.com/feed/www.there…
''From Error to Entry: Cracking the Code of Password-Spraying Tools'' #infosec #pentest #redteam #blueteam trustedsec.com/blog/from-erro…
Hackers Infect Users with AV Software arstechnica.com/security/2024/…
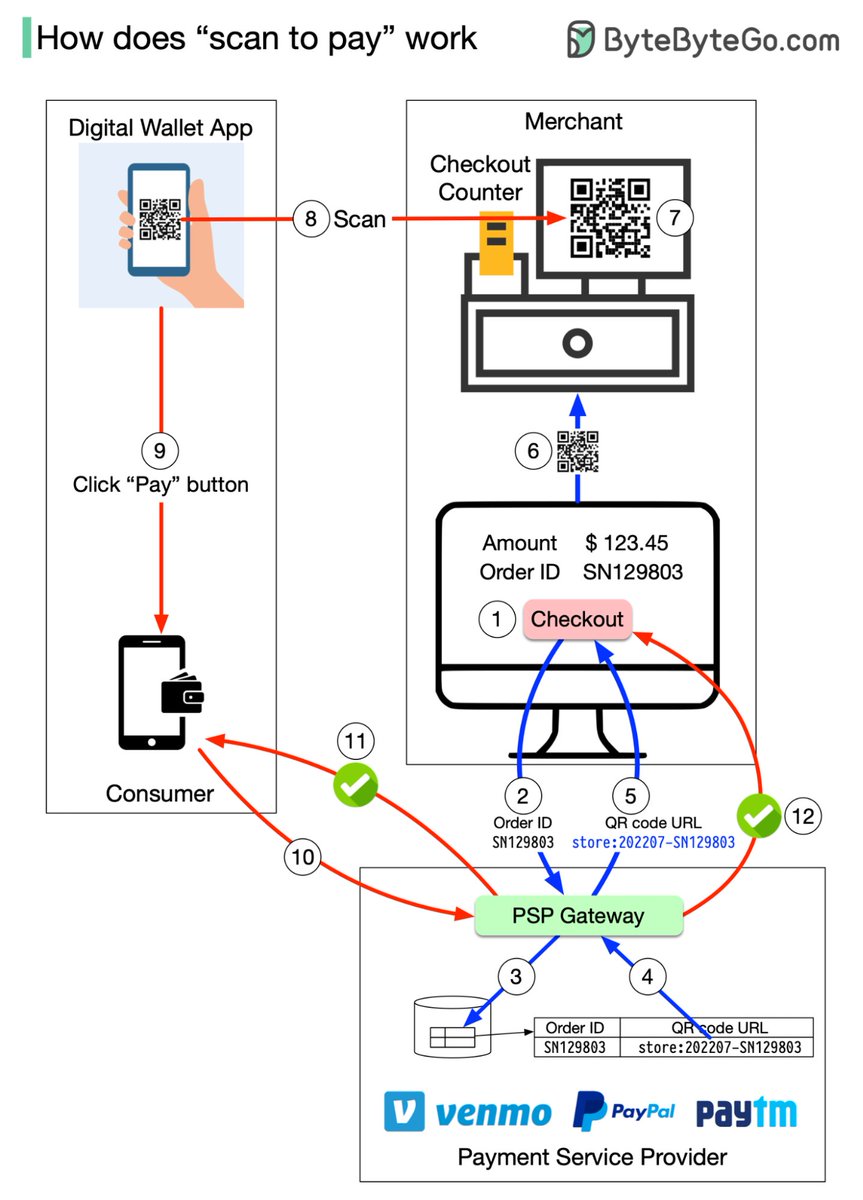
How do you pay from your digital wallet, such as Paypal, Paytm and Venmo, by scanning the QR code? To understand the process involved, we need to divide the “scan to pay” process into two sub-processes: 1. Merchant generates a QR code and displays it on the screen 2.…
ArcaneDoor hackers exploit Cisco zero-days to breach govt networks bleepingcomputer.com/news/security/…
How i Manage to Get Sensitive Informations via docker image medium.com/@ph-hitachi/ho…
Congress voted to expand Section 702 of #FISA, part of the warrantless surveillance programs exposed by @Snowden. This effectively grants U.S. agencies access to the communications equipment of almost any U.S. business to spy on foreigners and Americans: proton.me/blog/us-warran…
🔑 În ciuda precauțiilor pe care le luăm, conturile noastre de social media pot fi compromise. 🔐 Cele 3 aspecte esențiale de securizare a unui cont în aceste situații, în materialul de mai jos. #DNSC #cyber #awareness #SigurantaOnline
🌐 După compromiterea unui cont online, posibilitatea de recuperare a acestuia depinde de măsurile de securitate luate anterior. Dar există anumite acțiuni care ar trebui făcute de fiecare dată când ne pierdem conturile. #DNSC #cyber #awareness #SigurantaOnline
Microsoft releases Exchange hotfixes for security update issues - @serghei bleepingcomputer.com/news/microsoft… bleepingcomputer.com/news/microsoft…
With HPKE (Hybrid Public Key Encryption), Alice just needs to send Bob her public key, and then Bob can create a cipher using a range of symmetric key methods (AEAD), Key Derivation Functions (KDF), and Key Exchange Mechanisms (KEM): asecuritysite.com/circl/go_hpke2
Your Data is not Safe! Protect it from anyone! youtu.be/JVx9YAaTp9w?si…
Major Security Flaws Expose Keystrokes of Over 1 Billion Chinese Keyboard App Users thehackernews.com/2024/04/major-…
🛜 Este esențial să adoptăm practici eficiente în utilizarea aplicațiilor de acces la distanță pentru a ne asigura că activitățile noastre sunt desfășurate în siguranță. 🔗 dnsc.ro/vezi/document/… #DNSC #SigurantaOnline #awareness
