Andy Robbins @_wald0
Product Architect of BloodHound Enterprise. Co-creator of BloodHound. Please donate to MDA: https://t.co/wtLm1eFzRc. He/him. @SpecterOps. Mstdn: @[email protected] wald0.com Seattle, WA Joined March 2011-
Tweets5K
-
Followers37K
-
Following2K
-
Likes5K
Published part 2 of Manual LDAP Querying. This blog covers additional topics like user account control, password attributes, domain trusts, and more. posts.specterops.io/manual-ldap-qu…
This is such an awesome writeup, but it's missing one thing - remediation steps Some AD admins may know how to fix these issues, but it's fair to assume some do not. I'd also highly recommend using PingCastle by @mysmartlogon as it audits most of this and more. Thread time!
This is such an awesome writeup, but it's missing one thing - remediation steps Some AD admins may know how to fix these issues, but it's fair to assume some do not. I'd also highly recommend using PingCastle by @mysmartlogon as it audits most of this and more. Thread time!
Here is how we have implemented the golden certificate and ADCS ESC3 abuse narratives in BloodHound 🔎🐕
Here is how we have implemented the golden certificate and ADCS ESC3 abuse narratives in BloodHound 🔎🐕
After 4 months of testing/peer-review and the PR being in draft, dacledit is now ready for official review and merge in Impacket 💪 This script can be used to read, write, remove, backup, restore ACEs in an object's DACL, see you soon when merged 😊 github.com/SecureAuthCorp…
It's a big day- @tifkin_, @0xdab0, and I are proud to announce that Nemesis 1.0.0 has landed! We have a ton of awesome new features and a streamlined installation, check out the details at posts.specterops.io/nemesis-1-0-0-… and the code at github.com/SpecterOps/Nem…
Last year I shared how to convert BloodHound JSON to PowerShell objects. Here's a proper function: ConvertFrom-BHJSON gist.github.com/martinsohn/1f3… Examples in this new 🧵
Last year I shared how to convert BloodHound JSON to PowerShell objects. Here's a proper function: ConvertFrom-BHJSON gist.github.com/martinsohn/1f3… Examples in this new 🧵
Nice if you want to play around with BH data inside PowerShell. Thx @martinsohndk for sharing this gem
Nice if you want to play around with BH data inside PowerShell. Thx @martinsohndk for sharing this gem
We are hosting a #BloodHound users meetup next week: Location: 11000 Optum Cir, Eden Prairie, MN Date/time: May 2 from 4PM to 7PM Cost: free Register here: ghst.ly/442MNfk
I just published a blog and tool for the LSA Whisperer work that was presented at the SpecterOps Conference (SOCON) back in March. If you are interested in getting credentials from LSASS without accessing its memory, check it out! medium.com/specter-ops-po…
Heading to #MMSMOA next month? Make sure to add this session to your schedule. @_Mayyhem will be joining @TheWMIGuy & @TomDegreef to speak on how to secure your ConfigMgr environment & defend against publicly known attacks. Learn more ➡️ ghst.ly/4459csL #SCCM
Shoutout to @m4lwhere on this comprehensive guide to getting started in BloodHound Community Edition. Check out his blog post that covers setting up, collecting data, analyzing the data & providing value with that data. ghst.ly/3JlkvmO
If you want to get started with BloodHound CE, then I highly recommend reading this awesome blog post by @m4lwhere. It's a great resource to kickstart your journey! m4lwhere.medium.com/the-ultimate-g…
👋 Hello, Nashville! If you’re at #WiCyS2024 come by Booth 228 to chat with a few Specters and learn more about us.
