m4n0w4r @kienbigmummy
Work hard in silence , let success make the noise. kienmanowar.wordpress.com Joined October 2015-
Tweets4K
-
Followers5K
-
Following2K
-
Likes16K
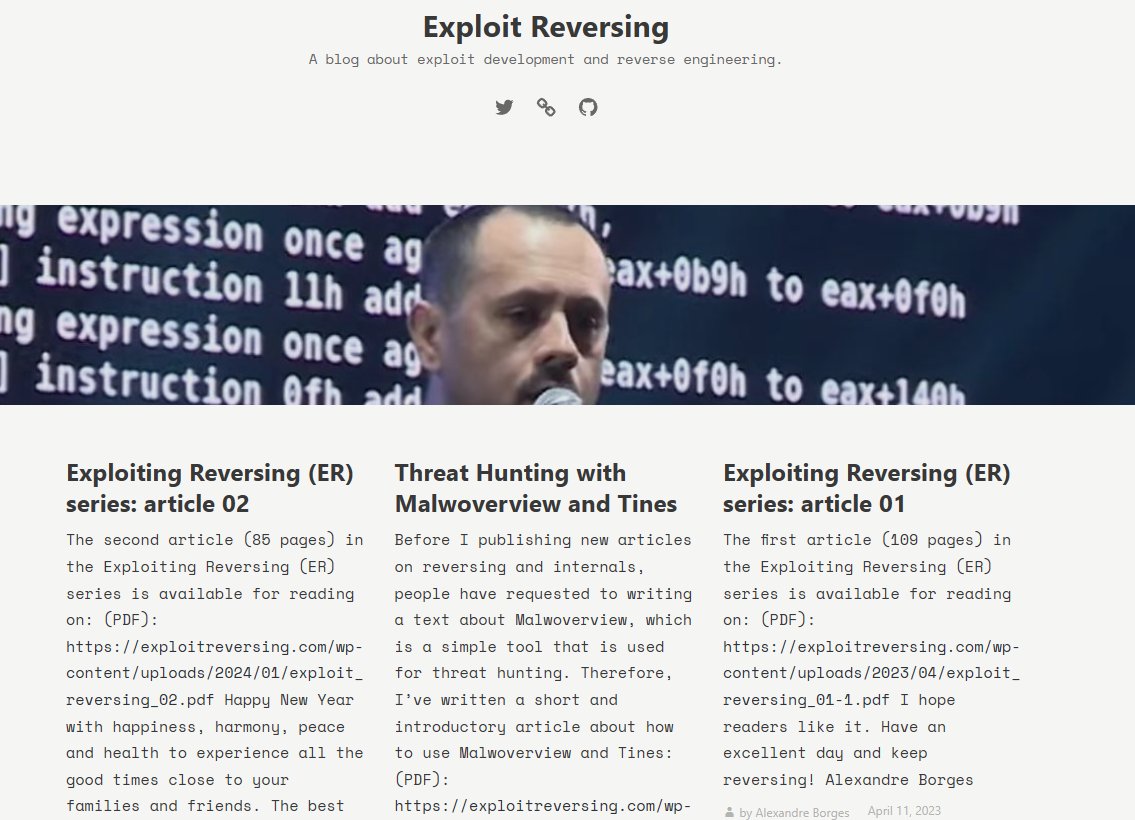
In our latest blogpost, @croco_byte presents an often overlooked AD attack surface related to OUs ACLs,with the release of a dedicated exploitation tool, OUned.py (github.com/synacktiv/OUned). synacktiv.com/publications/o…
Following the first part of the #APT29 #NOBELIUM attack, I am picking up from where we last off in the first part, shedding light on the latter components of the #malware infection chain and going through each in-depth. Your feedback is appreciated:) blu3eye.gitbook.io/malware-insigh…
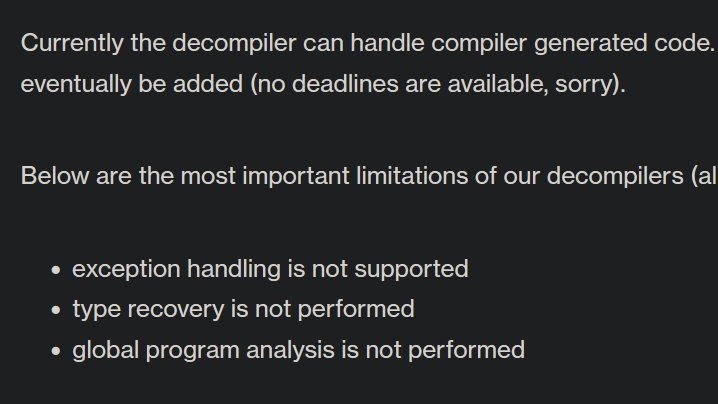
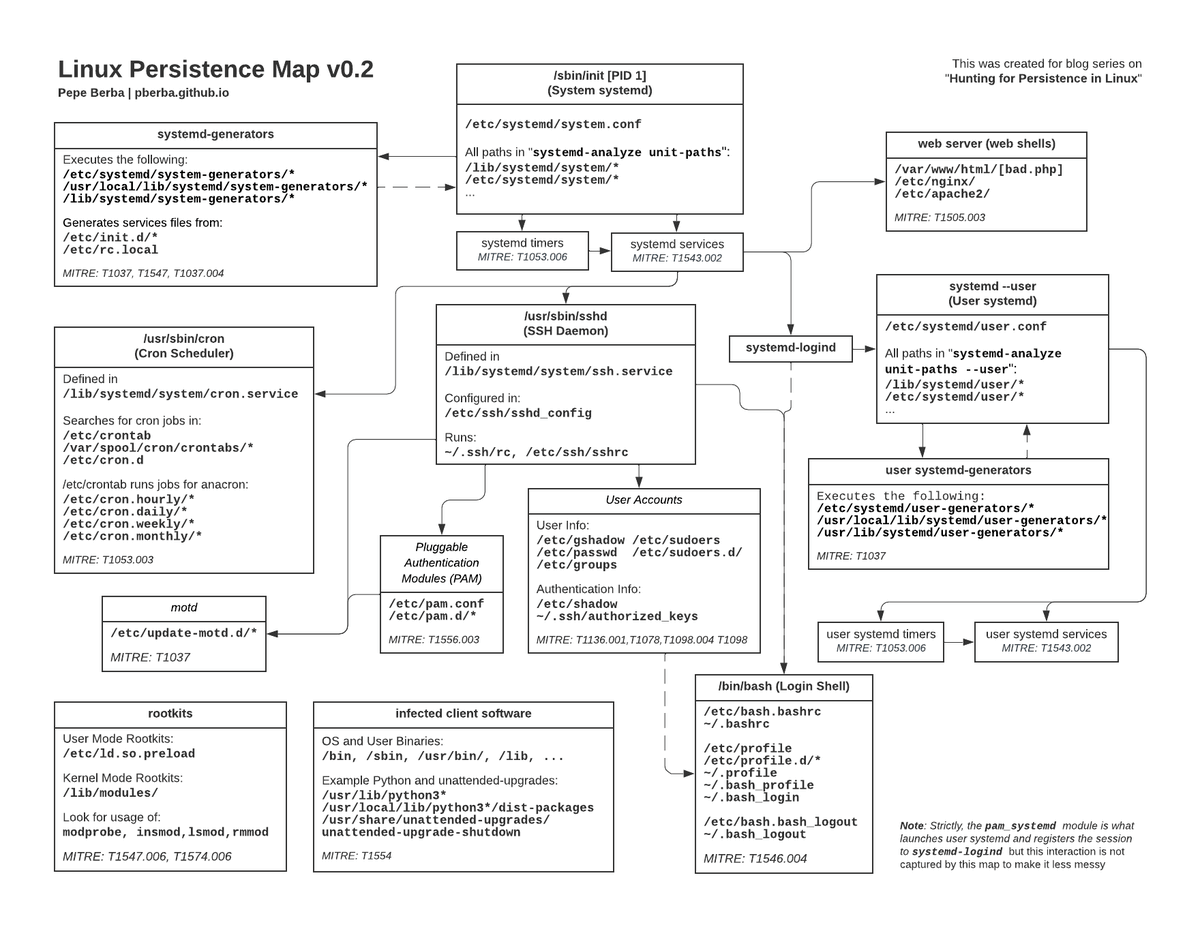
Some basic #IDA101 here: IDA does not support decompiling exception handlers; in other words, code that are within a catch block will not show up in the pseudocode view. A reminder that you should not blindly trust the pseudocode view. This is a very common anti-analysis method,…
Be alert that there is Qakbot being spread in the wild: 49220571574da61781de37f35c66e8f0dadb18fdedb6d3a1be67485069cfd4b0 Campaign: tchk08 ITW URLs on Virustotal: upd5[.]pro upd112.appspot[.]com
Tired of setting `OPCODE_BYTES = <NUMBER>` in ida.cfg/idauser.cfg but nothing happens? Edit 🔧 the default view under HKEY_CURRENT_USER\SOFTWARE\Hex-Rays\IDA\Desktops\$DIS$Default and tweak "inf":{"flat_dto":{ ... "opcode_bytes":<NUMBER> ...}} - Enjoy!🎉
🚨 New Blog Alert: Dive into the depths of WINELOADER malware! 🍷🔍 🎯 Key Takeaways: 1️⃣ Reversing Reveals by @tccontre18 : Our analysis uncovers intriguing technical insights in WINELOADER’s architecture! 🔧👀 2️⃣ WINELOADER Exposed: We breakdown its sneaky skills and control…
Did you know that importing tasks bypasses registry monitoring in Windows 10? I for sure didn't until I did a deep dive into scheduled task permissions. Check out ARC Labs' latest blog for tools, videos, and some other goodies #threathunt #threatintel binarydefense.com/resources/blog…