A new variant of RedLine Stealer, an information-stealing #malware, has emerged using Lua bytecode to enhance its ability to evade detection. It is being distributed via repositories on #GitHub disguised as game cheats. Details: thehackernews.com/2024/04/new-re… #cybersecurity

Dan Cimpean @DanCimpean
3K Followers 4K Following Romanian National Cyber Security Directorate, Risk, Digital, Cloud, Policy, Assurance, OSINT, Tech, European Institutions, Brussels, Bucharest, Personal Views
Karol Farris @farris_kar49864
64 Followers 5K Following
Isabella-rose Vandeya.. @IsabellaRo62739
46 Followers 5K Following
Reta Carithers @CarithersR2524
69 Followers 5K Following
Summer Kottman @kottm_sum
98 Followers 5K Following
Yasmin Rochenstire @YRochenstir
42 Followers 5K Following
Sherril Heffler @SherriHeffl
20 Followers 3K Following
Angel 😌 @Angel_Emery23
3 Followers 500 Following Lust-fillеd gоddess chаsing everlasting grаtifiсatiоn
Yvone Drayer @DrayerYvon35455
75 Followers 5K Following
Luna Wescovich @lun_wescov
50 Followers 5K Following
Jorja Dase @DaseJor
56 Followers 5K Following
EdieBibo @BiboEdie89367
4 Followers 669 Following
Adele Vanzante @vanzante72618
72 Followers 5K Following
Halle Restrepo @HalleRestr2858
55 Followers 5K Following
Lyla Leab @LeabLyla20350
58 Followers 5K Following
Aundrea Scarff @scarf_aund
41 Followers 5K Following
Julissa Kaiwi @julissa_ka
49 Followers 5K Following
Claretha Wiltbank @ClarethaW33339
77 Followers 5K Following
Chandra Dalpe @ChandraDal10422
41 Followers 5K Following
Starr Aldaba @AldabaStar92761
24 Followers 5K Following
Virginia Schenkel @VirginSchenke
66 Followers 5K Following
Cara Bollin @BollinCara26137
69 Followers 5K Following
Jannette Brickner @JannetBrickne
70 Followers 5K Following
Aida Sieligowski @SieligowsAid
30 Followers 5K Following
Ameera Burgher @BurgheAmee
10 Followers 3K Following
Kip Norman @Chopalop
1K Followers 4K Following Music listener, dog walker and dog nanny. Enemy of the stupid and running junkie. Three #Tseks full sir
Gussie Mcphillips @McphillGussi
62 Followers 5K Following
Théophile Bita @TheophileBita
22 Followers 189 Following 💻Ir. informaticien passionné par la technologie et l'innovation. Fort d'une solide expertise dans le développement de logiciels et de systèmes...
