3.11 - User Verification Methods 1) Utilize Discord IDs tinyurl.com/HowToFindDisco… 2) Check App Connections —if a user's Twitter account is linked to their Discord profile, it is highly likely that they are who they claim 3) Check servers where that user has an Admin or Team Role
3.12 - User Verification WARNINGS Discord Names can be copied nearly identically using ZALGO Text example: DrewBleam#0420 DrewBIeam#0420 ^ NOT THE SAME NAME The bottom version utilizes the Latin capital letter IOTA which is indistinguishable from "L" x.com/drewbleam/stat…
3.12 - User Verification WARNINGS Discord Names can be copied nearly identically using ZALGO Text example: DrewBleam#0420 DrewBIeam#0420 ^ NOT THE SAME NAME The bottom version utilizes the Latin capital letter IOTA which is indistinguishable from "L" x.com/drewbleam/stat…
3.13 - More User Verification WARNINGS Attackers will often create fake Twitter and Instagram accounts to attach to their imposter Discord Accounts. Always Verify...and then Verify again :)
4.0 - If it sounds too good to be true...it probably is ══════════════════ This lesson can be a bit overlooked because of the seemingly obvious nature...but realistically, too good to be true opportunities ACTUALLY do come up in web3... spotting the fakes 👇
4.1 - DM Scams Most fake opportunities originate in the DMs. You didn't actually win that giveaway that you never signed up for. You're being socially engineered.
4.2 - Airdrops These are prime Attack Vectors for web3 enjoyoors because we all love and NEED a good airdrop! But before you even pursue a new airdrop, head to Twitter, Discord, and some friends' DMs to see if they've heard about it yet. NEVER be the first to claim an airdrop
4.3 - JOB SCAMS This is a newer and more innovative method than the rest... The Job Scam leads victims to believe they are being recruited to perform a job or service to take down their 𝘼𝙬𝙖𝙧𝙚𝙣𝙚𝙨𝙨 for the attacker to strike. here are the common attack vectors 👇
4.31 - Game tester Leads the victim to believe that they are being hired as an early tester for an upcoming game release. Attacker will send the user to a malicious website that has them download the "Beta" which is actually a malware virus that can rek users in several ways.
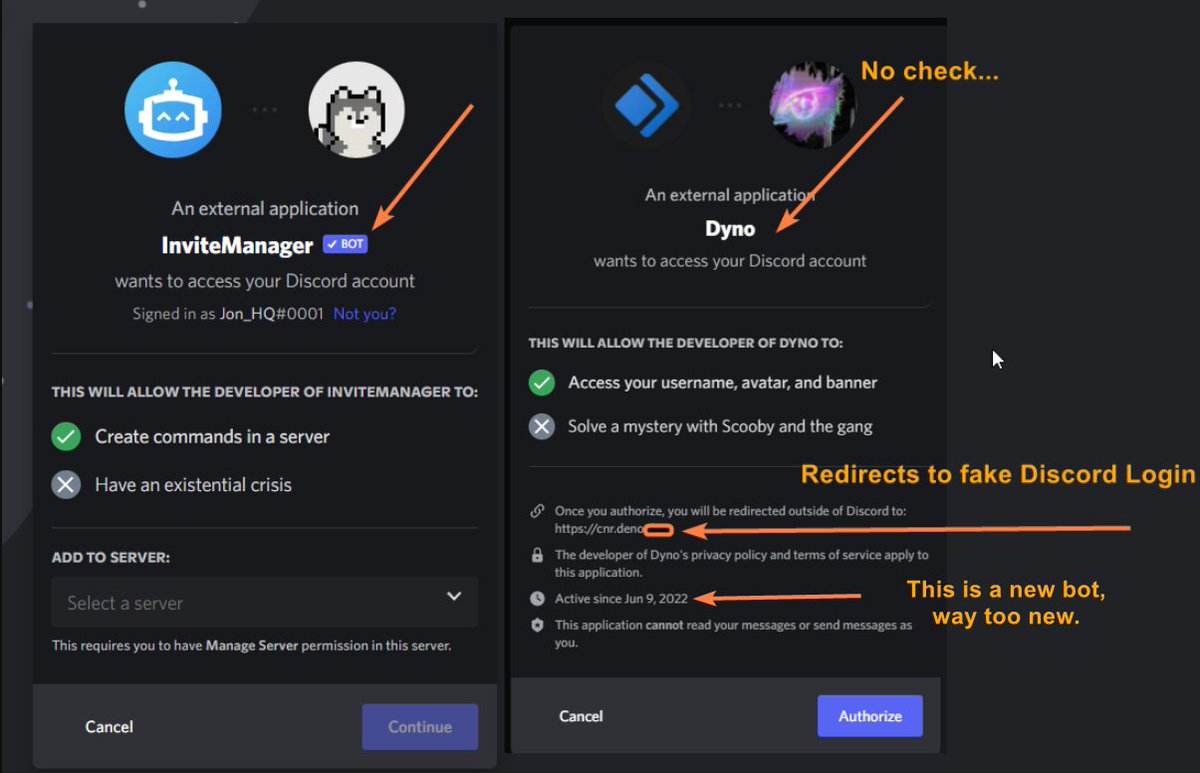
4.32 - Discord Moderator Job Scam Victim is invited to a server with a fake verification bot that leads them out of the Discord App to a site that intends to hijack their Discord Token. Great breakdown by @Jon_HQ: x.com/jon_hq/status/…
4.32 - Discord Moderator Job Scam Victim is invited to a server with a fake verification bot that leads them out of the Discord App to a site that intends to hijack their Discord Token. Great breakdown by @Jon_HQ: x.com/jon_hq/status/… https://t.co/ahb8tXO10i
5.0 - Social Engineering 101 ══════════════════ The primary tactic of any Phishing attack or Social Engineer is to make the victim feel a sense of Urgency or Panic. Training yourself to identify this feeling is a key principal of basic online OpSec.
5.1 - Social Engeneering Identification and Prevention digitalguardian.com/blog/social-en… Blog by @DigitalGuardian
6.0 - Conclusion ══════════════════ The overarching principals of safe Discord use are very much in line with general online Operational Security - the primary focus being the need for situational awareness when interacting online.