I wrote a script to identify every TAKEOVER and ELEVATE attack in Misconfiguration Manager that can be run with Read-only Analyst privileges or higher in SCCM. Please share with your IT admins, defenders, clients, assessors, and friends in infosec! posts.specterops.io/rooting-out-ri…
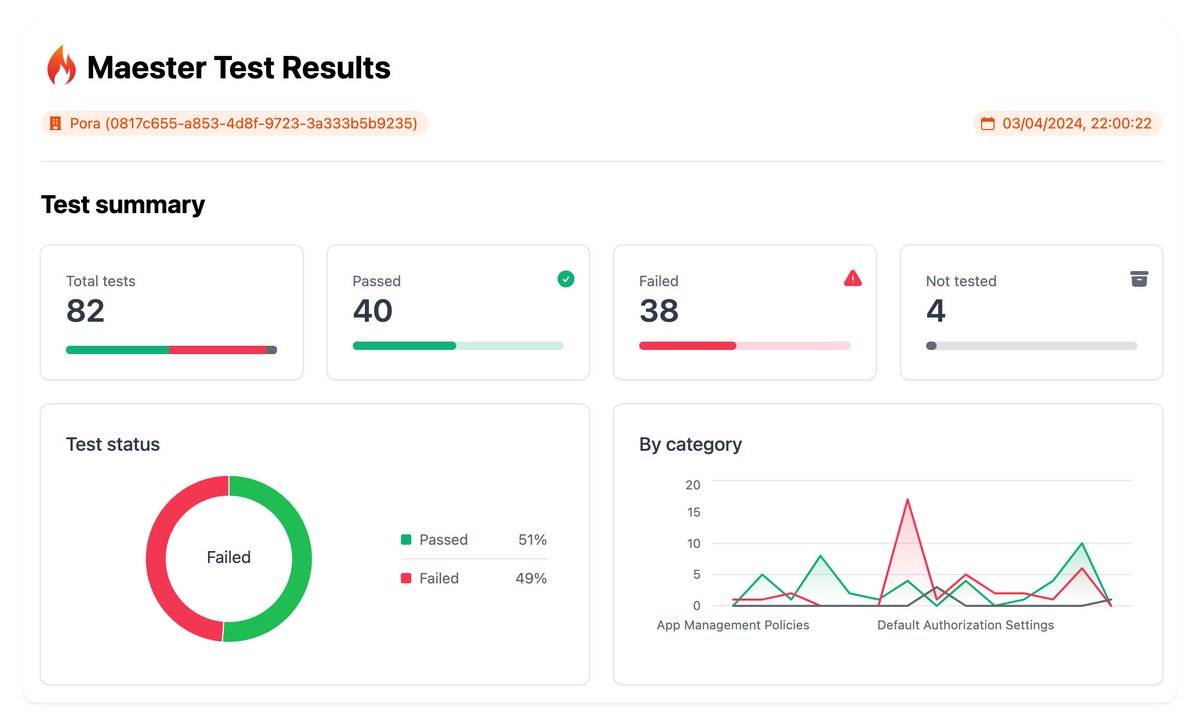
🥳 🎉 Folks, @fabian_bader, @Thomas_Live & I are excited to launch Maester today after working on this over many long nights & weekends! Maester is an open source, test framework that you can set up in minutes to test & continuously monitor your Microsoft security config 🧵⬇️
Heading to #WiCyS2024 this week? We are too! Stop by Booth 228 to meet our team and learn more about us and how you can become a Specter.
Entra Connect Sync lets you exclude *specific* users from synchronization using attribute-based filtering. Does Entra Cloud Sync have a similar feature? I can see filtering by group and OU. But is there an *attribute* based filter to exclude *specific* users from sync?
Is it possible to conduct AiTM phishing attacks with Azure Functions to phish Entra ID sign-in cookies? Spoiler: Yes it is. And we can bypass injected canary tokens and automate the replay😶🌫️nicolasuter.medium.com/aitm-phishing-… Kudos to @wesleyneelen @janbakker_ @fabian_bader @SantasaloJoosua
In the documentation for #EntraID roles, I was curious about this big “Important” box for the Application Administrator role because I know it’s here for security reasons as @_dirkjan showed 😉 (learn.microsoft.com/en-us/entra/id…) 👀 Let’s see if the part I highlighted is true!