On March 25, the FBI released an indictment of APT31 hackers. We read it carefully to find new intel, and managed to connect a few dots (including about the RAWDOOR malware family). Full article and IOCs: harfanglab.io/en/insidethela…
Playlist of #JSAC2024 presentations in English now available here. Stay tuned for #JSAC2025 ! ^MT youtube.com/playlist?list=…
Our latest post has just gone live! In this one, we're looking at using Capstone Disassembler, Unicorn Emulation Framework, and Python to defeat encrypted stack strings within a Conti ransomware sample 0ffset.net/reverse-engine…
✍️🇻🇳My quick note about techniques employed by the threat actor in the phishing email to distribute #WarZoneRAT via #DBatLoader. kienmanowar.wordpress.com/2024/04/09/qui…
ThreatLabz has released an IDA plugin to deobfuscate the strings for previous versions of #Pikabot. Read our blog here: zscaler.com/blogs/security… The source code for the IDA plugin can be found here: github.com/threatlabz/pik…
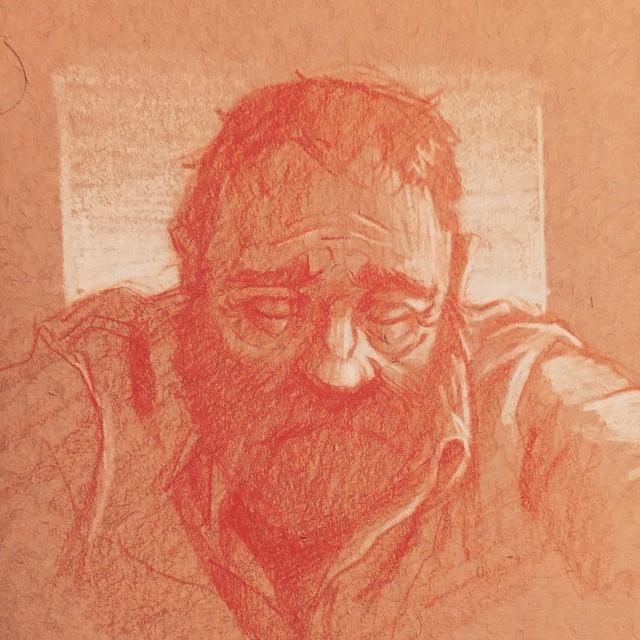
Chasse à la menace sur Linux, utiliser Sysmon et auditd et détecter des webshells. -> pberba.github.io/security/2021/…
From One to Now: The 30+ Years Journey of IDA Pro. Explore the evolution of IDA from its first version in the late 1990s to the present day in this video walkthrough. Watch here: youtu.be/tzJ5JjUW48s
Updated the Persistence checklist. There are 4⃣0⃣ persistence techniques which are backed up with an article ⤵️ github.com/netbiosX/Check… #redteam
Today, DHS released the Cyber Safety Review Board’s (CSRB) report summarizing the findings of its review into attacks associated with the 2023 Microsoft Exchange Online intrusion. Learn more here⬇️ cisa.gov/resources-tool…
#ESETResearch is releasing Nimfilt, an #IDAPro plugin to help reverse engineering #Nim malware – a language increasingly used by both the red-teaming community, and malware developers. Nimfilt demystifies Nim's custom mangling scheme. github.com/eset/nimfilt @barberousse_bin 1/3
If you like malware analysis and netflow threat intelligence connecting the dots between malware families, check out this technical analysis blog, a collab between @proofpoint and @teamcymru about Latrodectus malware proofpoint.com/us/blog/threat… (don't google lactrodectus 🕷️pictures)