Fermina Annen @an_fermi
27 Followers 5K Following
Eliyah Stork @EliyahSto
41 Followers 5K Following
Peggy Mellard @MellardPeg11508
48 Followers 5K Following
Mirabelle @DeliaI336803
5 Followers 205 Following Love life, enjoy traveling, enjoy different landscapes and cultural history (hope to meet friends with common interests)
Sirena Dambrosi @DambrSire
57 Followers 5K Following
Marwa Bredehoft @BredehoftM30940
48 Followers 5K Following
Lavern Dino @lave_din
49 Followers 5K Following
Casey Aldrich @CaseyAldri
49 Followers 5K Following
Ozie Yanity @yanit_oz
41 Followers 5K Following
Margaret Rauda @rauda_ra
74 Followers 5K Following
Louis Tomos Evans @LouisTomosEvans
1K Followers 3K Following 👋 Founder of Hunt Intelligence → https://t.co/lYWE0SBwgx Focused on building innovative and user-friendly OSINT Tools for everyone to use.
Stella Cecala @cecal_ste
14 Followers 2K Following
vx-underground @vxunderground
291K Followers 210 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
DefCamp @DefCampRO
2K Followers 565 Following Building valuable, hands-on learning experiences for 2000+ #cybersecurity specialists from all over the world. Join us to educate, secure & change the world!
Dan Cimpean @DanCimpean
3K Followers 4K Following Romanian National Cyber Security Directorate, Risk, Digital, Cloud, Policy, Assurance, OSINT, Tech, European Institutions, Brussels, Bucharest, Personal Views
Ioan-Cosmin Mihai @ICMihai
282 Followers 126 Following Elevating cybersecurity proficiency, enhancing digital skills, and empowering law enforcement experts to excel in fighting cybercrime
Directoratul Naționa.. @DNSC_RO
4K Followers 555 Following Directoratul Național de Securitate Cibernetică (DNSC) The Romanian National Cyber Security Directorate (DNSC) https://t.co/p9RxfoyITb
MApN @MApNRomania
36K Followers 297 Following Contul oficial de Twitter al Ministerului Apararii Nationale
SSSCIP Ukraine @SSSCIP
14K Followers 386 Following State Service of Special Communications and Information Protection of Ukraine | Державна служба спеціального зв’язку та захисту інформації України 🇺🇦
ENISA @enisa_eu
53K Followers 942 Following Official Twitter channel of the European Union Agency for Cybersecurity (ENISA) 🇪🇺 | RTs ≠ endorsement
Daniel Kelley @danielmakelley
40K Followers 557 Following Reformed Black Hat Computer Hacker • Contributed To 100+ Bug Bounty Programs⚡100K+ Audience
Matthew @embee_research
12K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
LuemmelSec @theluemmel
6K Followers 485 Following I speak BloodHound. Husband, Father, IT-Guy, Security-Noob Blog: https://t.co/PXB35KEqs6 GitHub: https://t.co/Unp9jZOpBn
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 568 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger | Stronger Together |
Clandestine @akaclandestine
35K Followers 5K Following | Security | Osint | Threat Research | Opsec | Threat Intelligence | Infosec | Threat Hunting |
Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
nixintel - nixintel@b.. @nixintel
23K Followers 1K Following Steven Harris | OSINT & Cyber Security Specialist | Investigator | Teach OSINT @SANSInstitute | Ex @OSINTCurious | https://t.co/EGO8CWyA6H
Alexandre Borges @ale_sp_brazil
23K Followers 111 Following Vulnerability Researcher and Exploit Developer
Hermix @Hermix_sw
14 Followers 34 Following https://t.co/dxt92vI7OT is the first analytics platform for public sector sales- and bid managers. Contact us for your free demo👇
Stefan Morcov @stemrv
64 Followers 118 Following IT/Software engineer migrated to management, marketing and sales. EU projects, new tech, innovation, AI, complexity, eLearning.