Florian Roth @cyb3rops
180K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Florian Hansemann @CyberWarship
75K Followers 47 Following Father, Founder @HanseSecure, Pentesting, Student, ExploitDev, Redteaming, InfoSec & CyberCyber; -- Mastodon: https://t.co/KFSKYUN98M
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
mRr3b00t @UK_Daniel_Card
93K Followers 7K Following 真理的揭露者 Quis custodiet ipsos custodes fella in cyberspace #nafo undercover #FVEY Lovely Horse #fella #meme #farm #appreciator #cyber #specialist
Alh4zr3d @Alh4zr3d
19K Followers 283 Following Legal Criminal | Twitch cult leader | InfosecPrep founder | Lovecraft scholar | Soros mercenary | Spiritual cargo shorts wearer | Cthulhu fhtagn
ippsec @ippsec
111K Followers 350 Following
Grzegorz Tworek @0gtweet
30K Followers 1K Following My own research, unless stated otherwise. Not necessarily "safe when taken as directed". GIT d- s+: a+ C++++ !U !L !M w++++$ b++++ G-
DebugPrivilege @DebugPrivilege
37K Followers 2K Following Security “Researcher” | Former Microsoft MVP | All Tweets are my opinions and thoughts. Interested in Security, Debugging, and Troubleshooting.
DirectoryRanger @DirectoryRanger
31K Followers 100 Following This account assembles and disseminates information related to Active Directory and Windows security.
Mike Felch (Stay Read.. @ustayready
15K Followers 2K Following Pentester / Red Team | Hacking since Renegade BBS backdoors | Dev since vb3 | Content since '99-'03 ezines | Prior CrowdStrike / BHIS | In Christ's grip
Charlie Bromberg « .. @_nwodtuhs
13K Followers 648 Following Trying to hack the way we hack things 🏴☠️
Dr. Nestori Syynimaa @DrAzureAD
17K Followers 2K Following Principal Identity Security Researcher at Microsoft. Ex-Secureworks. (MSc, MEng, PhD, CITP, CCSK). And yes, opinions are my own ;)
Oliver Lyak @ly4k_
8K Followers 267 Following Yet another security researcher 🔦 Github: https://t.co/7WFOFz17KI
Vincent Yiu @vysecurity
27K Followers 202 Following Follow me for Cybersecurity #Thought #Leadership. Director Red Team. Help organizations safeguard their businesses from the bad guys.
Dirk-jan @_dirkjan
25K Followers 174 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
Ogeam @Ogeam1
5 Followers 99 Following
Print3M @Print3M_
41 Followers 50 Following Security Research (rather useless) & Programming. Proud father of https://t.co/BEDG5EUCGz Blog: https://t.co/leKJGz7MGu
Akshay Ambre @AkshayAmbre9
2 Followers 25 Following
나영욱(이태수/�.. @4fI2l6Kr7kOo3fQ
648 Followers 7K Following 우리 하나로 마트 점장 문공 입니다.서울중앙지법 민사합의12부 부장판사입니다.대통령 명예훈장입니다.대법관 상달 입니다.정신과 특작부대 사령관 입니다.하버드 의대 명예박사입니다.방송공사 명예회장입니다.대법원 초대 상임원장입니다.목민관 총판사입니다.세계 성결교회 상임 부목사입니다.
Sənan Rəhimli @rhlisna19
2 Followers 15 Following
Abes Shabib @4S4br
0 Followers 12 Following
TammyPitman @cFlAzhs8HYFd2
3 Followers 229 Following
███ ███ @WhitfieldsDad
10 Followers 149 Following Red + purple + ███ team at ███, former EDR and vulnerability scanner developer at Rapid7. Working on BAS + ███ + CTI + ███, ███ at ████ ███.
Electronicsseeker @libertarian108
24 Followers 2K Following
Timothy Wilson @Khemist_MK
177 Followers 348 Following @[email protected] // blogger // Homelab // Infosec Researcher
Harm Veenstra | MVP @HarmVeenstra
2K Followers 3K Following Microsoft MVP | #PowerShell Evangelist | Living apart together with @Eve_023 | Consultant | *Core | #Pixel7 | #Espresso | https://t.co/8Aes02OcHf
Thanks Always @iTimonPumbaa
9 Followers 615 Following
diarrhea_goat @diarrhea_goat
1 Followers 281 Following Systems eng by day, pentester by night. Sharing what I learn along the way and randomly bitching about IBD.