[New Post] Persistence - DLL Proxy Loading pentestlab.blog/2024/04/03/per… #redteam

Florian Roth @cyb3rops
179K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Alexandre Borges @ale_sp_brazil
23K Followers 111 Following Vulnerability Researcher and Exploit Developer
Jiří Vinopal @vinopaljiri
8K Followers 428 Following Threat Researcher at Check Point @_CPResearch_ #DFIR #Reversing - All opinions expressed here are mine only. https://t.co/iWvwWF1AnN
Karsten Hahn @struppigel
22K Followers 703 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
20K Followers 236 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
Nicolas Krassas @Dinosn
121K Followers 734 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
blackorbird @blackorbird
28K Followers 601 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 569 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger | Stronger Together |
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon), https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Max_Malyutin @Max_Mal_
11K Followers 303 Following Threat Researcher, Blue Team, DFIR, Malware Analysis, and Reverse Engineering. “⚔️What do we say to God of malware, Not today⚔️”
Germán Fernández @1ZRR4H
28K Followers 577 Following 🏴☠️ OFFENSIVE-INTEL 🏴☠️ Cyber Threat Intelligence by Hackers | Security Researcher en https://t.co/rDrSxZASB3 | @CuratedIntel Member | 🥷🧠🇨🇱
Josh Stroschein | The.. @jstrosch
8K Followers 987 Following Reverse engineer at FLARE/@Google | @pluralsight author | 700K+ views on YT 😱 Find FREE resources below👇
hasherezade @hasherezade
84K Followers 843 Following Programmer, #malware analyst. Author of #PEbear, #PEsieve, #TinyTracer. Private account. All opinions expressed here are mine only (not of my employer etc)
Matthew @embee_research
11K Followers 1K Following Malware Researcher & Reverse Engineer | Creating and Sharing Educational Cyber Content
Kimberly @StopMalvertisin
16K Followers 631 Following Security Researcher | Cyber Threat / Malware Analyst | Ex Sr. Threat Analyst @ Proofpoint | Founder of Stop Malvertising
