Ido Veltzman @Idov31
I'm a security researcher that using this platform to share my projects and research. Opinions are my own. https://t.co/UiWgKq40sV linktr.ee/idov31 Joined March 2020-
Tweets188
-
Followers3K
-
Following37
-
Likes558
As you've noticed in the agenda of x33fcon, Nidhogg now has full integration to @checkymander's Athena and now it can be used with Mythic C2 infrastructure. The API available here: github.com/Idov31/Nidhogg… If you want to learn about this and more, make sure to watch my talk :)
As you've noticed in the agenda of x33fcon, Nidhogg now has full integration to @checkymander's Athena and now it can be used with Mythic C2 infrastructure. The API available here: github.com/Idov31/Nidhogg… If you want to learn about this and more, make sure to watch my talk :)
A simple reverse engineering writeup, defeating a username and serial key check! medium.com/@syncwithali/d…
From knowing Austin and his work, anyone that will hire him will have a 10x researcher on their team. Extremely talented and creative person.
From knowing Austin and his work, anyone that will hire him will have a 10x researcher on their team. Extremely talented and creative person.
I'm pleased to announce that I will be giving my talk "Kernel Games: The ballad of offense & defense" in @x33fcon this year, I hope to see you all there 🥳
Modern implant design: position independent malware development. A small blog post on how to design "modern" malware with features like global variables, raw strings, and compile-time hashing. 5pider.net/blog/2024/01/2… Repo: github.com/Cracked5pider/…
The documentation of all features is complete and can be viewed in: github.com/Idov31/Nidhogg… In the documentation there are usage examples, explanations and helpful information for users and for people that want to learn how certain feature is implemented. #infosec #CyberSecurity
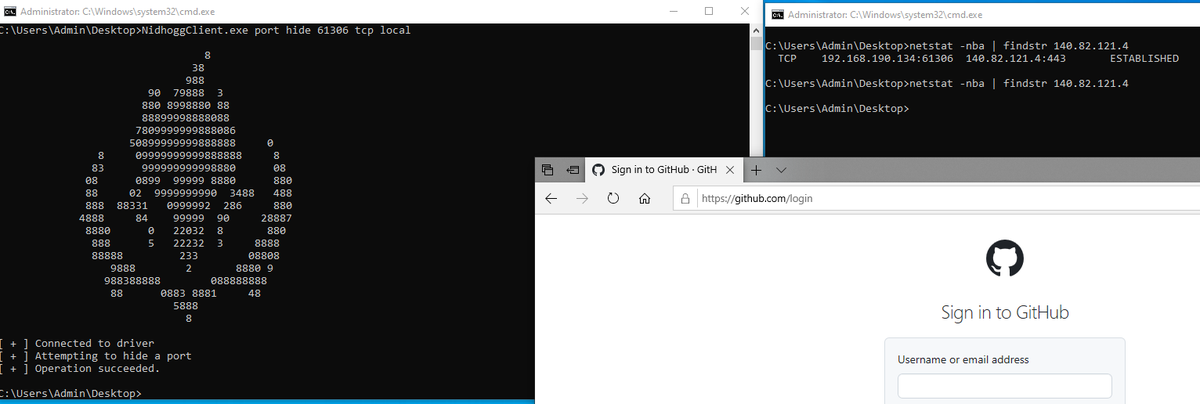
Another feature is completed :) Port hiding is added to Nidhogg, now you can hide connections by tcp (local or remote) or udp ports, already live in dev. github.com/Idov31/Nidhogg… #infosec #CyberSecurity
Due to the changes that happened with Nidhogg in the last months, I created a dedicated wiki that explains how the features work and how to use them. In the next weeks, I will add the documentation of all features. Everything will be available here: github.com/Idov31/Nidhogg…
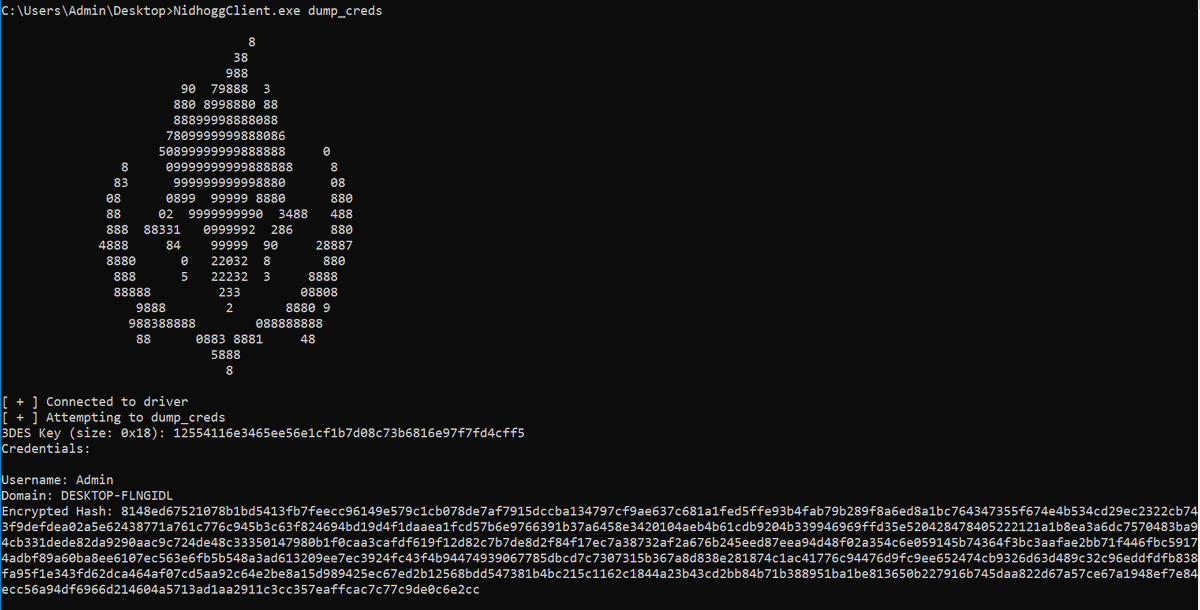