CaRLiTo ⋰·⋰✤ @crypt0xCarL
326 Followers 2K Following You look good today, much handsome ! $ORN $COTI $NOIA $GOVI $BLOK . Enjoy the ride and fasten your seat belts. Do Your Own Research.
signalblur📡🛸 @signalblur
68 Followers 390 Following Founder @ Signalblur Cyber Threat Intelligence, parked - find me on mastodon @ https://t.co/PDJPhsbMxK
Gatsby_tweet @gatsby_tweet
53 Followers 268 Following
rainbowdynamix @rainbowdynamix
56 Followers 273 Following red team stuffs || shadow wizard money gang member ||
Jason Graham @JasonSGraham
179 Followers 1K Following Christian, Husband, Father, Hacker. Opinions are mine alone.
BerkeleyNyi @Berkeley147
381 Followers 6K Following
Chaminda Kumara @kumaruwan17
87 Followers 2K Following
teio @teio1515599
17 Followers 162 Following
shirto cubher @cubher15531
22 Followers 184 Following
Daniel @DMakewea
1 Followers 1K Following
Poupou Micou @PoupouMicou
5 Followers 49 Following
Ezsecurity @Ezecurity
1 Followers 139 Following
Hermon Kidane @HermonK7
53 Followers 307 Following
pfremaux @pfremaux
22 Followers 499 Following
Taquine @taquine_
54 Followers 172 Following # ﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽﷽
mlecchaslayer156 @mlecchasla37448
110 Followers 3K Following
sthatrolls @sthatrolls
8 Followers 54 Following
Flash @gordonjwang
0 Followers 4K Following
Lauri @LauriKendaru
19 Followers 96 Following
DriveByte GmbH @drive_byte
35 Followers 73 Following Sleep well again and leave hackers no chance to begin with. We provide innovative and tailored cybersecurity services, for corporate, and SME sized businesses.
lolett84 @tiltdealer
117 Followers 842 Following
skander @skander6659
40 Followers 86 Following
c500 @c5008944
29 Followers 317 Following
Dave Kennedy @HackingDave
207K Followers 6K Following Founder @Binary_Defense @TrustedSec Co-Owner https://t.co/HQC75WhdJh. @WeHackHealth Podcast. Fam First/Hacker/CSO/USMC/Intel/Fitness. Motto: Make world a better place
Florian Hansemann @CyberWarship
75K Followers 47 Following Father, Founder @HanseSecure, Pentesting, Student, ExploitDev, Redteaming, InfoSec & CyberCyber; -- Mastodon: https://t.co/KFSKYUN98M
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
DebugPrivilege @DebugPrivilege
37K Followers 2K Following Security “Researcher” | Former Microsoft MVP | All Tweets are my opinions and thoughts. Interested in Security, Debugging, and Troubleshooting.
DirectoryRanger @DirectoryRanger
31K Followers 100 Following This account assembles and disseminates information related to Active Directory and Windows security.
Mike Felch (Stay Read.. @ustayready
15K Followers 2K Following Pentester / Red Team | Hacking since Renegade BBS backdoors | Dev since vb3 | Content since '99-'03 ezines | Prior CrowdStrike / BHIS | In Christ's grip
Charlie Bromberg « .. @_nwodtuhs
13K Followers 648 Following Trying to hack the way we hack things 🏴☠️
Dr. Nestori Syynimaa @DrAzureAD
17K Followers 2K Following Principal Identity Security Researcher at Microsoft. Ex-Secureworks. (MSc, MEng, PhD, CITP, CCSK). And yes, opinions are my own ;)
Oliver Lyak @ly4k_
8K Followers 267 Following Yet another security researcher 🔦 Github: https://t.co/7WFOFz17KI
Vincent Yiu @vysecurity
27K Followers 202 Following Follow me for Cybersecurity #Thought #Leadership. Director Red Team. Help organizations safeguard their businesses from the bad guys.