JAMESWT @JAMESWT_MHT
35K Followers 419 Following #Independent #Malware #Hunter #CyberSecurity #InfoSec https://t.co/KCFBJcHHcW
Tuan Anh Nguyen 🇻�.. @haxor31337
13K Followers 2K Following 28 y/o Bug Bounty Hunter and Red Teamer at Viettel Cyber Security. Brand Ambassador @Hacker0x01 - Researcher Spotlight @Bugcrowd
◯∴ @5o89
396 Followers 5K Following . ____ ∞ 0 123 369 567 9 ∞ ____ . N0 m0re HIR0$HIMA.☀️N0 m0re NAGA$AKI. N0 m0re M0AB・F0AB・Bi0l0gical WAR +α ∵☮️Ukraine・$yria・Yemen・$0malia・Gaza +α ∵🌻∴🌍🌏🌎311
Clove @CTW577
1 Followers 109 Following
Mohamed Ezzat @ZW01f
102 Followers 341 Following CS fresh graduate| Newbie Malware Analyst👾🔬 | RE & DF Enthusiast | Ctf player👨💻
sunnymelb @YogaroraYogesh
65 Followers 762 Following
Mr. 1nj3ct0r @cau_ca_98
9 Followers 93 Following Head of Information Security | Pentester | SRE | SecDevOps | System Security
Scott Lynch @packetengineer
3K Followers 5K Following Certified @SANSDefense Instructor | SECOPS/CERT Manager | Defcon BTV | Navy Vet | Sailor | Tweets Are My Own
Threat Entel @Entelligen
64 Followers 120 Following
Flash @gordonjwang
0 Followers 4K Following
K1nz @viet_kien16450
96 Followers 1K Following
r1n9w0rm @r1n9w0rm
88 Followers 69 Following
Dat Dora @DatDora
2 Followers 123 Following
baysao @baysao
208 Followers 2K Following
huyhai @lifeisnotsoez
12 Followers 204 Following
Alex Teixeira @ateixei
3K Followers 841 Following I design and build #SIEM content for a living. Editor at https://t.co/WIrKw7X1p5 #DetectionEngineering & Research, #ML #Stats x-Splunk
goutattack @chmod888
25 Followers 2K Following You've heard of Vans, the shoe company? Now introducing Shoes, the van company!
annie @AnnieAnnieyou12
2 Followers 374 Following
ً @VBrfTp7LS280861
0 Followers 388 Following
Abdulwahab Ibrahim @Abdulwahab75056
150 Followers 1K Following
Gökhan Boyraz @GBTeknikservis
95 Followers 421 Following
Lola Jackson @jackson_lo80540
24 Followers 129 Following
Yossi Yosefi @yyosefi
6 Followers 270 Following Entrepreneur, Mentor, Empowerment coach, Software engineer, IT & Cloud specialist. I like connecting with people and passionate about e-comm, marketing & AI.