There was no update for a while and the reason being a massive bug fixes, feature checking and a new feature (fun fact: it is the 23th feature!). Now, you can use Nidhogg to dump credentials from LSASS! Go check it out: github.com/Idov31/Nidhogg… #infosec #CyberSecurity
I plan on releasing my stage 0 which started out as a plan to be a fully fledged framework but stopped at stage0, I genuinely had it private/sitting for a while and plan on stabilizing some code before deploying! I have no use case for it anymore.

klez @KlezVirus
6K Followers 668 Following Principal Cyber Security Consultant at Digital Trust Consulting Services, BSI - Opinions are my own
Justin Elze @HackingLZ
52K Followers 5K Following Hacker/CTO @TrustedSec | Former Optiv/SecureWorks/Accuvant Labs/Redspin | Race cars
Nikhil @Ox4d5a
15K Followers 1K Following Penetration Tester | i XCHG 0's 1's and do hacks | Red Team Sorcery https://t.co/6LUhkvNA77 | #eJPT | #OSCP | #CRTP | #CRTA | #CESP | #CRTE
Saad AHLA @d1rkmtr
7K Followers 369 Following d1rkmtr, Security researcher @AlteredSecurity, malware dev, kickboxer
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Austin Hudson @ilove2pwn_
6K Followers 34 Following Offline and looking for work. Living life happy and to its fullest . To reach me, I'm available @ [email protected]. GitHub: https://t.co/AihdCtKl5O
sn🥶vvcr💥sh @snovvcrash
10K Followers 438 Following Sr. Penetration Tester / Red Team Operator @ptswarm :: Author of Pentester’s Promiscuous Notebook (https://t.co/rL1sv5A2R7) :: He/him :: Tweets’re my pwn 🐣
Swissky @pentest_swissky
17K Followers 2K Following RedTeam | Pentest Author of PayloadsAllTheThings & SSRFmap https://t.co/w1ZLRqoafG
Filip Dragovic @filip_dragovic
6K Followers 1K Following
n00py @n00py1
13K Followers 955 Following Retweeter of InfoSec/Offsec/Pentest/Red Team. Occasional blogger/Independent security research. [email protected] on Mastodoge
Sh0ck @Sh0ckFR
7K Followers 1K Following Just another infosec guy in a red team - Punk à chien avec le QI d’Einstein 😅
Matthew @embee_research
12K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
Fawaz - بوجابر @q8fawazo
5K Followers 731 Following Penetration testing & Red team Senior Analyst مختبر اختراق @ بنك بوبيان
Luke H @3z57uff
116 Followers 225 Following
LonelyTesseract @lotesse
20 Followers 87 Following
22lrconsumer @22lrconsumer
0 Followers 55 Following
kevtrades @kextrades
1 Followers 4 Following
aubrey quarcoo @ahene90
305 Followers 5K Following Ghanaian orgin, Freelance C++ fixed income developer. Founder of GeorgeTown Analytics, using Erlang and Esper for messaging and Nosql. Web isolation