Félix Aimé @felixaime
6K Followers 2K Following Threat Intelligence stakhanovite ⛏️ and proud dad. Former @Kaspersky & @CERT_FR. Now state-sponsored threats CTI lead at @sekoia_io.
PETS @PET_Symposium
6K Followers 69 Following Official account of the Privacy Enhancing Technologies Symposium. Next event: PETS 2024, July 15-20, Bristol, UK and Online.
Compass Security @compasssecurity
3K Followers 116 Following Penetration Testing, Red Teaming, Incident Response, Bug Bounty, Security Training, Cyber Range
Mullvad.net @mullvadnet
32K Followers 1 Following A fast, trustworthy, and easy-to-use VPN is a good first step toward reclaiming your privacy. Just €5/month. // Need help? Email [email protected]
HydrAttack @EASM_HydrAttack
29 Followers 1 Following The official twitter channel for EASM HydrAttack
France Travail @FranceTravail
73K Followers 5K Following Compte X officiel de France Travail #OnEstLàPourVous #AvecFranceTravail (Pour une réponse adaptée à votre situation, contactez votre conseiller)
Anthropic @AnthropicAI
262K Followers 26 Following We're an AI safety and research company that builds reliable, interpretable, and steerable AI systems. Talk to our AI assistant Claude at https://t.co/aRbQ97uk4d.
UK Financial Intellig.. @NCA_UKFIU
3K Followers 494 Following Receives financial intelligence from Suspicious Activity Reports. Don't report crimes on Twitter. Call 101 or 999 for emergencies. Not monitored 24/7
W.R. Schock, QBD @iontecs_pemf
21K Followers 2K Following iontecs Quantum Biodynamics *Developing next-level Blochchain Tesla PEMF *Multiple quantum physics patents *Inventor Vortex Chillers *Employer/engineer/designer
Amazon Web Services @awscloud
2.2M Followers 465 Following The official account for Amazon Web Services (#AWS). ☁️ For help, please contact: @AWSSupport
LaurieWired @lauriewired
30K Followers 204 Following Reverse engineer specializing in cross-platform malware analysis with a focus on mobile threats.
ICI Bucharest @ICIBucharest
775 Followers 40 Following The National Institute for Research - Development in Informatics - ICI Bucharest #cybersecurity #digitalforensics #IT #research #HPC #cyberdiplomacy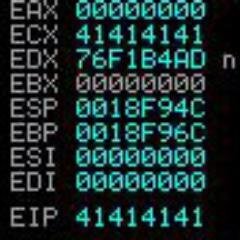
Hyp3rlinx @hyp3rlinx
2K Followers 51 Following Security Researcher, I exploit what I wanna exploit ... I exploit what I like..
Matthias Kirschner @kirschner
2K Followers 0 Following @FSFE's president. Working for #FreeSoftware, so every individual can self-determined use, study, share, and improve software. ➡️ @[email protected]
Free Software Foundat.. @fsfe
27K Followers 0 Following Free Software Foundation Europe is a charity that empowers users to control technology. Follow us in the Fediverse! @[email protected]
Aalto University @AaltoUniversity
54K Followers 1K Following Aalto University (Aalto-yliopisto) is a multidisciplinary university, where science and art meet technology and business. #AaltoYliopisto #AaltoUniversity
James Warner @jmswrnr
11K Followers 2K Following 👨🏻💻 Creative Web Developer 🏢 Prev at @LEGO_Group, @EA
Notion @NotionHQ
463K Followers 4K Following The connected workspace for your docs, projects, and knowledge.
Skiff @skiffprivacy
34K Followers 358 Following Private, end-to-end encrypted, and open-source mail, calendar, notes, and drive. Now part of Notion.
OSINT Combine @osintcombine
20K Followers 681 Following We are leaders in Open Source Intelligence training and services in Australia. #OSINT
Günter Born @etguenni
2K Followers 429 Following IT-Aut(h)or, (Security-)Blogger, Ex MS MVP Borns IT- & Windows-Blog & Impressum https://t.co/GQlOVFKOr9 EN: https://t.co/ftBN7x2zqX Mastodon: https://t.co/vid1NWayaJ
Amnesty International @amnesty
2.2M Followers 4K Following We defend human rights around the world. No government is beyond scrutiny. No situation is beyond hope. Let's get to work!