Sehrish @Sehrish_Baloch1
7 Followers 73 Following
Mine @_quynhhmaii_
4 Followers 269 Following
Vu Tuan @tuanvd86
2 Followers 20 Following
Inaya @inayaK100897
2 Followers 60 Following
Smukx.E @5mukx
779 Followers 184 Following IT and Red Teaming, Malware and Reverse Engineer. 19 y/0. Currently learning some low level stuffs . Tweets are Personal ;)
Akhil Jose @Whenx0467
0 Followers 354 Following
Ameer Hamza @0xhamza
254 Followers 3K Following I have Diverse Interests: Interested in Global Politics Specific to Great Power Rivalry, Middle East, South Asia and OBOR. Interested in Information Security.
Cryptirin • Web 3 E.. @cryptirin
54 Followers 244 Following 🚀 Navigating the digital tides of Web3! 💎 Crypto trader by day, blockchain explorer by night.
Ramdhan @n0psledbyte
1K Followers 780 Following CTF @SuperGuesser (pwn), Security Researcher @starlabs_sg
Moggz @Moggznz
7 Followers 418 Following
wma @wma314
58 Followers 2K Following
vx-underground @vxunderground
289K Followers 207 Following The largest collection of malware source code, samples, and papers on the internet. Password: infected
Florian Roth @cyb3rops
179K Followers 2K Following Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇
Alexandre Borges @ale_sp_brazil
23K Followers 111 Following Vulnerability Researcher and Exploit Developer
Jiří Vinopal @vinopaljiri
8K Followers 428 Following Threat Researcher at Check Point @_CPResearch_ #DFIR #Reversing - All opinions expressed here are mine only. https://t.co/iWvwWF1AnN
Karsten Hahn @struppigel
22K Followers 703 Following Malware Researcher at G DATA. Ransomware hunter. he/him 🦔🌈🏳️⚧️
0xor0ne @0xor0ne
54K Followers 525 Following | CyberSecurity | Reverse Engineering | C and Rust | Exploit | Linux kernel | PhD | My Tweets, My Opinions :) |
ςεяβεяμs - м�.. @c3rb3ru5d3d53c
20K Followers 236 Following 💕 Malware Hunter Killer 💕 #binlex & #mwcfg Developer 📽️ YouTuber 👩💻 She/Her 💍@DravenSwiftbow Support my work 👇 ☕️ https://t.co/SfTI8uJa23
Nicolas Krassas @Dinosn
121K Followers 734 Following Head of Threat & Vulnerability Mgmt @ Henkel AG & Co. KGaA https://t.co/NC1orlKrW3
blackorbird @blackorbird
28K Followers 601 Following Peace and Love. Just Analysis/Hunter. #APT #threatIntelligence #Exploit Need Job
Thomas Roccia 🤘 @fr0gger_
25K Followers 2K Following Sr. Threat Researcher @Microsoft, Malware Warlock, Threat Intel, Python🧡- Former @McAfee_labs, Goon @Defcon, Creator of #UnprotectProject - Tweets are my own
MalwareHunterTeam @malwrhunterteam
211K Followers 36 Following Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.
Ptrace Security GmbH @ptracesecurity
53K Followers 883 Following Empowering IT Security Professionals through Hands-On Online Courses.
ESET Research @ESETresearch
32K Followers 30 Following Security research and breaking news straight from ESET Research Labs.
Unit 42 @Unit42_Intel
51K Followers 88 Following The latest research and news from Unit 42, the Palo Alto Networks (@paloaltontwks) Threat Intelligence and Security Consulting Team covering incident response.
Ali Hadi | B!n@ry @binaryz0ne
29K Followers 569 Following DFIR and Adversary Simulation | DFIR @ ProtonMail | Perfect Stranger | Stronger Together |
Binni Shah @binitamshah
131K Followers 176 Following Linux Evangelist, Malwares , Security Enthusiast, Philanthropist , Reformist , Jain. binitamshah at protonmail dot com
Michael Koczwara @MichalKoczwara
18K Followers 2K Following Founder @Intel_Ops_io Threat Intelligence, Adversary Infrastructure Hunting, Curated TI Feed (Coming Soon), https://t.co/vixTz8xKuF https://t.co/VQWaze6gaF
Max_Malyutin @Max_Mal_
11K Followers 303 Following Threat Researcher, Blue Team, DFIR, Malware Analysis, and Reverse Engineering. “⚔️What do we say to God of malware, Not today⚔️”
Mohamed Ezzat @ZW01f
102 Followers 341 Following CS fresh graduate| Newbie Malware Analyst👾🔬 | RE & DF Enthusiast | Ctf player👨💻
Scott Lynch @packetengineer
3K Followers 5K Following Certified @SANSDefense Instructor | SECOPS/CERT Manager | Defcon BTV | Navy Vet | Sailor | Tweets Are My Own
SandboxEscaper @big_polar_bear1
2K Followers 289 Following Fan of quadratic residues Former microsoft employee selling windows 0days.