Dirk-jan @_dirkjan
25K Followers 174 Following Hacker at @OutsiderSec. Researches AD and Azure (AD) security. Likes to play around with Python and write tools that make work easier.
rootsecdev @rootsecdev
24K Followers 1K Following Security Consultant @TrustedSec | Military grade meme poster, researcher, cloud penetration tester, voider of warranties. My thoughts are my own.
mpgn @mpgn_x64
17K Followers 234 Following Flibustier du net ̿ ̿̿'̿'\̵͇̿̿\=(•̪●)=/̵͇̿̿/'̿̿ ̿ ̿ ̿ Podcast Hack'n Speak @hacknspeak / https://t.co/GyACSFg9mw
Matt Zorich @reprise_99
11K Followers 2K Following @Microsoft GHOST 👻 | https://t.co/HWozKuj5IQ | Tweets are my own
Josh @passthehashbrwn
8K Followers 344 Following Adversarial Simulation at IBM, tweets are mine etc.
sn🥶vvcr💥sh @snovvcrash
10K Followers 441 Following Sr. Penetration Tester / Red Team Operator @ptswarm :: Author of Pentester’s Promiscuous Notebook (https://t.co/rL1sv5A2R7) :: He/him :: Tweets’re my pwn 🐣
Harm Veenstra | MVP @HarmVeenstra
2K Followers 3K Following Microsoft MVP | #PowerShell Evangelist | Living apart together with @Eve_023 | Consultant | *Core | #Pixel7 | #Espresso | https://t.co/8Aes02OcHf
erm4 @er1cm4
19 Followers 71 Following
Keanu Nys @RedByte1337
199 Followers 47 Following Offensive Security Lead @ Spotit. Creator of GraphSpy
Cory Wolff @cwolff411
7K Followers 233 Following Director, Offensive Security @ risk3sixty | Core team member @RedTeamVillage_ | Technologist | Builder and breaker of all the things. Tweets are my own.
clearbluejar @clearbluejar
987 Followers 294 Following Research | Learn | Write | Code | Repeat | https://t.co/aMkHjDdfTq #patchdiffing | Author of #ghidriff | Security Researcher @clearseclabs
Jean-Michel Besnard @jmbesnard_maz
305 Followers 510 Following Partner - Cybersecurity Audit & Advisory - Grant Thornton France
Ashish Gupta @ashishrocks
253 Followers 573 Following VP, Cloud Security Operations, Information security. https://t.co/n5VhvhYfdu
Mike @MySnozzberries
511 Followers 2K Following I Build-Break-Repeat, AWS, Azure, MS, Cisco, InfoSec https://t.co/eN8iK5IMuL
Kay Daskalakis @KayDaskalakis
54 Followers 145 Following 🛡️ Visually helping to spread the message #DefenceInDepth starts with #Identity @SpecterOps - Tweets, satire and harmless opinions are my own.
Daniel Mayer @dan__mayer
556 Followers 492 Following https://t.co/K4CorT895N Adversary Simulation @specterops
Mohit Gupta @_Skybound
92 Followers 67 Following Principal Security Consultant @ WithSecure focusing on all things AWS and Kubernetes More active on Slack so find me there
drak3hft7 @drak3hft7
2K Followers 390 Following OSCP | eCPPT | CRTP | Bug Hunter & Penetration Tester | Synack Red Team Member | Top 30 Yeswehack
David O'Brien (he/him.. @david_obrien
6K Followers 2K Following Cloud Security diagrams automatically created for MSP / MSSP & consultants. 9 year former MS Azure MVP, pilot, dad. #cloudsecurity #azure
Jean Marsault @iansus
1K Followers 377 Following Red-Team & DFIR @WavestoneFR YoloSw4g CTF Opinions are my own
elkement @elkement
1K Followers 1K Following Physicist, engineer (cyber security, energy). Creating physics-inspired art and Found Poetry.
Daniel @0x64616e
481 Followers 139 Following
Lukas Klein @RantaSec
38 Followers 166 Following
Forrest Kasler @FKasler
245 Followers 370 Following Climber, Penetration Tester, Code Junkie, Malware Enthusiast @specterops
itay.io @ity_krk
154 Followers 997 Following cybersecurity all-arounder | low code enthusiastic | creator of https://t.co/mDid1l28hR | https://t.co/gCB4ydvg9b (acquired by Zscaler)
Edznux @Edznux
123 Followers 422 Following
nodauf @nodauf
459 Followers 503 Following Offensive security enthusiast | Interested in malware dev, AD, Windows, ...
Rémi GASCOU (Podalir.. @podalirius_
7K Followers 557 Following Security Researcher & Speaker | Microsoft Security MVP | Developer of security tools | Coach of the CTF team @OteriHack 🎬 https://t.co/QaAENc4NcY
Melvin langvik @Flangvik
9K Followers 465 Following Team Lead @kovertno , previously Red Team @TrustedSec , terrible creator of InfoSec content 📹Opinions are my own and not the views of my employer.