Ptkatz @ptkatz
1 Followers 59 Following
dorota @dorotaq
781 Followers 444 Following
sam @0xSJH
435 Followers 459 Following ⏚ security ♂He/Him ∫ Tweets are randomly generated and do not express opinions.
Czentye Levente @lordlewo
23 Followers 3K Following
Tana Tanita @CCMaldev
1 Followers 28 Following
diego perez gimenez @diegoperez2641
0 Followers 61 Following
binek86 @binek86
34 Followers 387 Following
bl4ck_W01f @0xd0s3nt
38 Followers 295 Following It's always easier to break things if we already know how to build them.
Melodi Vandalsen @MelVandals
84 Followers 5K Following
A3391gent @a3391gent
2 Followers 99 Following
Ozone777 @Moons7Ozone777
4 Followers 22 Following
Ingoa @rettiwt_ingoa
0 Followers 81 Following
ph01b3 @ph01b3
10 Followers 96 Following
Okan Kurtulus @okan_kurtuluss
702 Followers 350 Following Cyber Security Consultant | OSEP | OSWE | OSCP | eMAPT | TSE
ignacio @javiercaceres29
464 Followers 2K Following Developer,Continuos learner, Fan MotoGp, Futbol Y los buenos asados
JohnCMtwi @c_mtwi
4 Followers 121 Following
Dino Dunn @DinoDunn7
25 Followers 307 Following Po-ta-toes! Boil them, mash them, stick them in a stew.
Mohamed Hassan @mhassan252
13 Followers 292 Following Telecom Engineer | Cybersecurity enthusiast | Pentester
Bhaskar kannan @BhaskarKanan
137 Followers 149 Following
Rubbba @Rudbba
10 Followers 86 Following
bad2 @bad299376504
140 Followers 3K Following
Zero Day Equation🇵.. @ZeroDayEquation
28 Followers 1K Following Offensive Cyber Software Security Researcher | OSCP | OSEP | OSWE | OSWP | OSED | OSCE3 | OSEE | CRTO | CRTP | CISSP | #bugbounty #fuzzing #cybersecurity
stackHeaper @Stackmemory
0 Followers 59 Following Binary Exploitation student. Interested in Low level stuff RE-VR-Fuzzing-Assembly-C/C++ Programming
TD.Sbs @TDSbs
44 Followers 411 Following
memN0ps @memN0ps
2K Followers 219 Following Rust programming, hypervisor research & development, Windows internals, and reverse engineering. Member of @the_secret_club.
Myah Stropes @myah_strope
65 Followers 5K Following
roland @x1488z
0 Followers 7 Following
Black Swan @blackswan171
509 Followers 5K Following
35tur @35turM
29 Followers 84 Following
Daniel Ogwok @danogwok
363 Followers 1K Following I have a strong interest in Geography, History and Computer Science. Software Developer. Student.
Weakgod Chiu @pwn2ooown
87 Followers 903 Following Cybersec Enthusiast/Pwner. Not affiliated with pwn2own competition.
vx-underground @vxunderground
291K Followers 210 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
klez @KlezVirus
6K Followers 668 Following Principal Cyber Security Consultant at Digital Trust Consulting Services, BSI - Opinions are my own
x86matthew @x86matthew
17K Followers 344 Following C / asm / reverse engineering. Developer at @MDSecLabs. Other stuff at @the_secret_club
hasherezade @hasherezade
84K Followers 845 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Austin Hudson @ilove2pwn_
6K Followers 34 Following Offline and looking for work. Living life happy and to its fullest . To reach me, I'm available @ [email protected]. GitHub: https://t.co/AihdCtKl5O
Yarden Shafir @yarden_shafir
19K Followers 270 Following A circus artist with a visual studio license
LiveOverflow 🔴 @LiveOverflow
142K Followers 1K Following wannabe hacker... he/him 🌱 grow your hacking skills @hextreeio
Pavel Yosifovich @zodiacon
12K Followers 939 Following Developer, trainer, author and (sometimes) speaker. Founder at @trainsec academy.