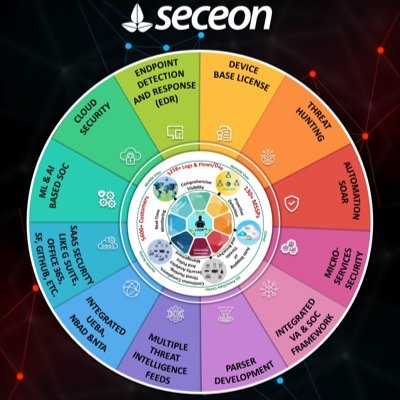
CyberKnight @CyberKnightME
343 Followers 117 Following Cybersecurity focused value-added-distributor (VAD) covering the Middle East. Our ZTX methodology incorporates solutions that protect the entire attack surface.
BBC World Service @bbcworldservice
560K Followers 747 Following News, views and highlights from the BBC's international radio station.
The OSPAs @theOSPAs
2K Followers 945 Following The Outstanding Security Performance Awards (#OSPAs) recognise and reward outstanding performance across the security sector https://t.co/uLEsF6croG
The Tennis Letter @TheTennisLetter
90K Followers 989 Following Want to know the 411 & keep up with all the hot gossip? Look no further. ATP/WTA news, history, & memes | https://t.co/4fsyjojBzS
The Straits Times @straits_times
1.3M Followers 132 Following Stay in the know with the latest news from Singapore and around the world. Breaking news | Exclusives | Opinion 📧: [email protected] 📱: https://t.co/yTmX7znOOT
SES @SES_Satellites
27K Followers 1K Following As the leader in global content connectivity solutions, we connect more people in more places with content that enriches their personal stories.
0sintSir🕵🏻�.. @ronkaminskyy
652 Followers 94 Following Senior Dark Web & CTI Analyst @rapid7 | Blogger | Veteran | OSINT, GEOINT, CTI Addict. Opinions are my own🥷🏼 #osint #threatintel #darkweb #humint #geopolitics
Framework @FrameworkPuter
68K Followers 123 Following Remaking consumer electronics to respect people and the planet. Now shipping the Framework Laptop in 🇺🇸🇨🇦🇬🇧🇩🇪🇫🇷🇳🇱🇮🇪🇦🇹🇦🇺🇧🇪🇮🇹🇪🇸🇹🇼🇵🇱
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
Authy @Authy
15K Followers 190 Following Simple & secure 2-Factor Authentication Get App or API: https://t.co/BIS5EorYPp For Support: @AuthyHelp or https://t.co/slIXYYiMr6
About Privacy @aboutprivacyNL
3K Followers 357 Following https://t.co/Xn5QOpSs6z is de online privacygids met tips & tools over privacy en cybersecurity | The Dutch Privacy Guide. Tweets in NL and (mostly) EN
clif @clif_high
146K Followers 29 Following radical iconoclast ~ Time powers everything. Harmonize with Irreversiblity.
Eunice D Wong 🦄 @Eunicedwong
169K Followers 1K Following I ONLY HAVE THIS ACCOUNT! Crypto Trader. No leverage, I post real-time crypto signals for free here 🚀 Not financial advice🧘🏼♀️11:11✨🪬🪬 Alhamdullilah ☪️
Davinci Jeremie @Davincij15
603K Followers 308 Following I told you to buy #Bitcoin for $1 in 2011. Don’t miss it again! ETH=0x94e9A5A128f7B4af0BEeFe32F411F61d244759cE SOL=4ekSqR4pNZ5hp4cRyicji1Yj7ZCphgkYQhwZf2ib9Wko
CoinMarketCap @CoinMarketCap
6.3M Followers 440 Following #CMC is the world's most trusted source of crypto data, insights & community. Start your crypto journey at https://t.co/fJ6p40tTvW
CZ 🔶 BNB @cz_binance
9.0M Followers 2K Following @binance co-founder and former CEO, holder of #bnb #btc
The Calyx Institute @calyxinstitute
10K Followers 1K Following Nonprofit that develops & researches #privacy tech + education to address #digitaldivide & promote free expression. + @CalyxOS @[email protected]
Alisa Esage Шевч�.. @alisaesage
35K Followers 142 Following Hacker & Founder @zerodaytraining • First Female Winner Pwn2Own • Solo Entrepreneur • Student of Physics
THORChain @THORChain
244K Followers 2K Following Decentralised L1 Liquidity Protocol ⚡️Swap, Earn, & Borrow - BTC, ETH, BNB, Cosmos & more ⚡️Infrastructure for top wallets & exchanges Community managed account
Microsoft Threat Inte.. @MsftSecIntel
180K Followers 1K Following We are Microsoft's global network of security experts. Follow for security research and threat intelligence.