Ben Barnea @nachoskrnl
1K Followers 370 Following Security Researcher @ Akamai. Windows vulnerabilities & internals research. Opinions and tweets are my own
Anthony Weems @amlweems
3K Followers 244 Following Cloud Vulnerability Research • The opinions stated here are my own, not those of my company.
alden @birchb0y
1K Followers 2K Following sr detection engineer @ huntress • re/malware enjoyer • macOS security
Cyber Team @Cyberteam008
843 Followers 51 Following Threat Hunting | APT Tracking | Malware Analysis | Darkweb Monitoring "Unity is Strength"
Smukx.E @5mukx
779 Followers 184 Following IT and Red Teaming, Malware and Reverse Engineer. 19 y/0. Currently learning some low level stuffs . Tweets are Personal ;)
IrishDeath @IrishD34TH
48 Followers 7 Following
Dave W Plummer @davepl1968
46K Followers 59 Following Hi! I'm Dave Plummer. You might remember me from such Windows components as Task Manager, Windows Pinball, Calc, ZIPFolders, Product Activation, etc. Cheers!
Ramdhan @n0psledbyte
1K Followers 780 Following CTF @SuperGuesser (pwn), Security Researcher @starlabs_sg
Billy @st424204
927 Followers 90 Following Security Researcher @starlabs_sg Pwn2Own Vancouver 2024,2023,2022,2021 Pwn2Own Austin 2023,2021
Manfred Paul @_manfp
4K Followers 280 Following Maths and cyber and stuff. Playing CTFs with @redrocket_ctf (and @Sauercl0ud). Pwn2Own Vancouver 2020..=2022, 2024. @[email protected]
bakki @shubakki
566 Followers 86 Following 18yo silly person | prominent shadow wizard money gang member | adversary emulation & offensive sillyware dev @ some company
Matt | HuskyHacks @HuskyHacksMK
17K Followers 95 Following Security researcher at @HuntressLabs. AT Thru Hiker 2023. not really using twitter anymore but still respond/answer questions from time to time 🏔🚶♂️🏔 ✌
_Ray @_RayRT
326 Followers 767 Following Senior Adversarial Engineer at Lares, Member of EVILCORP\Domain Fathers. https://t.co/SIwC7MLXmP
clearbluejar @clearbluejar
966 Followers 292 Following Research | Learn | Write | Code | Repeat | https://t.co/aMkHjDdfTq #patchdiffing | Author of #ghidriff | Security Researcher @clearseclabs
Thalium Team @thalium_team
2K Followers 0 Following https://t.co/Sx05emsfNz Groupe Thales / Lutte Informatique / recherche de vulnérabilités / développements Red Team
Anyfun @_Anyfun
295 Followers 1K Following
zhassulan zhussupov @cocomelonckz
1K Followers 108 Following I am a cyber security enthusiast, author. speaker, mathematician. Love my wife and kids. Author of MD MZ and Malfind books. Co-founder of MSSPLab
Miixxedup @Miixxedup
309 Followers 526 Following CTI at @Mandiant | Analyst at @TheDFIRReport | Security Intelligence, Automation and Innovation | Sourdough baker noob but a connoisseur anyway.
Joel Esler @JoelEsler
6K Followers 590 Following VP - Intelligence - ThreatSTOP | xCisco Talos | xPodcaster - SANS Podcast + Beers with Talos | Success comes in many forms.
monty @_montysecurity
470 Followers 197 Following senior threat hunter | wannabe malware analyst | adversary infrastructure tracking | @CuratedIntel member | DM me if I post bad intel
H!S3 @0x48215333
165 Followers 364 Following f*society | #BlueTeam | Love #MISP hate #Malware | in a complicated relationship with #Emotet, #QakBot,#PikaBot and #FluBot | *riendly
microv @MikyRov
189 Followers 515 Following Cyber Threat Intelligence Analyst @cluster25_io | Threat Hunting | Threat Intel | Malware Analysis
BlueEye @BlueEye46572843
168 Followers 538 Following Open to immediate work,reverse engineer & malware researcher who is interested in #APT research and targeted #malware.Views are my own.