Connor McGarr @33y0re
9K Followers 93 Following Software Engineer, Endpoint Protection (EPP) @CrowdStrike | Exploit Development and Vulnerability Research
Fawaz - بوجابر @q8fawazo
5K Followers 731 Following Penetration testing & Red team Senior Analyst مختبر اختراق @ بنك بوبيان
Gynvael Coldwind @gynvael
38K Followers 1K Following security researcher/programmer/director @ HexArcana Cybersecurity GmbH ⁂ @pagedout_zine ⁂ @DragonSectorCTF ⁂ https://t.co/ShG2c5As1K ⁂ ex-Google ⁂ he/him
eversinc33 🩸🗡�.. @eversinc33
3K Followers 571 Following purple hearted pentester learning malware development & kernel stuff
Dreg @therealdreg
3K Followers 405 Following Senior Malware Researcher, OS Internals, C/C++, assembler, reversing, forensics, hardware hacking, x86_64, AVR, ARM & PIC
Shawn @anthemtotheego
2K Followers 244 Following adversary simulation @ x-force red | offensive engineering lead | implant dev | work in progress | thoughts my own | https://t.co/eNspx7jLvm
Sinaei @Intel80x86
7K Followers 357 Following Windows Internals enthusiast, Interested in microarchitecture and low-level programming. A developer of @HyperDbg Debugger. DMs open... https://t.co/4DCPew9veX
Ali @syncwithali
58 Followers 172 Following
Satoshi Tanda @standa_t
7K Followers 359 Following Engineer & Trainer. My DM is open. https://t.co/hqylaDLtNv
Alex Matrosov @matrosov
18K Followers 2K Following 🔬Founder & CEO @Binarly_io, #codeXplorer, #efiXplorer, @REhints and "Rootkits and Bootkits" book. Previously worked at Nvidia, Cylance, Intel, ESET, Yandex.
Raul • 𝖙𝖍𝖊.. @theg3ntl3m4n
935 Followers 568 Following Security Researcher @beyondtrust | Ex-Red Team @mandiant @crowdstrike
noct @never_unsealed
249 Followers 68 Following 21 | INTJ-T | Firmware Security Research | IT-Security Student https://t.co/2B9z8eJVGL
HackSys Team @HackSysTeam
10K Followers 555 Following Vulnerability Research, Kernel Exploitation, Reverse Engineering, Exploit Development, Program Analysis, Malware Research, Web, Machine Learning
waldoirc @waldoirc
3K Followers 623 Following Trying to figure out how computers work. Figuring out SDR, IOT, and Mobile exploitation. https://t.co/rLZFU0dOBy
Mor Davidovich @dec0ne
2K Followers 304 Following Security Researcher | Red Teamer | Malware Developer
Dmytro Oleksiuk 💥 .. @d_olex
13K Followers 1K Following zero-fucks-given infosec research | contacts: https://t.co/AB3QnrPja0 | 🇺🇦 Ukraine needs your help to kill Ruϟϟian zombies: https://t.co/ihU9OLujfk
Ofir Krispin @OfirKrispin
29 Followers 237 Following
Alon Starikov @alonstarikov16
177 Followers 1K Following@Idov31 @_RastaMouse @checkymander Oh, I will enjoy this one! Superb work on Nidhogg! I keep it in my bookmarks to dive into kernel development one day and use your code for learning 😀
@Idov31 @_RastaMouse @checkymander Great job, looking forward to it 👊
🎉 Exciting news! 🎉 The agenda for #x33fcon has just been announced! 📢 Don't miss out on insightful #talks, engaging #workshops, and #networking opportunities. Who's presenting this year? Check it out: x33fcon.com/#!conference.md #cybersecurity #conference #workshops #training
Reverse engineering a simple binary to pass the correct password! It employs a simple XOR scheme, extracting the right password was a success! medium.com/@syncwithali/r…
If you've ever worked with HyperDbg, you probably know that everything in HyperDbg is treated as an event. This new debugger is designed to allow us to control the smallest unit in computers which is a clock cycle, so we can execute custom actions for each event (clock).