First Squawk @FirstSquawk
310K Followers 250 Following Firstsquawk Is a Global Financial (News) Squawk Service Specialising In Financial Markets.
Insider Paper @TheInsiderPaper
351K Followers 1 Following Insider Paper is your source for Breaking News and Developing Stories.
Dragoș Tudorache @IoanDragosT
4K Followers 383 Following MEP (Renew Europe, Romania); Chair Special Committee on AI; LIBE rapporteur on AI Act; former Interior Minister and DG HOME Head of Unit.
ECTEG 🇪🇺 @ecteg
3K Followers 706 Following European #Cybercrime Training and Education Group 🇪🇺 #Europe #LawEnforcement #nonprofit #training #CapacityBuilding Funded by @EUHomeAffairs #securityEU #ISFCelebrating ILEA Day! I am proud to be an ILEA alumnus, having graduated from the "Law Enforcement Executive Development" program, organised by the International Law Enforcement Academy - Budapest (ILEA). I'm grateful for the invaluable skills and connections I gained.
We've partnered with National Security Services Group in Oman. NSSG will now offer our cutting-edge solutions like Threat Intelligence and Fraud Protection, alongside services such as Digital Forensics and Incident Response. eu1.hubs.ly/H08QnQM0
👨🏫 Ce pași trebuie să urmați atunci când realizați că ați căzut victimă unei fraude online, iar datele dvs. de card au intrat în posesia atacatorilor? 🔗 dnsc.ro/vezi/document/… #DNSC #cyber #awareness #SigurantaOnline
Join our webinar on Hyper-optimizing EU public tenders with AI. We would love to see you. When? • 18 April, 11h CET, on Zoom Meetings. See you in a week ⌛️ Register now: us06web.zoom.us/webinar/regist…
🔑 În ciuda precauțiilor pe care le luăm, conturile noastre de social media pot fi compromise. 🔐 Cele 3 aspecte esențiale de securizare a unui cont în aceste situații, în materialul de mai jos. #DNSC #cyber #awareness #SigurantaOnline
🌐 După compromiterea unui cont online, posibilitatea de recuperare a acestuia depinde de măsurile de securitate luate anterior. Dar există anumite acțiuni care ar trebui făcute de fiecare dată când ne pierdem conturile. #DNSC #cyber #awareness #SigurantaOnline
With HPKE (Hybrid Public Key Encryption), Alice just needs to send Bob her public key, and then Bob can create a cipher using a range of symmetric key methods (AEAD), Key Derivation Functions (KDF), and Key Exchange Mechanisms (KEM): asecuritysite.com/circl/go_hpke2
Together with the trainers of the CEPOL Mac Forensics course. Their mission is vital: to strengthen the capabilities of law enforcement investigators in Mac forensics. Wishing them great success in this training activity!