Nat Sakdasak @mossdinger
69 Followers 70 Following I love reversing stuff. Still quite new to it though.
ZwClose @zwclose
738 Followers 55 Following
Claes Spett (.PrØÐi.. @J3rge
2K Followers 546 Following Programmer | Exploit Dev | Code Breaker | Backdooring Everything I Break!
jinmo123 @jinmo123
1K Followers 6 Following
journalctl -fau mix@d.. @mnixry
543 Followers 163 Following Developer, OSS enthusiast, anime fan, amateur CTF player, and sophomore in cryptography. | 开源恐怖分子,傻卵二次元,编程苦手。| CN/EN (B1)/DE (A1) 本當下手
Keowu @keowu
114 Followers 11 Following Maybe a Reverse & EDR Dev | Jesus Follower | My RE friends discord server: discord dot gg/fWhvHXtzxy | https://t.co/cPfrnwC6jN | I just know that idk anything
Sylvain HAJRI @navlys__
3K Followers 682 Following Passionate about #OSINT. Founder of @Epieos, a reverse email/phone lookup OSINT tool. @_leHACK_ #OsintVillage Founder, @OsintFr co-founder.
Rodrigo Branco @bsdaemon
12K Followers 3K Following Just an opinionated security researcher. Opinions are my own H2HC (Hackers 2 Hackers Conference)
Terrance DeJesus @_xDeJesus
575 Followers 977 Following Cybersecurity | Data Junkie | Python | #cybersecurity #threatdetection #threathunting #python - {opinions are my own}
Steve McKenzie @jarsnah12
1K Followers 380 Following I do security and stuff. All opinions are shared by my employer and are hilarious. https://t.co/SZOWltaTQI
Aurélien Chalot @Defte_
2K Followers 414 Following Hacker, sysadmin and security researcher @OrangeCyberdef 💻 Calisthenic enthousiast 💪 and wannabe philosopher 📖 🔥 Hide&Sec 🔥Seems like there is malware abusing GitHub attachments to create file links in legitimate repositories. Here's a funny example github.com/microsoft/MSRC… nothing special, but just seemed neat.
@SecurityAura @ippsec Have you watched OALabs Twitch?
I wrote a blog about Cobalt Strike beacon monitoring, Windows tokens and Kerberos persistence. Check it out sokarepo.github.io/redteam/2024/0…
In our latest blogpost, @croco_byte presents an often overlooked AD attack surface related to OUs ACLs,with the release of a dedicated exploitation tool, OUned.py (github.com/synacktiv/OUned). synacktiv.com/publications/o…
The Windows Registry Adventure part 1: googleprojectzero.blogspot.com/2024/04/the-wi… part 2: googleprojectzero.blogspot.com/2024/04/the-wi…
So impressed by @j00ru's Project Zero journey looking for security issues in the important and complex Windows registry. Great writeup outlining his thought-process... good lessons for us all! googleprojectzero.blogspot.com/2024/04/the-wi…
Hyped for this 👀
Heading to #RSAConference? Join this live presentation with Spence Hutchinson & Anna Pham as they shed light on the competing Malware-as-a-Service (MaaS) operations & offer insights into malware delivery trends (e.g., Google Ads). Reserve a seat here: bit.ly/3w1huVN
Following the first part of the #APT29 #NOBELIUM attack, I am picking up from where we last off in the first part, shedding light on the latter components of the #malware infection chain and going through each in-depth. Your feedback is appreciated:) blu3eye.gitbook.io/malware-insigh…