Soon we'll say welcome to our new family member, hwdbg. 🛠️⚙️🔲 Hardware Debugger, or #hwdbg, is a new class of event-driven chip debuggers that allows precise signal control down to the period of a single clock cycle. github.com/HyperDbg/hwdbg #FPGA #Chip #Hardware #Debugging
So @j00ru published two posts on Windows Registry; given that there were a lot of fixes in Windows Registry in recent months I expect these to be fun ;) googleprojectzero.blogspot.com/2024/04/the-wi… googleprojectzero.blogspot.com/2024/04/the-wi…
Did you know that LSASS has the ability to execute arbitrary kernel-mode addresses? I wrote a small proof of concept that allows administrators to execute unsigned code in the kernel if LSA Protection is disabled. github.com/floesen/KExecDD
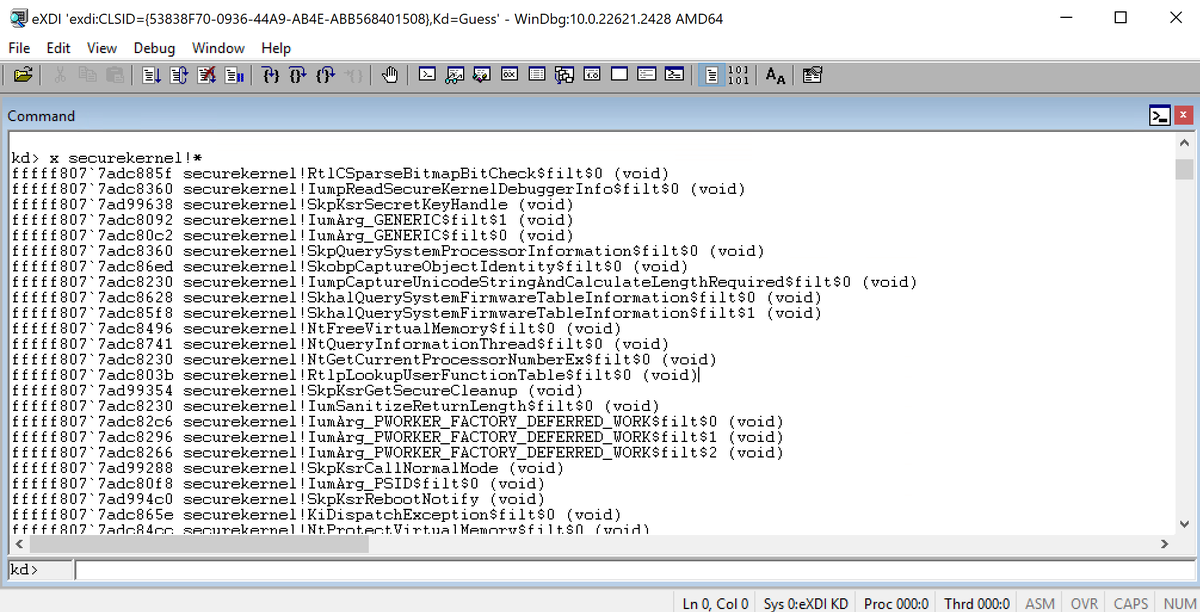
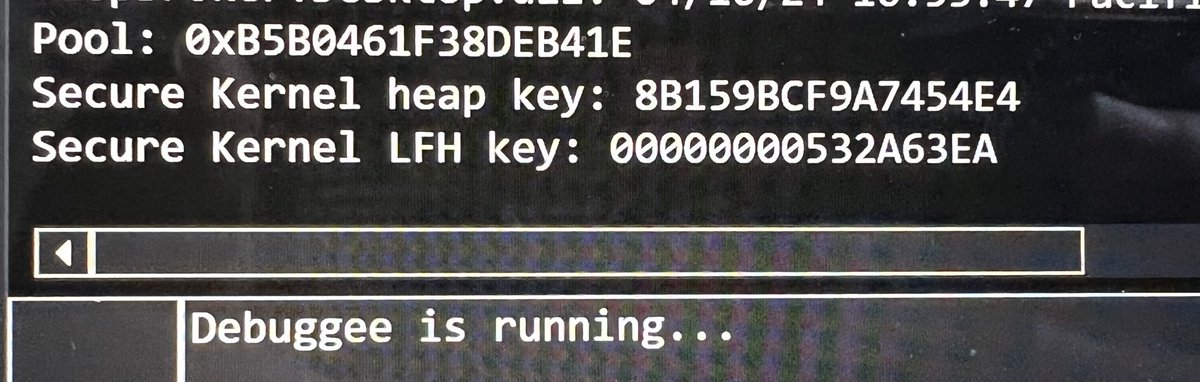
It took ~3 days but I got secure kernel debugging (mostly) working with LiveCloudKd (@gerhart_x) 🎉🎉🎉
A simple reverse engineering writeup, defeating a username and serial key check! medium.com/@syncwithali/d…
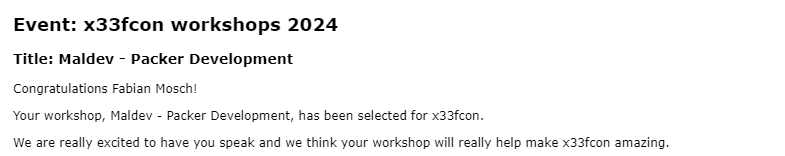
Looks like @ShitSecure and me are giving a workshop at @x33fcon this year👀We will be talking about packer development and help you to build your own packer for dropping malware in protected environments. Be there or be square🟥
Yeeah! 🔥🔥🔥🔥 Looks like @eversinc33 and I will give a Maldev Workshop at @x33fcon 2024! 😎Looking forward for that but also for this conference in general 🥰 Pirate Ship, we are ready 🏴☠️🦜