🛜 Este esențial să adoptăm practici eficiente în utilizarea aplicațiilor de acces la distanță pentru a ne asigura că activitățile noastre sunt desfășurate în siguranță. 🔗 dnsc.ro/vezi/document/… #DNSC #SigurantaOnline #awareness
As cryptography moves into data coding areas, get those data communication books dusted down. Here's PSK, ASK and FSK: asecuritysite.com/comms/plot03
Our sun is one of 100 billion stars in our galaxy. Our galaxy is one of billions of galaxies populating the universe. It would be the height of presumption to think that we are the only living things in that enormous immensity. - Wernher von Braun
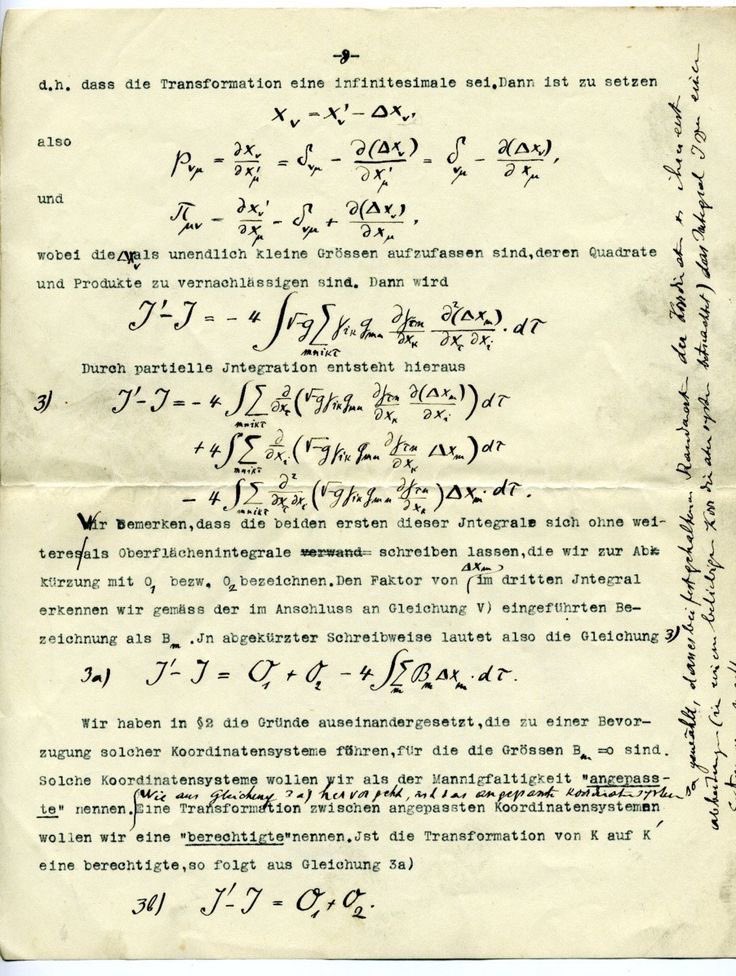
The concept of logarithms was invented by John Napier, a Scottish mathematician, who introduced them in 1614. Napier published his discovery in a book titled Mirifici Logarithmorum Canonis Descriptio (Description of the Wonderful Rule of Logarithms), which explained how…
As of today, we made free #ProtonVPN servers available in #Chad ahead of the presidential elections on May 6th. We want to ensure everyone has free and unrestricted access to information and prevent any potential attempts of interference or misinformation campaigns. ➡️ Learn more…
With the BLS sig, we can generate two random key pairs, which are used to sign two messages. F Bob has a message & Alice has another message. We can then generate two sigs and then aggregate them together. We can then check against the public keys: asecuritysite.com/signatures/go_…
A new feature on our Security Center helps improve your protection from cyber threats by alerting you about #databreach! Dark Web Monitoring is available to all paying users of #ProtonMail. #darkweb x.com/protonmail/sta…
Stay safe from cyber threats! Dark Web Monitoring is available to all paying users of #ProtonMail. If you register for an online service that gets hacked or suffers a #databreach, Proton will now alert you, so you can take immediate action. 1 / 2
🇹🇩 Săptămâna trecută, echipa DNSC a participat la Bruxelles la '2nd @enisa_eu Cybersecurity Policy Conference 2024 (EUCPC 2024)', eveniment ce a oferit din nou ocazia ca factorii de decizie de rang înalt din UE, reprezentanții industriei de profil, mediul academic și alte părți
Researchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers thehackernews.com/2024/04/resear…
Boneh–Lynn–Shacham (BLS) signature method produces short signatures. They use elliptic curve pairing (and which are also known as bilinear maps), and can be used to aggregate signatures: asecuritysite.com/signatures/go_…
#ToddyCat APT target government entities in Asia-Pacific region We publish a new research about a range of tools the actor utilizes for data extraction (specifically, documents, WhatsApp web credentials and passwords stored in browsers), and establishing stable and stealthy…