Malware Development Series => [+] Rc4 Shellcode Encryption: github.com/Whitecat18/Rus… [+] Rc4 Encrypted Shellcode Execution: github.com/Whitecat18/Rus… [+] Fixed APC Injection: github.com/Whitecat18/Rus… #maldev #rust #redteam #cybersecurity #infosecurity #infosec #security #Hacking
GitHub - Psmths/windows-forensic-artifacts: Handbook of windows forensic artifacts across multiple Windows version with interpretation tips with some examples. Work in progress! github.com/Psmths/windows…
I wrote a python script to decrypt the strings in #WineLoader . Check it out: gist.github.com/X-Junior/31e8f…
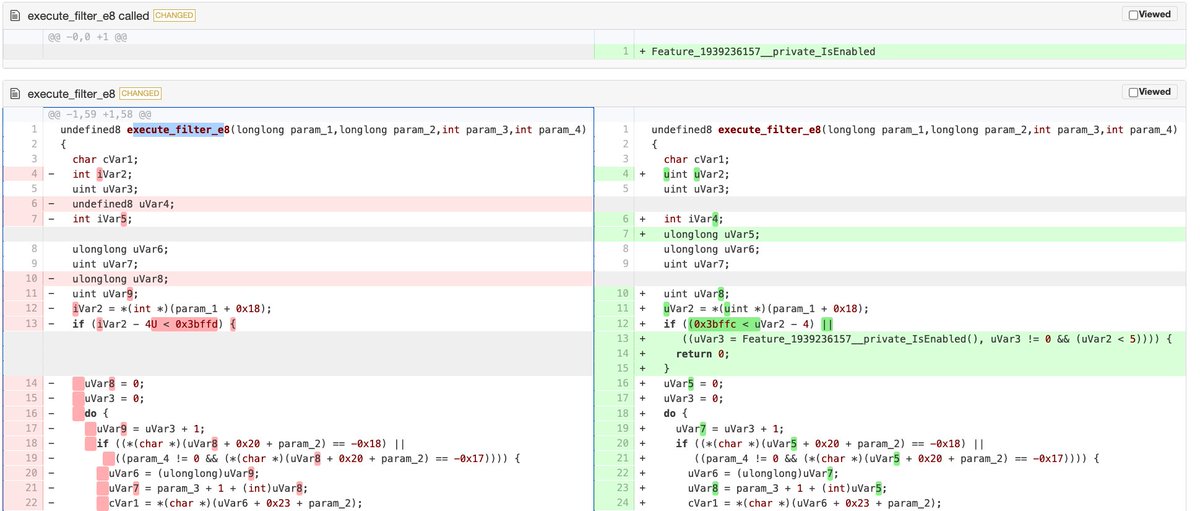
Looks like more libarchive CVE analysis is out from ZDI 👏 In my last Patch Tuesday post for CVE-2024-20696, I linked a diff that details the patch for CVE-2024-20697 explained in ZDI’s writeup. Seems to line up! 🧐 diffpreview.github.io/?9574f311b3d3f… 👀
CVE-2024-20697: Windows Libarchive Remote Code Execution Vulnerability -- The Trend Micro Research Team takes a deep dive into this recently patch bug. An attacker could exploit this bug by enticing a user into extracting a crafted RAR archive. zerodayinitiative.com/blog/2024/4/17…
This is an excellent guide for getting rid of Kerberos RC4. Highly recommend it. As the author puts it: "The risk of not taking action this area is greater than the risk of hardening your environment." techcommunity.microsoft.com/t5/core-infras…
ThreatLabz discovered a new backdoor that we call #MadMxShell targeting IT network administrators. Read our technical analysis here: zscaler.com/blogs/security…
Be alert that there is Qakbot being spread in the wild: 49220571574da61781de37f35c66e8f0dadb18fdedb6d3a1be67485069cfd4b0 Campaign: tchk08 ITW URLs on Virustotal: upd5[.]pro upd112.appspot[.]com
Tired of setting `OPCODE_BYTES = <NUMBER>` in ida.cfg/idauser.cfg but nothing happens? Edit 🔧 the default view under HKEY_CURRENT_USER\SOFTWARE\Hex-Rays\IDA\Desktops\$DIS$Default and tweak "inf":{"flat_dto":{ ... "opcode_bytes":<NUMBER> ...}} - Enjoy!🎉
Did you know that importing tasks bypasses registry monitoring in Windows 10? I for sure didn't until I did a deep dive into scheduled task permissions. Check out ARC Labs' latest blog for tools, videos, and some other goodies #threathunt #threatintel binarydefense.com/resources/blog…
🚨 New Blog Alert: Dive into the depths of WINELOADER malware! 🍷🔍 🎯 Key Takeaways: 1️⃣ Reversing Reveals by @tccontre18 : Our analysis uncovers intriguing technical insights in WINELOADER’s architecture! 🔧👀 2️⃣ WINELOADER Exposed: We breakdown its sneaky skills and control…
People ask why I haven't spoken at conferences in the last four years. In fact, my decision was made in 2022 for several reasons: 1. Due to the nature of my work (Windows/Hypervisors/Browsers exploitation), I cannot comment or present anything (and it isn't recommended). 2. The…
On March 25, the FBI released an indictment of APT31 hackers. We read it carefully to find new intel, and managed to connect a few dots (including about the RAWDOOR malware family). Full article and IOCs: harfanglab.io/en/insidethela…