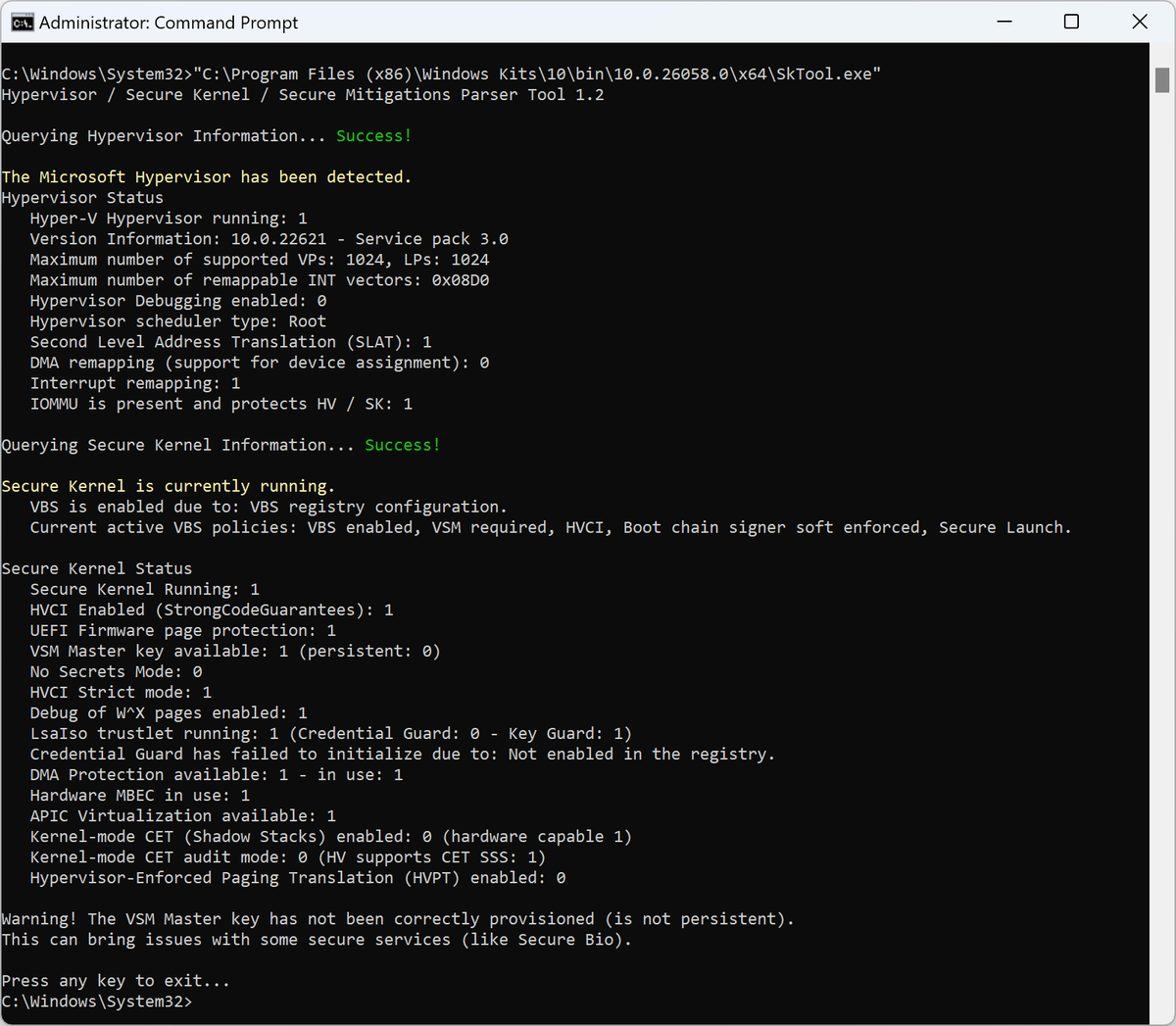
Shout out to @aall86 for building SkTool. The easiest way to find out what Hypervisor / secure kernel features are enabled on a system
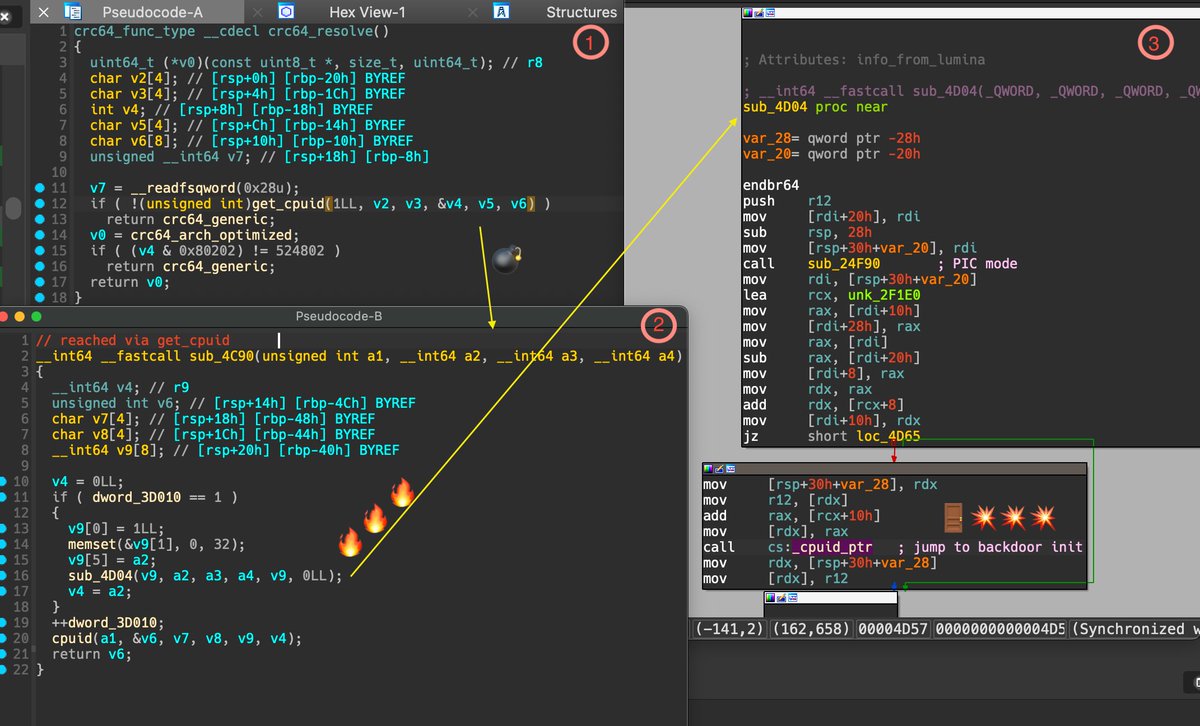
Proud of the team! We deployed generic IFUNC implantation detection in less than 24 hours with close to zero false positives. This demo shows our binary code intelligence engine in action by detecting the implantation of a backdoor in the crc64_resolve() function. This…
@antitree Our Transparency Platform has already deployed the detection. This specific case with such a backdoor implantation is tricky and possible only with deep code analysis for validation to reduce the FPs and not overwhelm security teams with alert fatigue.