Jason Ostrom @securitypuck
886 Followers 254 Following Instructor and Author @SANSInstitute | Blue & Red Team | GoLang & Terraform| Builder of things | Husband & Father | #NHL #NFL | @[email protected]
Michael Liben @MLiben
294 Followers 973 Following Security and Identity-minded Technologist. Frequently outspoken.
Mike Marable @mike_marable
2K Followers 2K Following The guy that shipped #ConfigMgr 1805 TP at #MMSMOA 2018.
Paul Winstanley - MVP @SCCMentor
5K Followers 560 Following SCCM Solutions Ltd - https://t.co/t0fP65rZvu #Consultant, #SCCM #MSIntune #Windows10 #ConfigMgr #Windows365. Microsoft Enterprise Mobility MVP. #MEMPowered
Johann Rehberger @wunderwuzzi23
3K Followers 629 Following Hacking neural networks so that we don’t get stuck in the matrix. Red Team Director @ Electronic Arts. Entrepreneur. Builder and Breaker. Opinions are my own.
Vadims Podāns 🇱�.. @Crypt32
731 Followers 41 Following PKI Consultant @PKISolutions Microsoft MVP: Cloud and Datacenter Management
Francois Dufour @frfrdufour
455 Followers 183 Following Marketing Partner & CMO @ Decibel. CMO Coach. Ex Twilio and LinkedIn. Board Member @ Madkudu. Father, kitesurfer, swimmer. Writes about Marketing & PLG.
Sam Mak @sam_ps_mak
123 Followers 56 Following I'm a Senior Product Manager at Microsoft working on Identity Security.
Shannon McHale @_shannon_mchale
1K Followers 711 Following Red Team @ Mandiant/Google 👩🏻💻 Focused on hacking and protecting clouds. Presenter at DefCon, ShmooCon, WiCyS, and WiConnects. Ex-@RITSECclub President
Carsten @0xcsandker
2K Followers 132 Following Security enthusiast, Likes Windows Internals & AD In case twitter implodes: https://t.co/O5CSoJnrIK
Billy Oppenheimer @bpoppenheimer
117K Followers 127 Following writing/research assistant to @ryanholiday | my newsletter: https://t.co/uq7u9HbTfQ
Patrick Gray @riskybusiness
32K Followers 2K Following Host of the Risky Business® podcast. Guests by invitation only. Bsky: https://t.co/xxk90HocUF
Microsoft Mechanics @MSFTMechanics
147K Followers 402 Following Why, How & When to use current and forthcoming Microsoft Tech. Hosted by Microsoft Director @DeployJeremy & colleagues. An official @Microsoft video series.
Aaron Guilmette @drunknerdpro
125 Followers 142 Following Trust me--I'm a consultant. My tweets don't necessarily reflect the opinions or positions of my employer. https://t.co/FszwjI0E5V
A:\leksandar🌩🐚N.. @alexandair
5K Followers 1K Following Mastodon: @[email protected] Microsoft Azure MVP, the co-founder of https://t.co/ow8N26r2yX
L’Theron @Ltheron308
80 Followers 162 Following Screaming into the void. Tolkien Nerd. Musician. Infrequent Streamer. Former Chef. Constant Reader. Gamer. LGBTQA+ Ally 🏳️🌈Black Lives Matter, He/Him
Hugow @hugow_vincent
471 Followers 852 Following Security researcher && cat memes. Climb/fly sometimes 🪂
Aanchal Gupta @nchlgpt
2K Followers 185 Following CVP & Deputy CISO (Microsoft) Happy to discuss anything related to security, privacy, compliance, gardening, & hiking (nchlgpt =full name without vowels)Published part 2 of Manual LDAP Querying. This blog covers additional topics like user account control, password attributes, domain trusts, and more. posts.specterops.io/manual-ldap-qu…
10 years ago @strandjs asked me to come work at this small pentesting company called Black Hills Information Security. It is one of the best decisions I've ever made. For a decade I've had the privilege of hacking organizations with some of the coolest people on the planet.…
This is such an awesome writeup, but it's missing one thing - remediation steps Some AD admins may know how to fix these issues, but it's fair to assume some do not. I'd also highly recommend using PingCastle by @mysmartlogon as it audits most of this and more. Thread time!