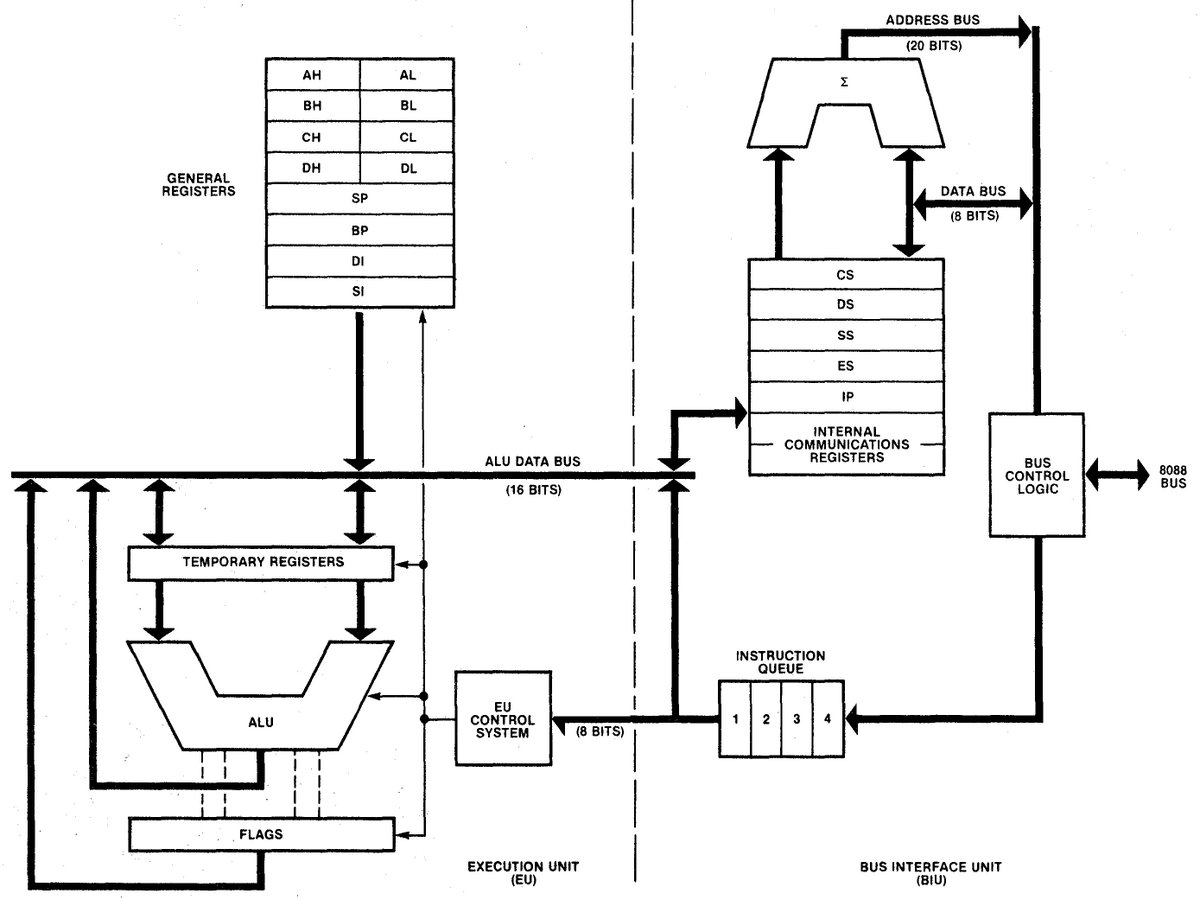
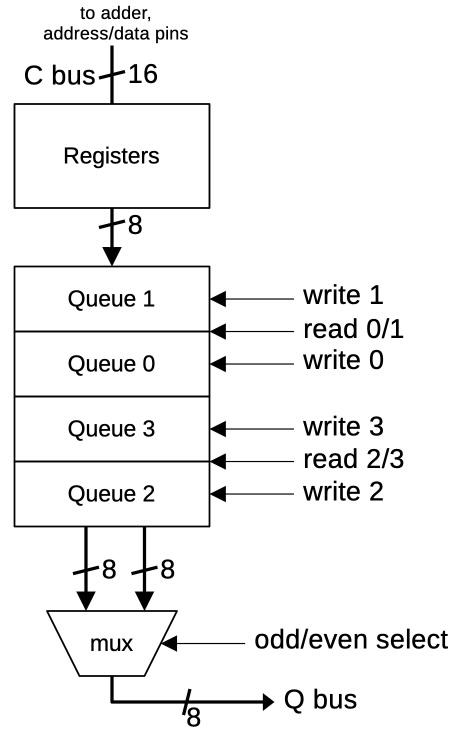
The Intel 8088 processor's instruction prefetch circuitry: a look inside : righto.com/2024/03/8088-p… credits @kenshirriff