Top 16 Active Directory vulnerabilities found during pentests (detailed post) #infosec #pentest #pentesting #hack #hacking @DirectoryRanger infosecmatter.com/top-16-active-…
Here is how we have implemented the golden certificate and ADCS ESC3 abuse narratives in BloodHound 🔎🐕
In Part 2️⃣ of the ADCS Attack Paths in BloodHound blog series, @Jonas_B_K explores some of the new edges introduced with ADCS support in BloodHound and how we have incorporated the Golden Certificates and the ESC3 abuse technique. Read more! ⬇️ ghst.ly/49VzHSE
After 4 months of testing/peer-review and the PR being in draft, dacledit is now ready for official review and merge in Impacket 💪 This script can be used to read, write, remove, backup, restore ACEs in an object's DACL, see you soon when merged 😊 github.com/SecureAuthCorp…
@zaab_it If I need it to work reliably straight to Invoke-RestMethod - I dont need to verify or update modules on disperse systems and if the URI changes I can just change that line and move on.
It's a big day- @tifkin_, @0xdab0, and I are proud to announce that Nemesis 1.0.0 has landed! We have a ton of awesome new features and a streamlined installation, check out the details at posts.specterops.io/nemesis-1-0-0-… and the code at github.com/SpecterOps/Nem…
Last year I shared how to convert BloodHound JSON to PowerShell objects. Here's a proper function: ConvertFrom-BHJSON gist.github.com/martinsohn/1f3… Examples in this new 🧵
Exporting nodes in #BloodHoundCE and #BloodHoundEnterprise is easy - click the Export button and select JSON ⬇️ JSON is nice but I prefer PowerShell objects, so I simply run... 1/2
Nice if you want to play around with BH data inside PowerShell. Thx @martinsohndk for sharing this gem
Exporting nodes in #BloodHoundCE and #BloodHoundEnterprise is easy - click the Export button and select JSON ⬇️ JSON is nice but I prefer PowerShell objects, so I simply run... 1/2
I just published a blog and tool for the LSA Whisperer work that was presented at the SpecterOps Conference (SOCON) back in March. If you are interested in getting credentials from LSASS without accessing its memory, check it out! medium.com/specter-ops-po…
Heading to #MMSMOA next month? Make sure to add this session to your schedule. @_Mayyhem will be joining @TheWMIGuy & @TomDegreef to speak on how to secure your ConfigMgr environment & defend against publicly known attacks. Learn more ➡️ ghst.ly/4459csL #SCCM
Shoutout to @m4lwhere on this comprehensive guide to getting started in BloodHound Community Edition. Check out his blog post that covers setting up, collecting data, analyzing the data & providing value with that data. ghst.ly/3JlkvmO
If you want to get started with BloodHound CE, then I highly recommend reading this awesome blog post by @m4lwhere. It's a great resource to kickstart your journey! m4lwhere.medium.com/the-ultimate-g…
I understand the announcement was vague but this is a rapid situation that is unfolding. If orgs want quick answers to paths leading to tier 0 assets. Do both blood hound and azurehound. Map those paths out. Reset, protect, and defend therecord.media/sisense-data-b…
👋 Hello, Nashville! If you’re at #WiCyS2024 come by Booth 228 to chat with a few Specters and learn more about us.
I wrote a script to identify every TAKEOVER and ELEVATE attack in Misconfiguration Manager that can be run with Read-only Analyst privileges or higher in SCCM. Please share with your IT admins, defenders, clients, assessors, and friends in infosec! posts.specterops.io/rooting-out-ri…
@merill idk how to explain it but the way you record demo videos is so aesthetically satisfying that i think you should be on the Windows UI team or something.
🥳 🎉 Folks, @fabian_bader, @Thomas_Live & I are excited to launch Maester today after working on this over many long nights & weekends! Maester is an open source, test framework that you can set up in minutes to test & continuously monitor your Microsoft security config 🧵⬇️
Heading to #WiCyS2024 this week? We are too! Stop by Booth 228 to meet our team and learn more about us and how you can become a Specter.